How Invicti identifies out-of-date technologies
Using outdated technologies introduces serious risks and can pave the way for attackers to exploit vulnerabilities in order to induce harm to your system.
For many years, attackers targeted potential issues in the source code to hack your system. That, however, has become difficult in recent years because best practices in coding have matured. Now, the attackers began to focus on potential issues in third-party application codes and open-source integrations.
That means even if your application has no vulnerabilities, the application will not be secure if it uses even a single vulnerable external library. After all, a chain is only as strong as its weakest link.
- So, Invicti can track and report on issues to help you secure your third-party components, such as JavaScript libraries and off-the-shelf web applications, in your website.
- These issues can be out-of-date technologies or vulnerabilities.
- Invicti can identify these problems thanks to its vulnerability database package.
This topic explains the vulnerability database in general and how Invicti identifies out-of-date components in your application.
Vulnerability Database
Invicti is an advanced heuristic web application security scanner that also checks for known web application vulnerabilities.
To report known vulnerabilities, the scanner rests on its vulnerability database (VDB). This database is an integration point for the Invicti security checks, which serves as a data store of known technologies, their versions, and their vulnerabilities.
Invicti updates this database per week. Invicti Enterprise automatically updates its vulnerability database and adds these new vulnerabilities into your scan policy. So, there is no need to manually update it.
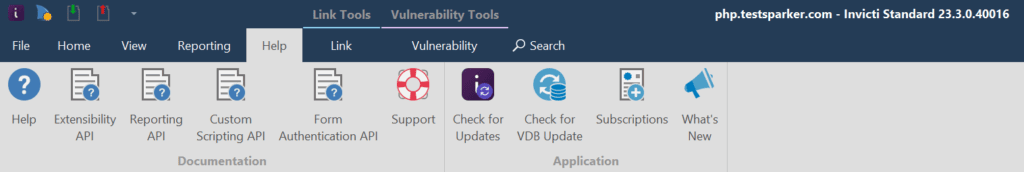
For Invicti Standard, whenever you open the program, it checks the database to see whether there are updates. In addition to this, from the Help tab in Invicti Standard, you can click Check for VDB Update to manually check for the updates.
How Invicti Identifies Out-of-date Version
There are three stages in detecting out-of-date version(s).
- Invicti first tries to identify applications, such as JavaScript libraries and web servers, in your system. It reports this issue as identified.
- Then, the scanner tries to identify the version of these applications. If successful, it reports this as a version disclosure issue.
- Following the version disclosure, Invicti queries its vulnerability database to see if there is a newer version. If so, it further reports this issue as an out-of-date version. In addition to reporting the out-of-date version, Invicti reports CVEs linked to this outdated application, if any.
Invicti also has a couple of security checks that are integrated (or directly working with the vulnerability database) to identify out-of-date issues. To clarify the dynamics, here are the vulnerability database integrated security checks:
Web App Fingerprint Check
Invicti, first, identifies web applications, then their versions. Following this, Invicti reports vulnerabilities in the web application(s) that the scanner identified. If Invicti matches the web application with more than one version, it reports them, merges them into a list, and updates the report’s confidence score regarding the matched version count.
The severity of the out-of-date vulnerabilities will be elevated to match the most severe CVE (Common Vulnerabilities and Exposures) reported for the identified version(s).

Javascript Libraries Check
Invicti extracts all of the JavaScript libraries while crawling the target. Then, the scanner tries to determine their versions. To do this, Invicti searches for some predetermined signatures on the source of the JS library or calls specific functions of these JavaScript that may expose the version information of the library itself. Then, it reports vulnerabilities, if any, in these libraries.
For more information, see Which JavaScript Libraries Do Invicti Scanners Detect?
Signatures Check
Invicti runs a couple of predetermined signatures against responses it received during the crawling stage. If this RegEx matches and Invicti identifies versions, this security check will communicate with the vulnerability database to report any known vulnerabilities.
If there is a newer version in the Invicti vulnerability database, it also reports an out-of-date issue. This security check mostly reports the application servers, programming languages, frameworks, etc.
VDB-Integrated Checks
In addition to the earlier security checks, proof-generating security checks also interact with the vulnerability database. For example, when SQL Injection checks extracted a proof containing technology and its version, it’ll also communicate with the vulnerability database to report any known issues related to the extracted technologies.
SQL Injection Check
As a web application security scanning tool, Invicti does not have direct security check(s) to identify database servers in your system.
Still, it reports these vulnerabilities in the following way:
- SQL Injection security check identifies a vulnerability in your system
- Invicti’s Proof Based ScanningTM technology exploits this vulnerability in a read-only and safe manner.
- Invicti extracts version information of the underlying database management system.
- Invicti reports this information as confirmed.
- Then, Invicti queries the Vulnerability Database to determine other vulnerabilities related to this version.
- Invicti also reports these related vulnerabilities, if any.

You can find the vulnerability database package if you installed Invicti Standard on your computer under C:\Users\[USER]\Documents\Invicti\Version Tables.