Online vulnerability scanner for web applications and APIs
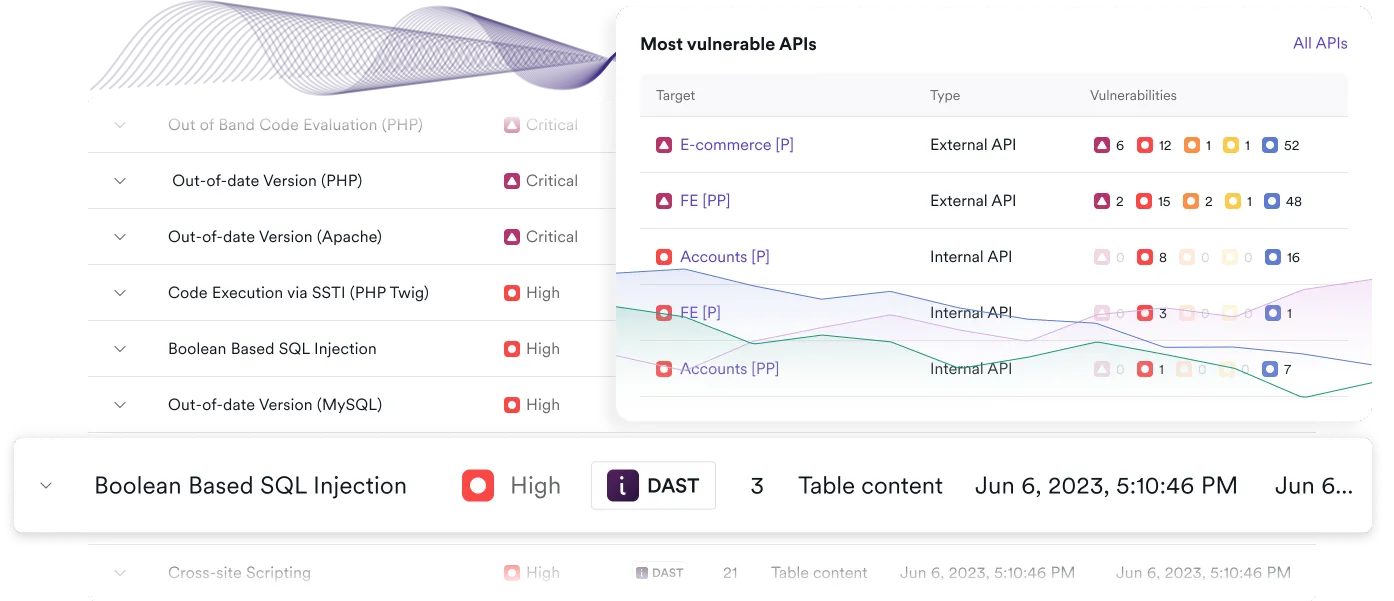
Scan your websites, web applications, and APIs with an online vulnerability scanner that focuses on real risk. Invicti combines dynamic application security testing (DAST) with proof-based scanning to help security teams identify and validate exploitable vulnerabilities, reduce noise, and prioritize what matters. As part of the Invicti Application Security Platform, your scan results feed directly into workflows for remediation, reporting, and continuous vulnerability management at scale.


G2 Awarded
Scan your full web attack surface across applications and APIs
An online vulnerability scanner is only as effective as the coverage it provides and the actionable results it delivers. Modern environments include far more than a single website – they span web applications, APIs, third-party components, and dynamically generated content.
Invicti continuously scans your externally reachable assets to detect vulnerabilities across your entire web attack surface, including:
- Web applications, including JavaScript-heavy single-page applications
- API endpoints and services that power modern architectures
- Authenticated areas using supported authentication methods such as SSO
- Internet-facing assets across both in-house and third-party environments
- Common CMS platforms such as WordPress and others
The scanner performs automated security checks for a wide range of issues, including OWASP Top 10 vulnerabilities like SQL injection, XSS, and RCE, web server misconfigurations, and outdated software that may expose your organization to security risks. Vulnerability scanning on the Invicti Platform includes a runtime SCA feature to flag the use of open-source components with known vulnerabilities (CVEs).
With dynamic testing that works regardless of underlying technologies, Invicti provides an outside-in view of your running applications – the same perspective malicious hackers have – so you can identify real exposure across both web apps and APIs.

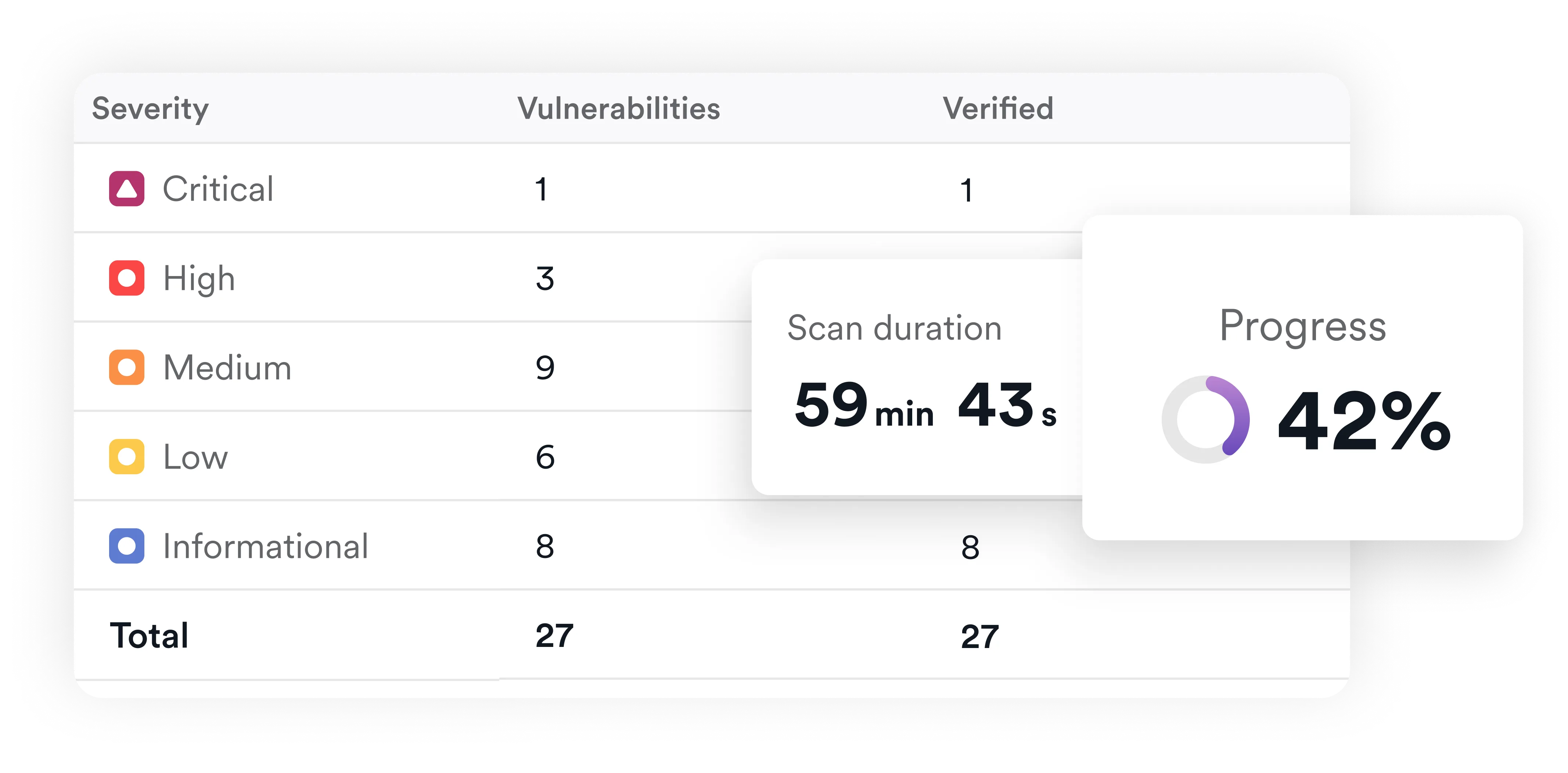
Cut through scanner noise with validated vulnerability results
Traditional online vulnerability scanners often generate large volumes of findings that require manual verification. This slows down remediation and makes it harder to focus on real risk.
Invicti addresses this with proof-based scanning, which safely validates many common vulnerabilities by demonstrating exploitability. Instead of relying solely on pattern matching, the scanner provides evidence-backed scan results that help teams distinguish between theoretical issues and real, actionable vulnerabilities.
This approach helps you:
- Reduce time spent triaging false positives
- Focus on vulnerabilities that can actually be exploited
- Provide developers and security teams with clear, actionable findings
- Improve confidence in your vulnerability detection and testing results
- Support security assessment requirements for compliance with ISO 27001, PCI DSS, SOC 2, DORA, NIS2, and other security standards and regulations
By prioritizing validated vulnerabilities, your security and development teams can move faster and spend less time chasing noise – and more improving overall security posture.
Integrate online vulnerability scanning into your SDLC and AppSec workflows
The value of an online vulnerability scanner comes from how easily it fits into your development and security processes. Invicti is designed to integrate directly into DevSecOps workflows, enabling continuous testing and faster remediation.
With built-in integrations and automation, you can:
- Trigger scans automatically from CI/CD pipelines
- Send verified vulnerabilities directly to issue trackers such as Jira
- Retest fixes as part of your development workflow
- Coordinate remediation across teams with shared visibility
As your needs and environments grow, scan results from DAST, API testing, and other security tools are centralized, correlated, and managed within the Invicti Application Security Platform to support broader cybersecurity and vulnerability management efforts. This gives teams a unified way to track, prioritize, and manage security vulnerabilities across applications and APIs while maintaining a strong focus on validated risk.
FAQs about online vulnerability scanning
An online vulnerability scanner is a SaaS-based tool that tests websites, web applications, and APIs for security issues by interacting with them over the web. Web vulnerability scanning is a type of dynamic application security testing (DAST) that analyzes running applications from the outside to identify issues such as cross-site scripting (XSS), SQL injection, misconfigurations, and many more.
An online vulnerability scanner is typically delivered as a cloud-based service that you can access on demand, while DAST refers to the underlying testing approach. In practice, most modern online web vulnerability scanners use DAST to test running applications and identify exploitable vulnerabilities as part of a broader vulnerability assessment process, and you will often see them referred to as DAST tools.
Yes, but effectiveness depends on API-specific capabilities. Modern online vulnerability scanners should be able to test API endpoints as well as web applications, but legacy tools designed for website security struggle with API-specific testing. The Invicti Platform includes dedicated API discovery and testing functionality to maximize coverage across the entire application attack surface.
Proof-based scanning is an Invicti technology that validates many vulnerabilities by safely demonstrating they can be exploited and providing proof. Having evidence that an issue is real eliminates uncertainty and reduces the need for manual verification, so teams can prioritize fixing confirmed vulnerabilities over investigating large numbers of potential issues.
Any organization that develops, operates, or manages websites, web applications, or APIs should use an online vulnerability scanner. Regular scanning is essential for identifying and fixing new vulnerabilities in environments that change frequently due to ongoing development and deployment.
An online vulnerability scanner complements penetration testers and automated pentest processes (including AI pentesting), but does not fully replace them. Automated scanning provides continuous coverage and helps identify common vulnerabilities quickly, while penetration testing offers deeper security assessments of complex attack scenarios.
No. A web vulnerability scanner focuses on application-layer vulnerabilities in websites, web applications, and APIs. Network scanners are designed to identify open ports, services, and infrastructure-level issues. Both serve different purposes and are often used together in a broader set of security tools.
You should only scan systems that you own or have explicit permission to test. Unauthorized scanning of any websites, applications, or networks can be illegal and may be treated as a cyberattack in some jurisdictions.
Focus on fixing real risk with Invicti’s web security scanner.