WEB APPLICATION SECURITY TESTING FOR TECHNOLOGY & SOFTWARE
Secure your web applications with the only AppSec platform that truly scales
It doesn’t matter how many web apps, sites, and APIs you have. You can secure them all with Invicti.
Trusted by technology companies around the world






Automate everything
Save your teams thousands of hours each year by automating all the AppSec work that can possibly be automated.
Integrate anything
No other AppSec platform has more integrations than Invicti. Let developers take action on security with the tools they already use with 50+ integrations into:

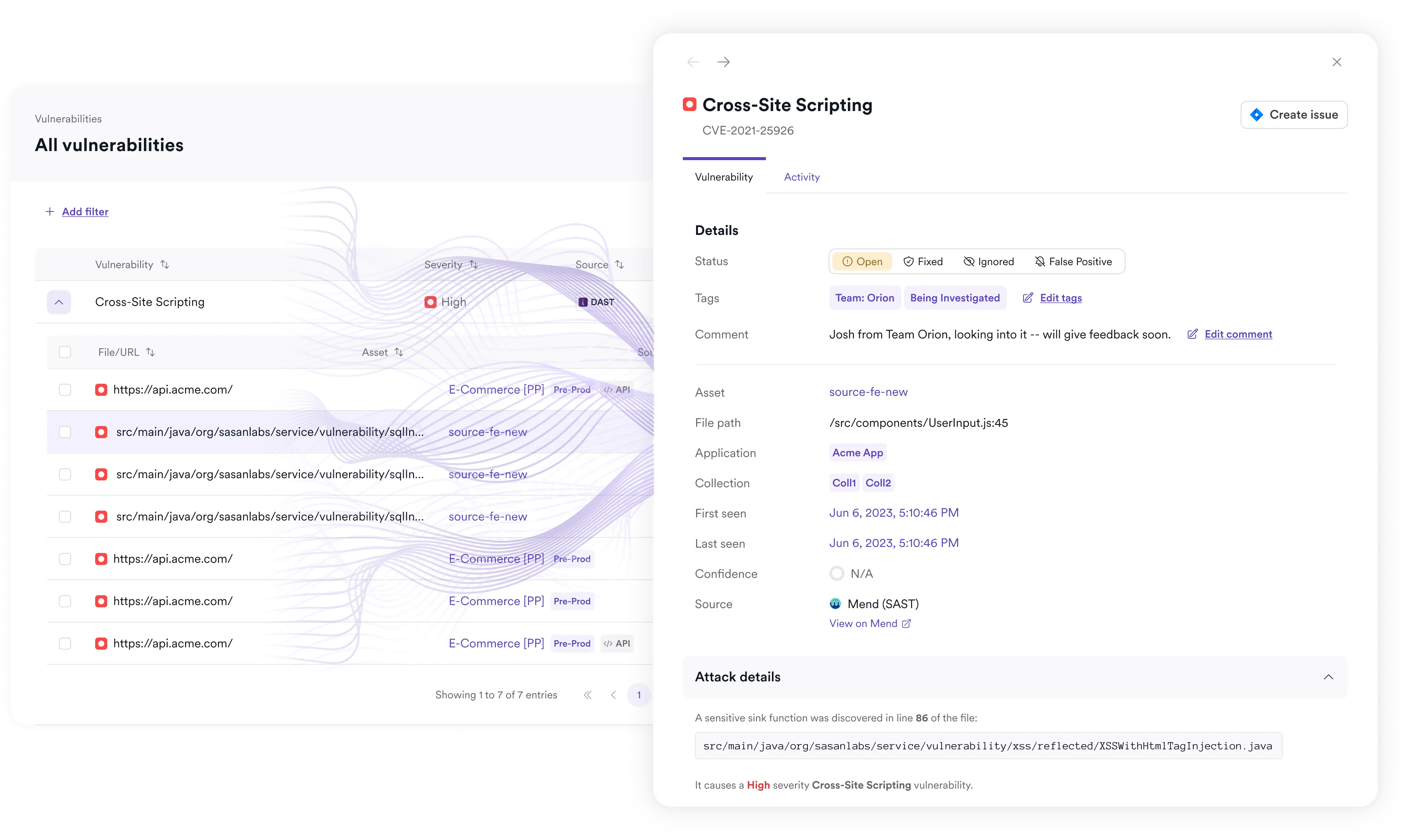
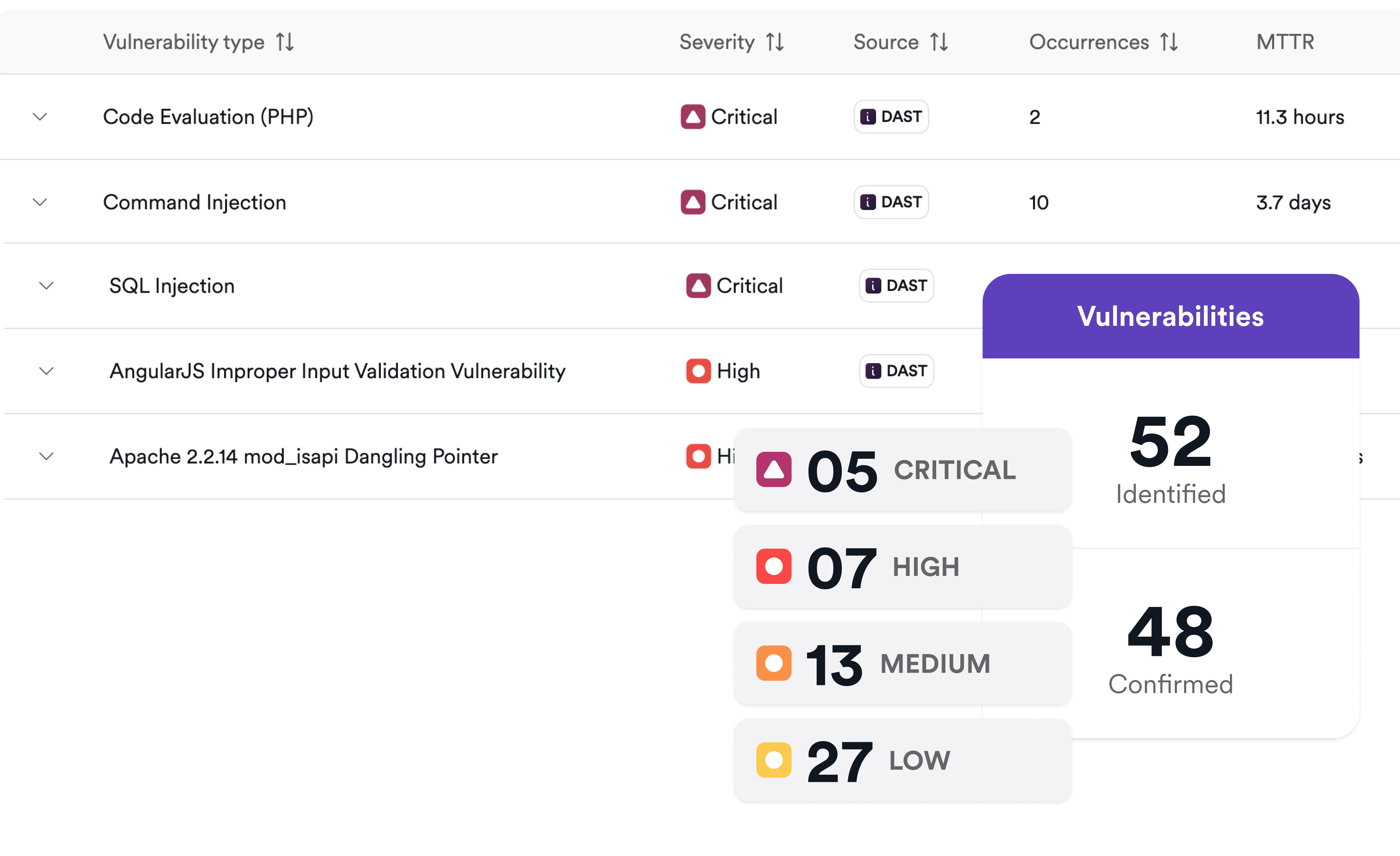
Detect more vulnerabilities. Spend less on bug bounties.
Get broader, deeper coverage with blended DAST + IAST and SCA. So you can detect more vulnerabilities with less reliance on manual pentesting and costly bounty programs.
GARTNER REVIEWS
Superior service
GET A DEMO
Your best path to scalable security