Invicti for Security Engineers
Focus on What’s Important
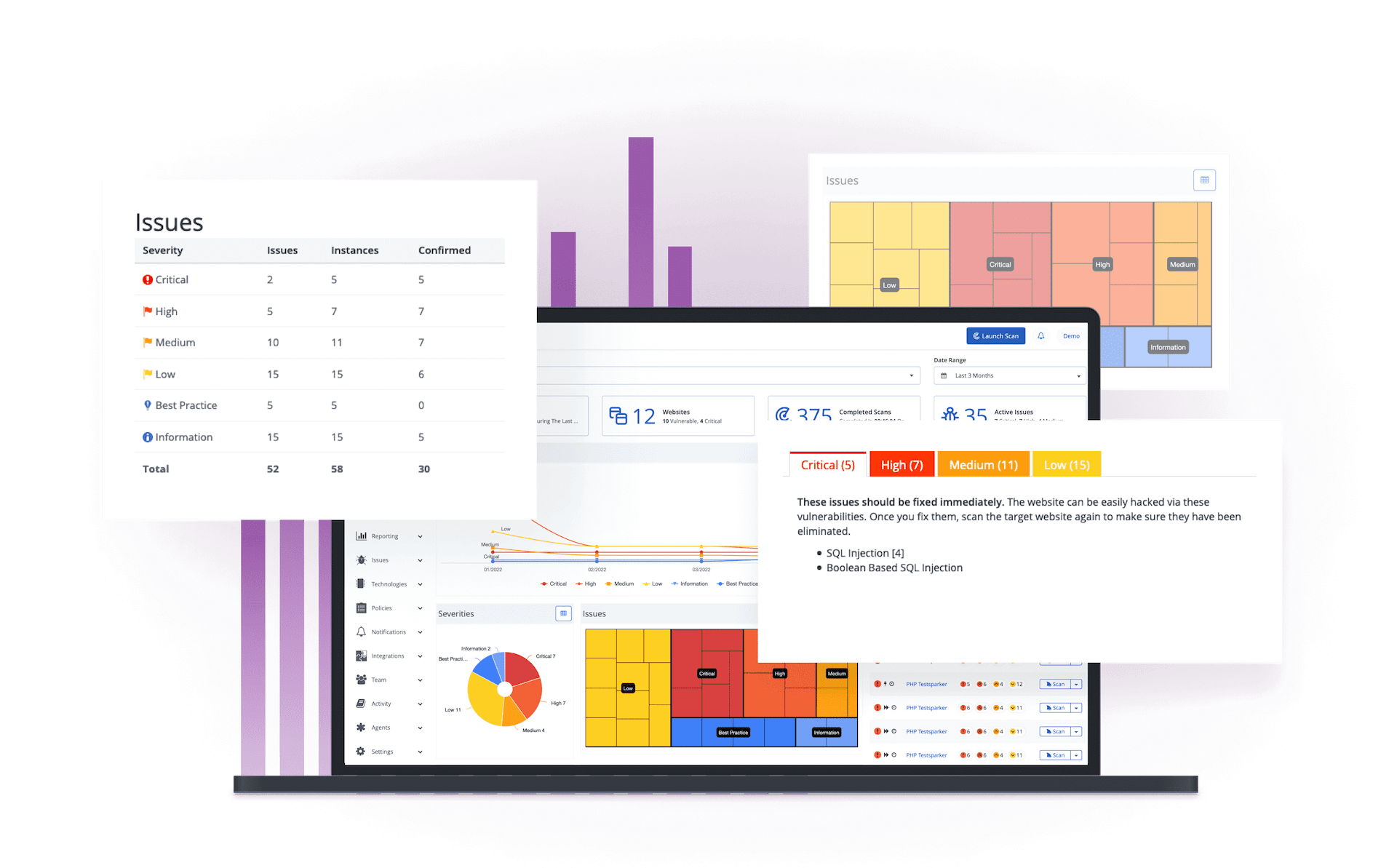
Invicti is a scalable, multi-user web application security solution with built-in workflow and reporting tools ideal for security teams. It’s available as a hosted and self-hosted solution and can be fully integrated in any development or testing environment.

The software is an important part of my security strategy which is in progress toward other services at OECD. And I find it better than external expertise. I had, of course, the opportunity to compare expertise reports with Invicti ones. Invicti was better, finding more breaches.
Senior Analyst, OECD

More Time for Hacking
Why spend hours finding and confirming ordinary bugs? Invicti not only scans everything for you but it also generates proof of exploit for every vulnerability that it finds, so you don’t have to. With the mundane out of the way, you can spend your time digging deep into more interesting subjects, for example researching new attack vectors.
No More Ghost Hunting
One of the most annoying tasks for a security engineer is trying to confirm an inexistent bug that is reported by an automated scanner. It takes a lot of time and causes a lot of frustration because it is much harder to prove that there is no bug than to find one. Invicti’s engine reports only vulnerabilities that it can prove, so you don’t need to worry about false positives.


Working with Other Tools
Invicti’s extensive import, export, and integration capabilities let you use it with many other solutions of your choice. For example, you can work together with your favorite manual tools to be able to follow up on results acquired from your own research or to dig deeper into issues that Invicti finds. If you prefer, you can also automate and integrate it to work completely in the background.
Trusted by Companies Like








“Invicti are not just another vendor from where we purchase any other software, they are like business partners.”
Jade Ohlhauser, CTO
RPM Software Uses Invicti to Ensure their Online Service Offering is Secure
As a cloud-based software developer and provider, RPM Software is responsible for the sensitive data their customers store on their solutions, hence they cannot afford to take web application security lightly…
Featured Security Engineers Content
Web Security
This whitepaper is part of a three-part installment covering a wide breadth of topics on passwords, security, next-generation, and plenty more. In this installment…
Web Security
This whitepaper is part of a three-part installment covering a wide breadth of topics on passwords, next-generation security and plenty more. In this…
Web Security
As we have seen in part 1 of PCI Complaince, the Good, the Bad and the Insecure, PCI compliance is a good idea in abstract, however it should be…
