Web vulnerability scanner for modern web applications and APIs
Find real, exploitable security vulnerabilities in your web applications and APIs with a proof-based web vulnerability scanner built for modern cybersecurity teams.
Invicti delivers dynamic application security testing (DAST) as part of its comprehensive AppSec platform to automatically validate vulnerabilities, reduce false positives, and help security teams prioritize remediation based on real-world risk.


3600+ Top Organizations Trust Invicti
















What a web vulnerability scanner actually tests
A web vulnerability scanner is a security tool that performs automated vulnerability scanning on web applications, APIs, and web servers to identify security vulnerabilities attackers can exploit.
Unlike network vulnerability assessment tools that focus on infrastructure or operating system weaknesses, a modern web vulnerability scanner analyzes:
- Application logic and functionality
- Authentication and authorization controls
- API endpoints
- JavaScript-heavy front ends and frameworks
- Server-side misconfigurations
- OWASP Top 10 risks and known CVEs
Effective vulnerability scanning strengthens your security posture by detecting web application vulnerabilities before they become real-world security risks.
Why continuous vulnerability scanning is critical for modern web apps
Modern web apps rely heavily on APIs, open-source components, and complex architectures. This dramatically expands the attack surface and introduces new vulnerabilities with every deployment.
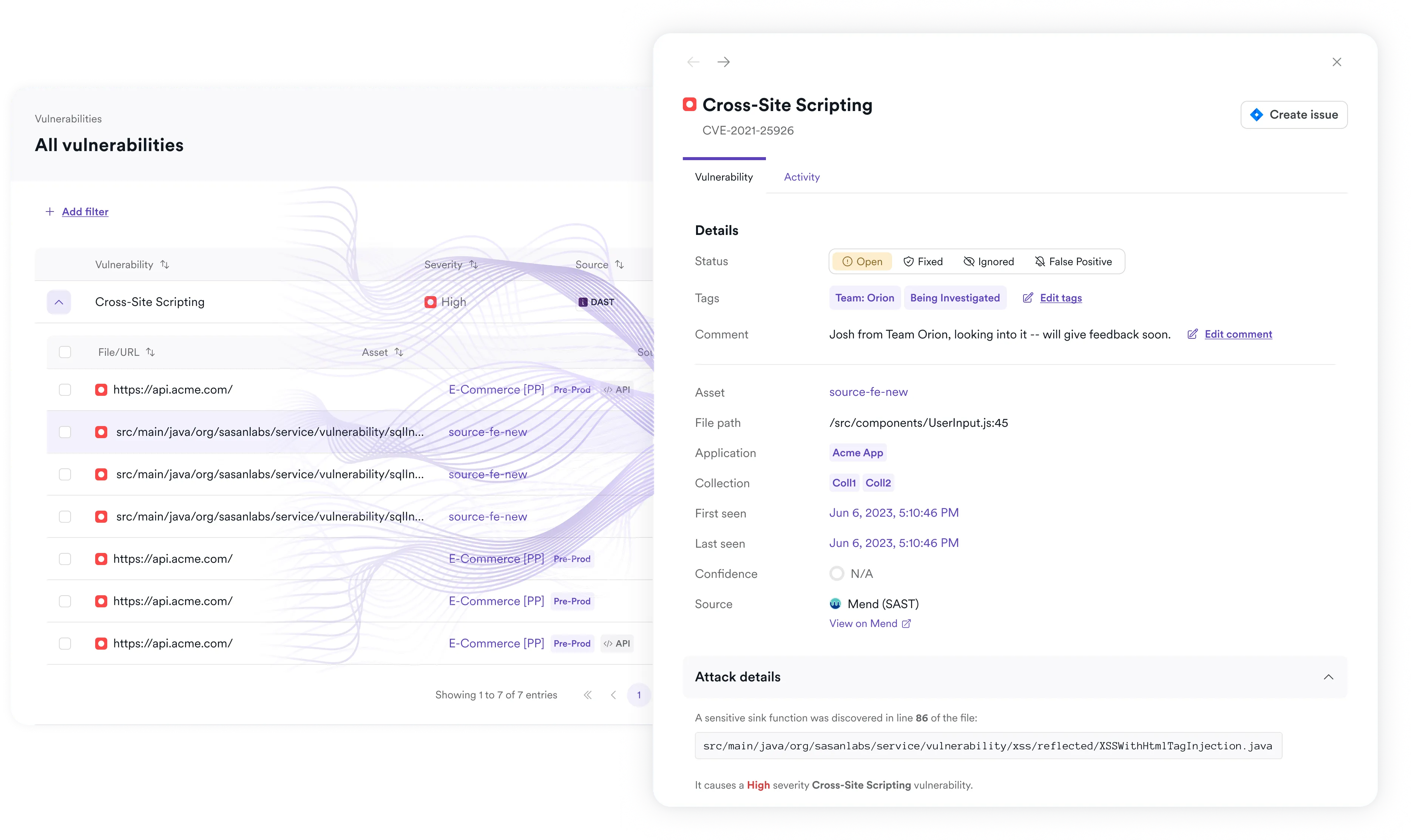
Common types of vulnerabilities detected in web applications include:
- SQL injection
- Cross-site scripting (XSS)
- Authentication bypass
- Misconfigurations
- Exposed endpoints
- Outdated components and known CVEs
- Business logic flaws
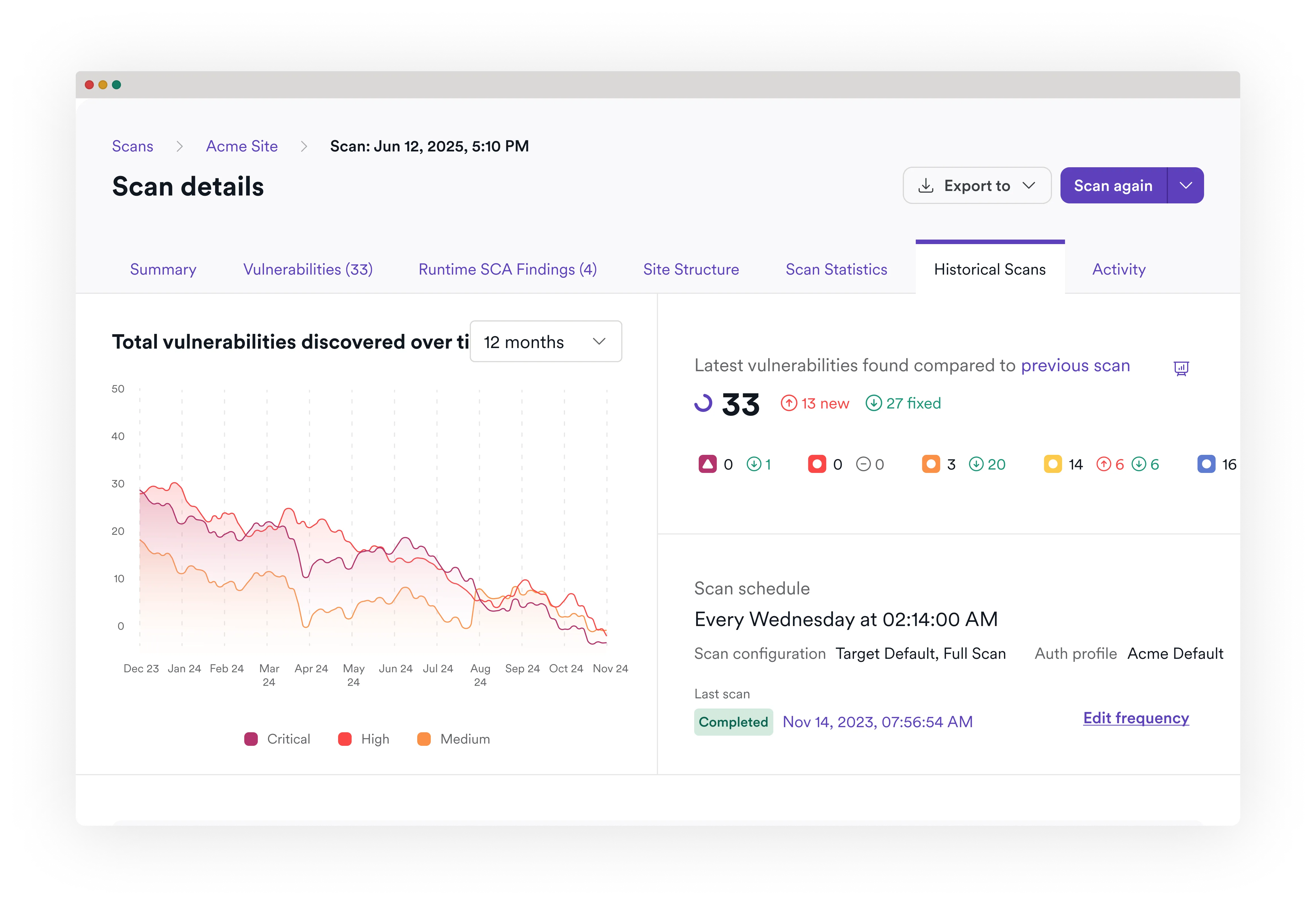
Periodic penetration testing or a one-time pentest is no longer enough. Security teams need continuous vulnerability detection through a combination of scheduled scans, real-time security checks, automated scanning in CI/CD pipelines, and scalable vulnerability management across SaaS and on-prem environments – all to keep pace with development.
How a modern web vulnerability scanner finds and validates vulnerabilities
Modern vulnerability scanning tools must go beyond simple pattern matching. A robust web vulnerability scanner should:
- Discover the full attack surface: Automatically crawl web applications, APIs, and endpoints to identify reachable functionality.
- Handle authentication and complex workflows: Support login flows and restricted areas of your web app.
- Perform dynamic testing: Inject safe payloads to simulate real-world attacks such as SQL injection and cross-site scripting.
- Validate exploitability: Confirm whether a vulnerability is actually exploitable in runtime conditions.
- Integrate into developer workflows: Automate scans in CD pipelines and integrate with tools like Jira and GitHub for faster remediation.
This combination transforms vulnerability scanning from a checklist exercise into actionable application security testing.
.svg)
Stop chasing false positives – validate real vulnerabilities with proof-based DAST
Many vulnerability scanning tools generate excessive false positives. Static scanners and some open-source tools such as ZAP or OpenVAS often flag theoretical issues without proving exploitability.
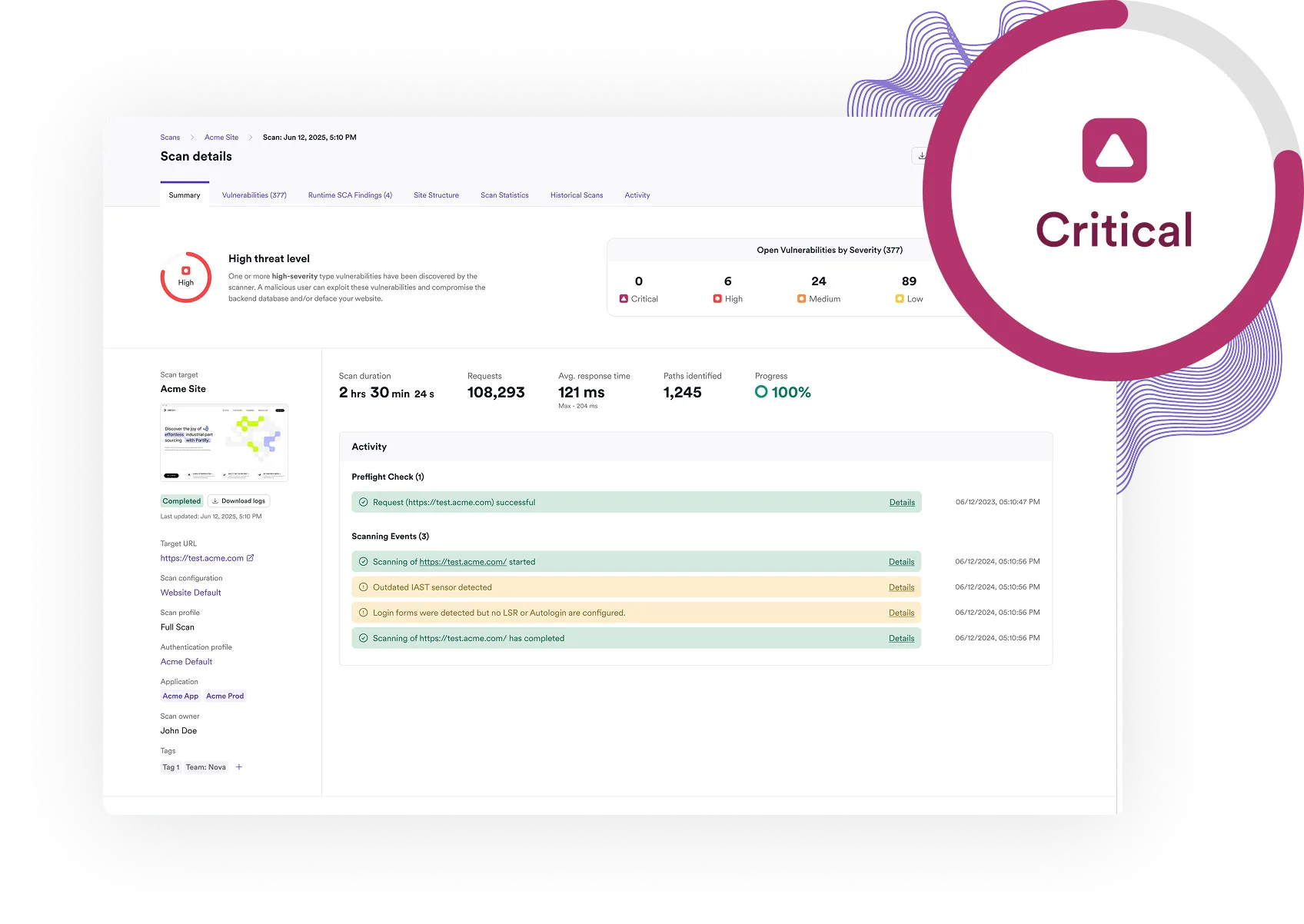
Invicti’s DAST engine uses proof-based scanning to automatically validate many security vulnerabilities. When possible, it demonstrates real-world exploitability, providing evidence instead of assumptions. This DAST-first approach means:
- Fewer false positives
- Faster triage for security teams
- Clearer remediation guidance
- Reduced alert fatigue
- Better prioritization of security issues
Rather than overwhelming teams with noise, Invicti helps prioritize the vulnerabilities attackers can actually use.
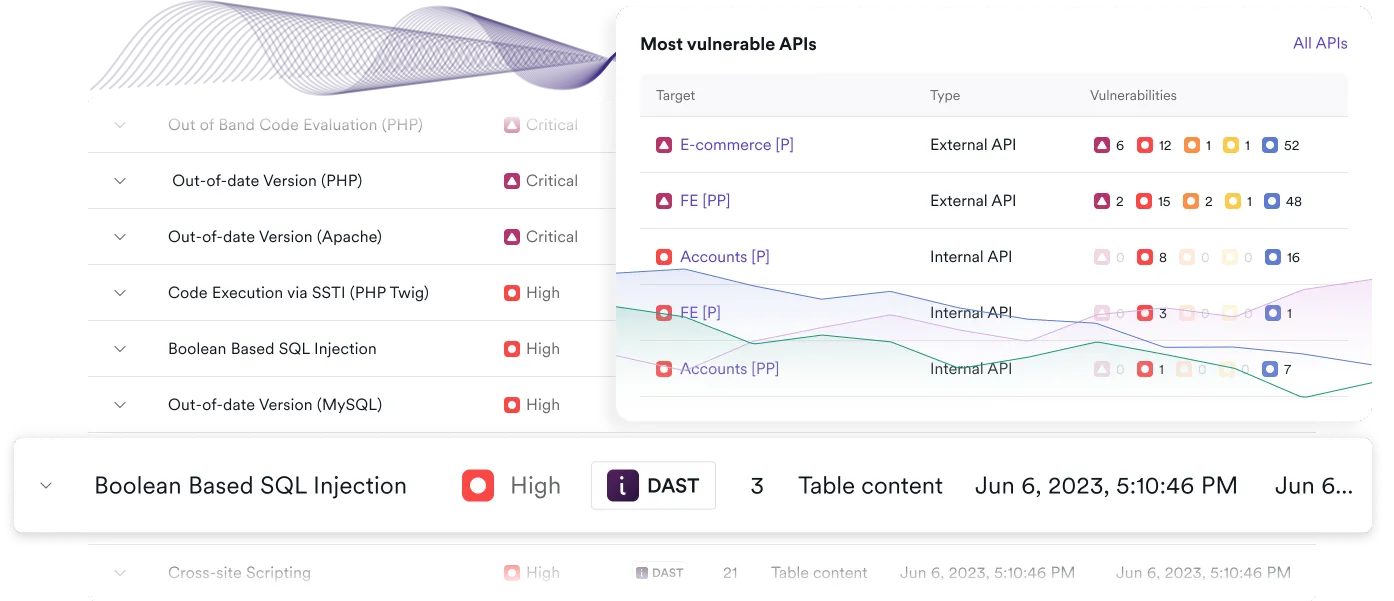
Scan APIs and modern web architectures as part of your full attack surface
APIs now power most web application functionality. A web vulnerability scanner that only tests the frontend leaves critical assets unprotected. Invicti’s API-native DAST:
- Discovers REST and SOAP APIs automatically
- Tests API endpoints for injection, authentication flaws, and other security vulnerabilities
- Validates vulnerabilities across web applications and APIs
- Supports JavaScript-heavy and modern frameworks
Vulnerability scanning must treat API security as an inherent part of web security to provide complete attack surface coverage.
How to choose the right web vulnerability scanner
When evaluating a web vulnerability scanner, whether it be Invicti, Acunetix, Burp Suite, or open-source options like ZAP, security professionals should consider:
- Accuracy and false positive rate
- Coverage of OWASP Top 10 and emerging security risks
- API and web application vulnerability detection
- Authentication support
- CI/CD integration and automated workflows
- Jira and GitHub integration
- Real-time dashboards and reporting
- Scalability for enterprise and SaaS environments
- Support for compliance frameworks such as ISO 27001
- Alignment with broader vulnerability management strategy
A modern web vulnerability scanner should automate security scanning while enabling security teams to prioritize and remediate effectively.

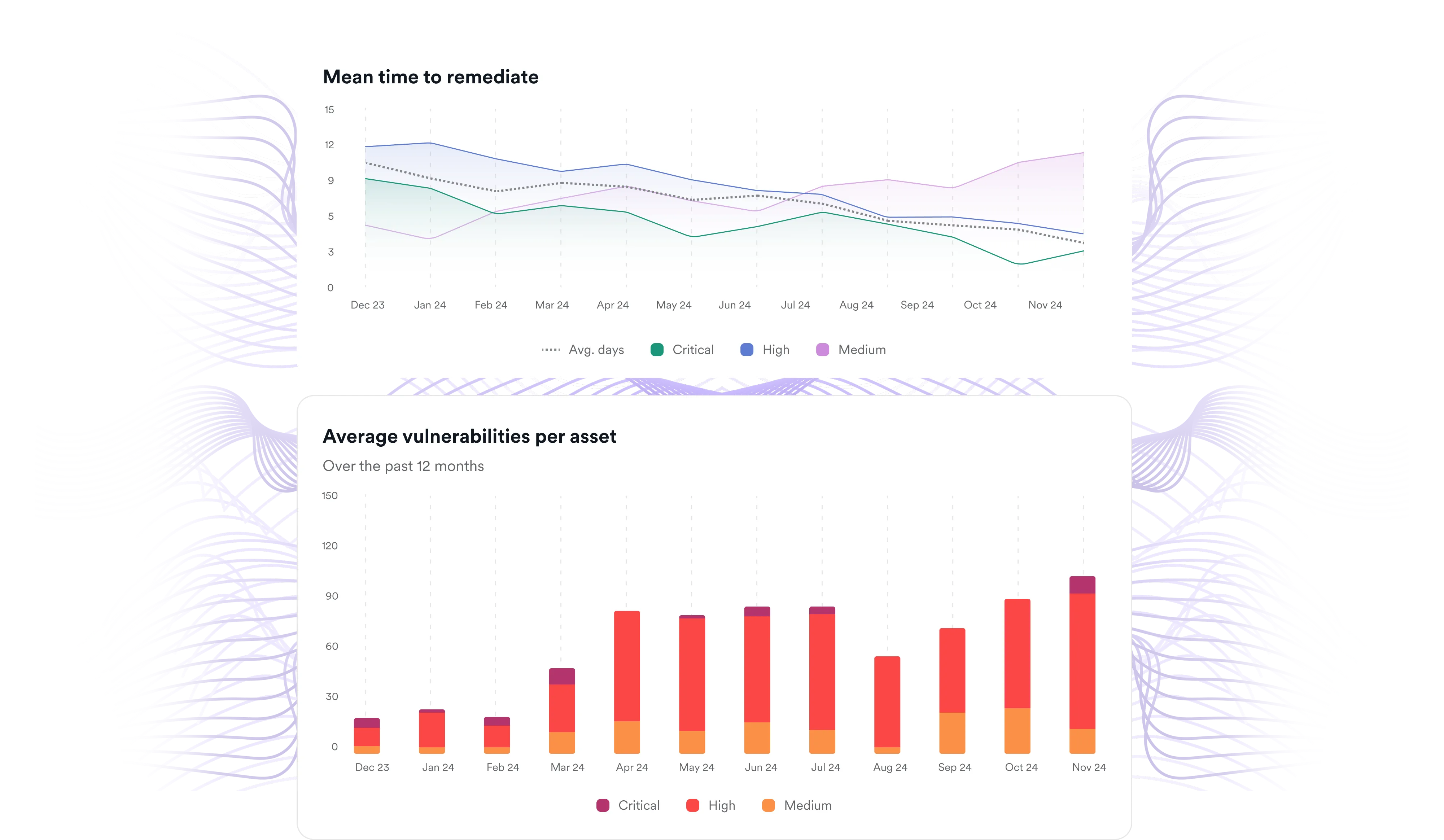
Scale vulnerability management across your web application environments
Invicti supports enterprise-grade vulnerability management with:
- Automated vulnerability scanning across web apps and APIs
- Integration with Jira, GitHub, and CD pipelines
- Centralized dashboards for vulnerability assessment
- Correlation of CVEs and application-level security issues
- Automated prioritization to reduce security risks
By validating exploitability and correlating findings across security tools, Invicti strengthens your overall security posture and accelerates remediation.