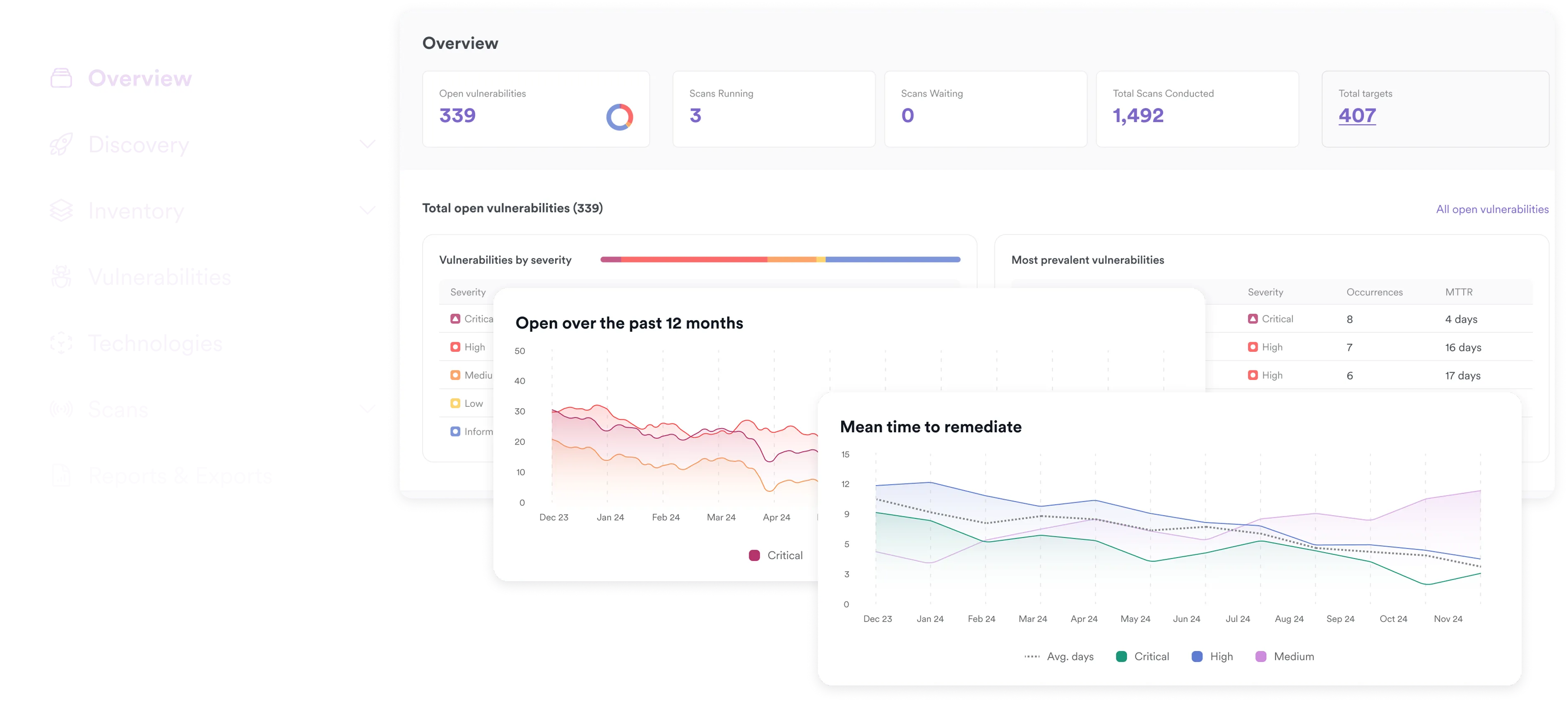
Prioritize and Eliminate Critical Threats with Confidence
Deduplicate findings, validate reachability, and confirm exploitability. Enrich with business context and EPSS scoring to eliminate noise and expose real risk.
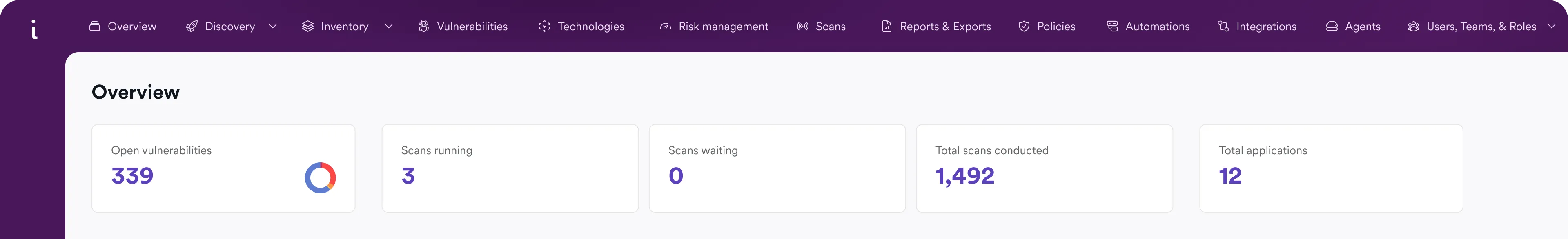
3600+ Top Organizations Trust Invicti
























Find real exploits earlier. Remediate faster.
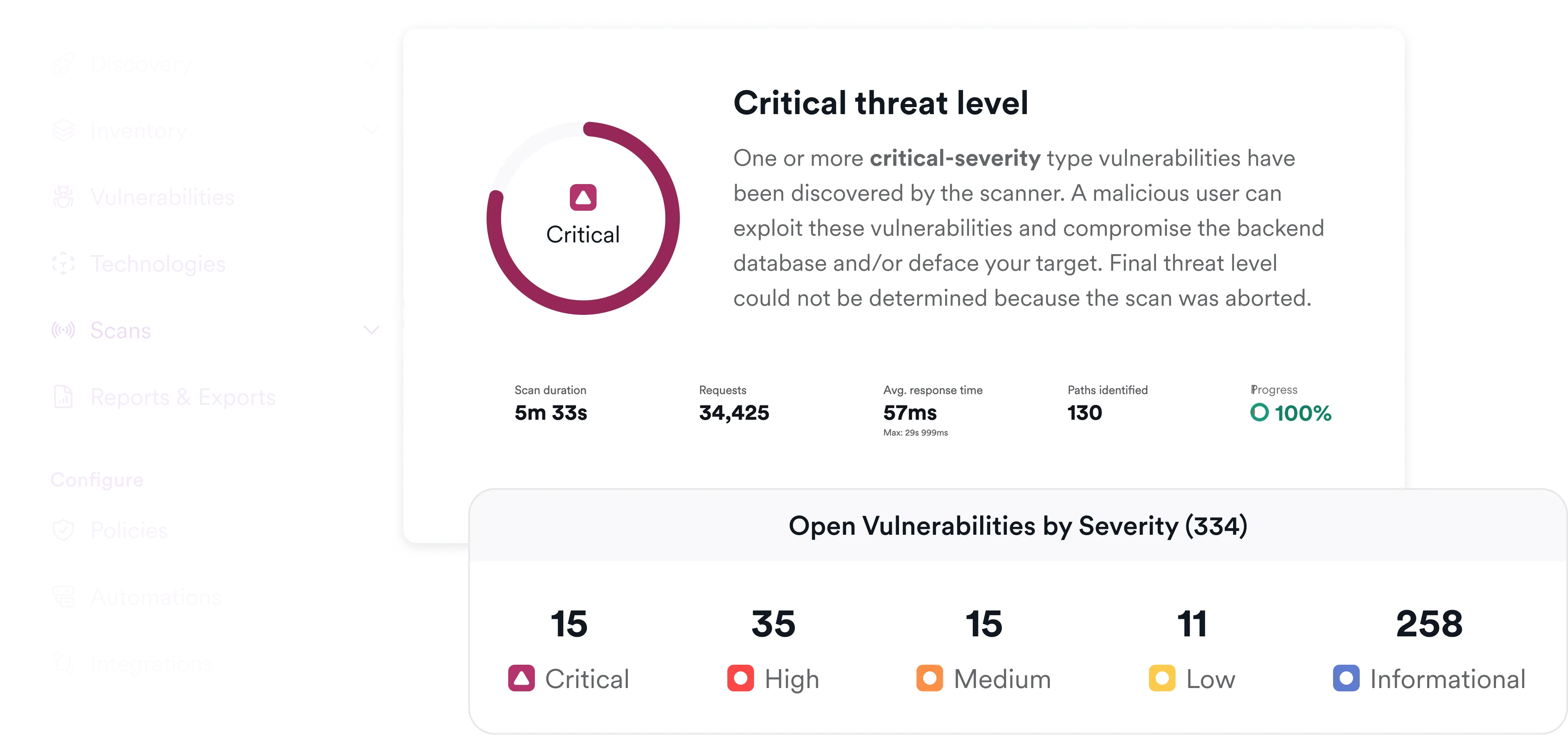
Correlate reachability, exploitability, business impact, and real-world threat intelligence to prioritize what actually puts you at risk.
Get signal without noise
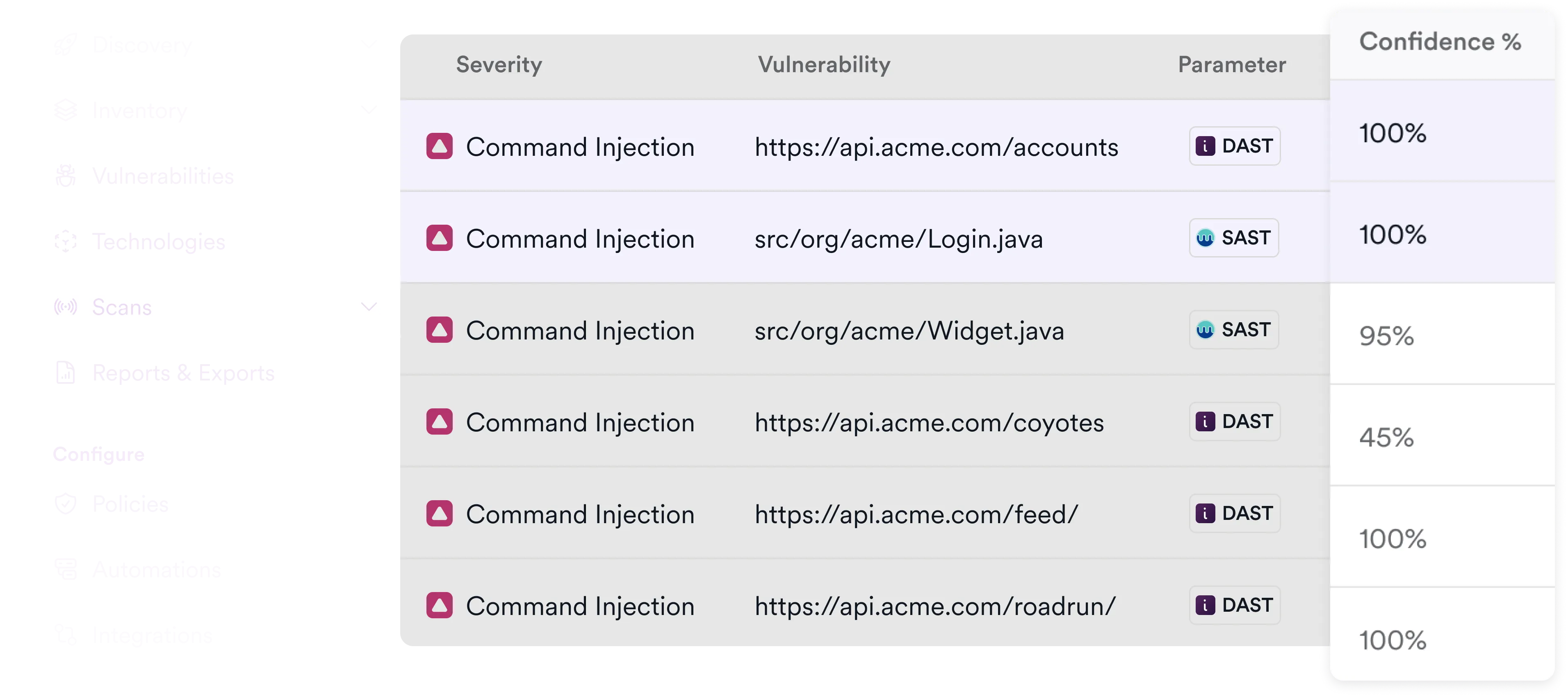
Deduplicate findings across scanners for the cleanest set of vulnerabilities.
See what's reachable
Not every critical CVE is reachable in your application. We know the difference.
Prioritize business threats
Validate exploitability with business context to give your team their time back.
Start with zero noise
Invicti's legacy of industry-leading, zero-noise runtime scanning provides data your team can trust.
Confirm what's reachable
Your environment is unique and sometimes "critical" vulnerabilities aren't actually executed by your application. Invicti confirms what's reachable.

Prove exploitability
Invicti safely exploits vulnerabilities to prove threat criticality with an industry-low rate of false positives.

Prioritize real-world risk
Ensure your team focuses on only the risks that can have a business impact.
Frequently asked threat intelligene questions
At Invicti, threat intelligence means prioritizing vulnerabilities based on real exploitability, reachability within your environment, business context, and real-world exploit likelihood (EPSS)—not just CVE severity or threat feeds.
Invicti uses proof-based DAST to safely exploit vulnerabilities and generate Proof of Exploit (PoE).
This confirms that:
- The vulnerability is real
- It can be triggered
- It produces measurable impact
EPSS (Exploit Prediction Scoring System) measures the likelihood that a vulnerability will be exploited in the wild within the next 30 days. Invicti automatically upgrades severity when EPSS indicates active or likely exploitation, ensuring your team focuses on vulnerabilities attackers are actually targeting.
Traditional CTI focuses on dark web monitoring, IoCs, and external threat feeds for SOC teams. Invicti’s threat intelligence is application-focused. We validate whether vulnerabilities are reachable and exploitable in your running applications, then enrich analysis with business impact and EPSS scoring to guide remediation.
Reachability determines whether a vulnerable component or endpoint is actually accessible in your deployed application. Exploitability confirms whether that reachable weakness can be successfully abused. Invicti correlates both before elevating risk so theoretical vulnerabilities don’t distract from real exposure.
Invicti allows organizations to:
- Label applications by business criticality
- Map vulnerabilities to ownership and teams
- Apply SLA-based prioritization rules
- Adjust severity based on asset importance
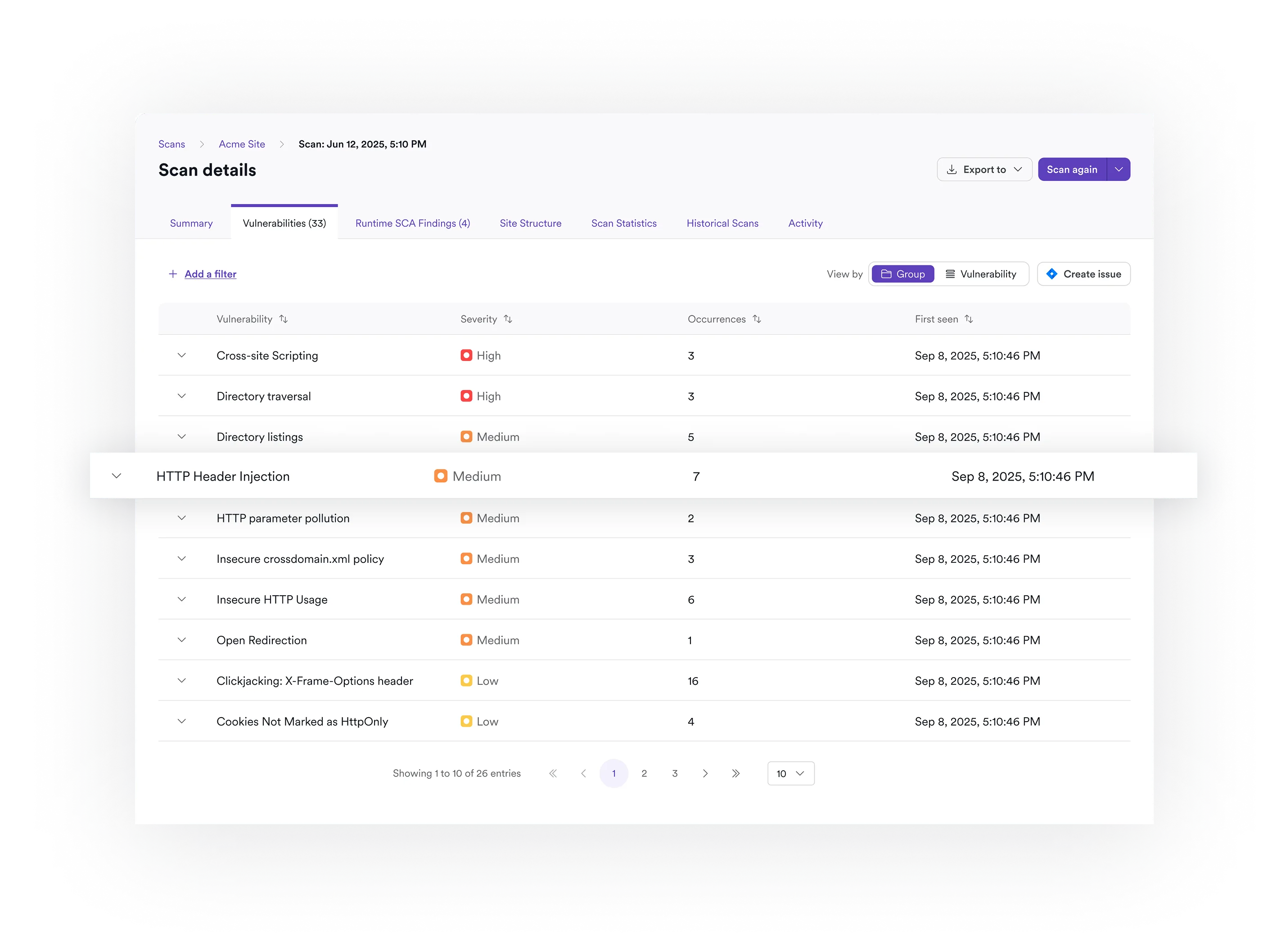
False positives are reduced through:
- Proof-based exploit validation
- Deduplication across scanners
- Suppression rules with expiration controls
- Corporate vulnerability memory
Secure Attack Surfaces Across the SDLC