Multi-Layer API Discovery is Different
Invicti correlates discovery data from source code, network traffic, API gateways, and web applications to continuously maintain a complete API inventory for scanning.
Automatically discover APIs across source code, gateways, runtime traffic, and web applications to build a complete and continuously updated API inventory.


















Organizations don’t know how many APIs they actually have. Undocumented APIs exist outside official inventories, leaving some attack surfaces invisible.
Most tools require manually uploaded schemas, endpoints, and authentication details. Developers rarely have this information, slowing or blocking testing.
Microservices, mobile apps, and machine-to-machine integrations constantly create new endpoints. APIs evolve faster than security teams can track them.
Web crawling or traffic monitoring alone can only reveal part of the API ecosystem. Many APIs remain hidden because they aren’t tied to a UI or active traffic.
Invicti correlates discovery data from source code, network traffic, API gateways, and web applications to continuously maintain a complete API inventory for scanning.
Modern applications often define APIs directly within source code.
Invicti connects directly to developer repositories like GitHub, GitLab
and Bitbucket.
From the codebase, the platform can:
This allows APIs to be discovered before they are deployed, giving security teams visibility earlier in the development lifecycle.
Invicti's industry-defining DAST identifies APIs automatically while scanning your web applications.
Our engine:
This allows security teams to quickly identify APIs connected to web applications and add them to the API inventory without manual configuration.

Find APIs through gateway platforms such as:
Invicti integrates directly with these gateways to retrieve API endpoints, schemas and documentation. This allows security teams to automatically discover APIs already deployed within their infrastructure.
Some APIs only become visible once they're running in production. Invicti can analyze network traffic to detect API activity across infrastructure such as:
By observing requests and responses, Invicti can identify active endpoints, extract API structures and reconstruct schemas. This helps discover undocumented APIs and endpoints that may not appear in application code or documentation.

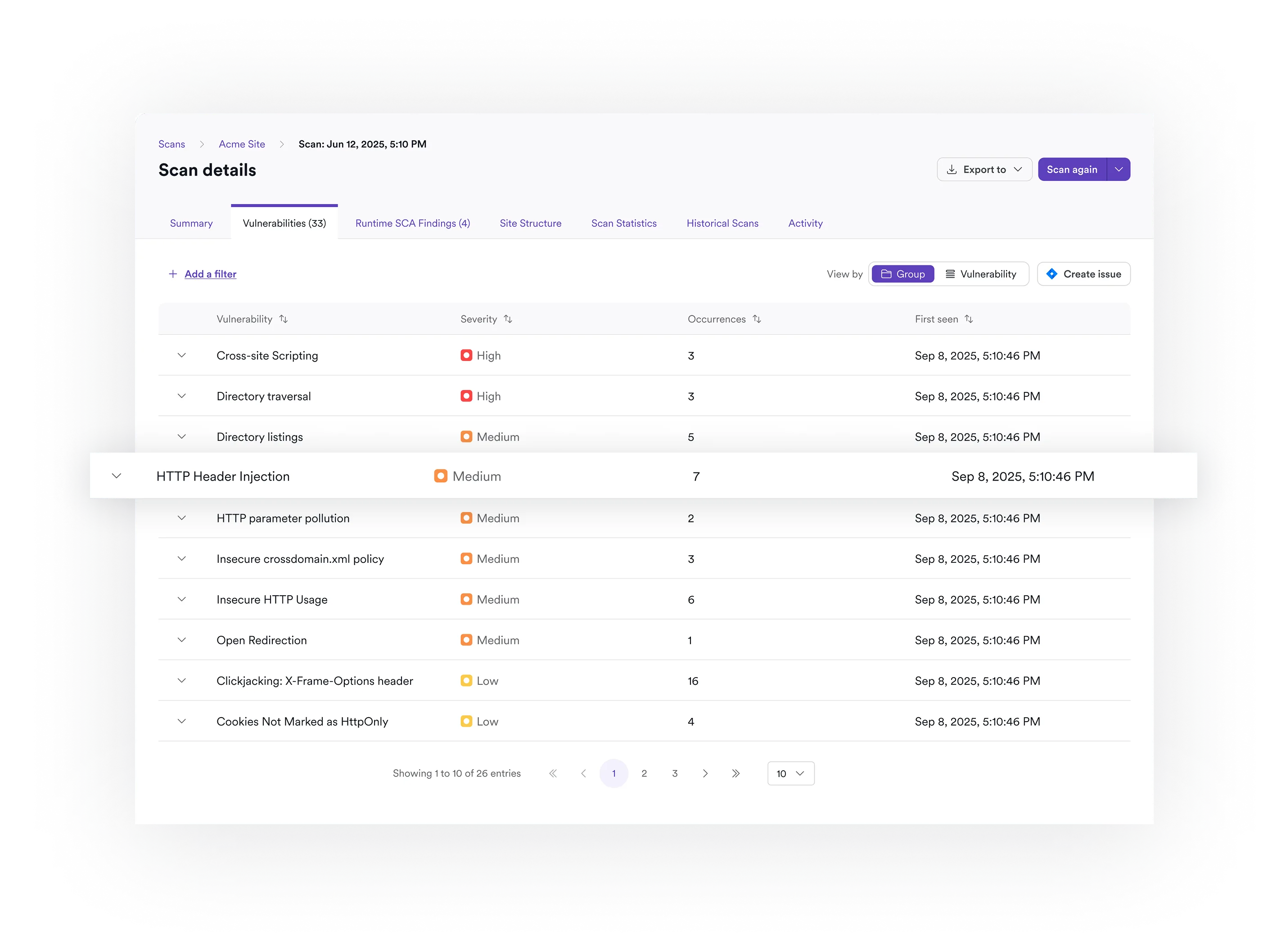
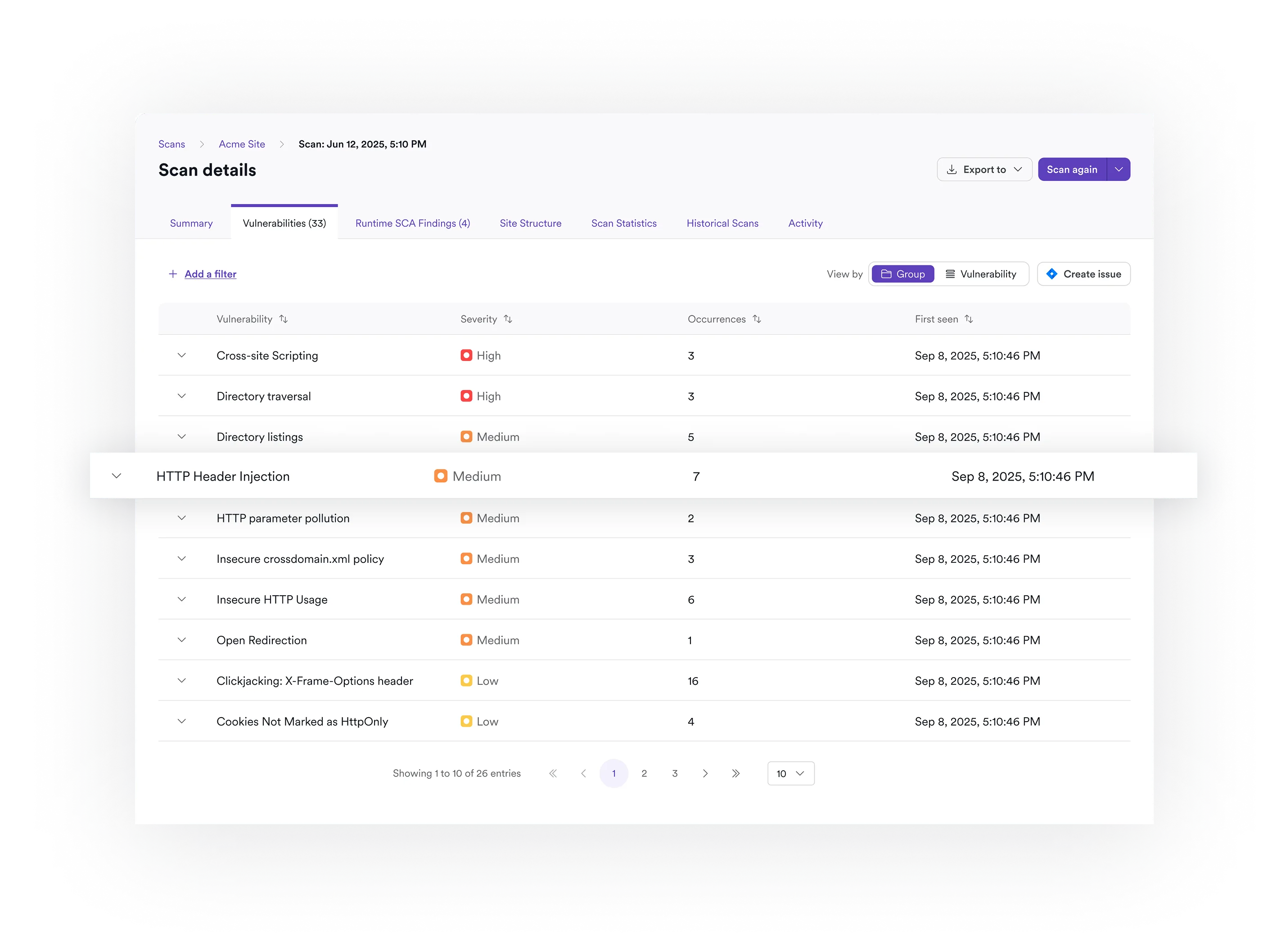
Invicti uses multi-layer API discovery to identify endpoints across your environment. The platform gathers API information from web application scans, API gateways, network traffic analysis, and source code repositories. By correlating these discovery sources, Invicti builds a complete API inventory without requiring developers to manually provide schemas or endpoint lists.
Yes. Invicti can connect directly to source code repositories such as GitHub, GitLab, and Bitbucket to identify APIs defined in code. This allows APIs to be discovered earlier in the development lifecycle so security testing can begin before deployment.
Invicti can detect and work with common authentication mechanisms such as tokens, cookies, and OAuth. During discovery and scanning, the platform identifies authentication patterns and uses them to perform authenticated testing of API endpoints.
Yes. Invicti integrates with CI/CD pipelines and development repositories to detect new or modified APIs as applications evolve. Newly discovered APIs are automatically added to the inventory and prepared for security testing.
Invicti can discover many types of APIs, including:
This allows security teams to identify APIs that may not appear in documentation or application inventories.
No. Many API security tools require developers to manually provide OpenAPI or Swagger specifications before testing can begin. Invicti automatically extracts or reconstructs API schemas from discovery sources such as code, gateways, and network traffic. This removes the need for manual setup.
API monitoring tools primarily analyze runtime traffic to detect attacks or suspicious activity. Invicti focuses on proactive API security testing. The platform discovers APIs across multiple sources and then actively tests them for vulnerabilities such as those listed in the OWASP API Top 10.
Once APIs are identified, Invicti automatically prepares them for testing by extracting or generating API schemas and mapping endpoint relationships. The APIs are then passed to the DAST engine, which scans them for vulnerabilities such as broken access control, injection flaws, and authentication weaknesses.