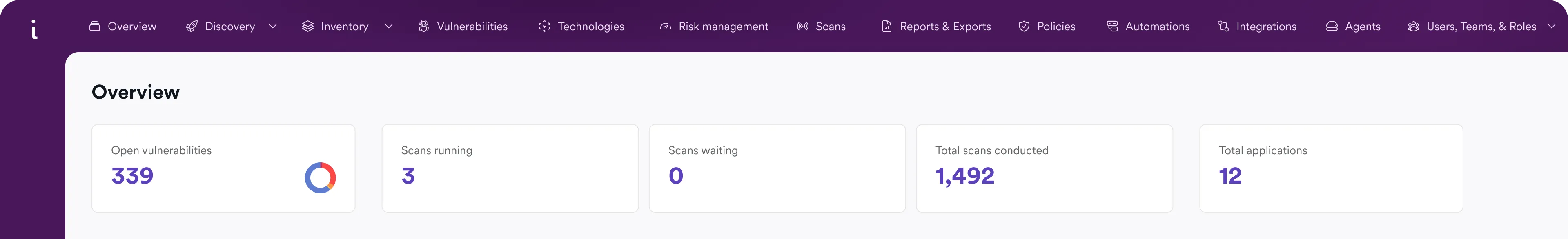
Manage Your Entire Application Attack Surface
Monitor and manage your application attack surfaces from build to production. Identify risky configurations in IaC, validate runtime exposures with DAST, and uncover hidden APIs.
3600+ Top Organizations Trust Invicti
























ASM for Code, Apps, and APIs
Invicti monitors and manages how attack surfaces are created, exposed, and expanded across IaC, running applications, and APIs.
All vulnerabilities are proven, prioritized, and displayed in a single view for fast remediation.
Infrastructure as Code
Prevent risky infrastructure from becoming an exposed application attack surface.
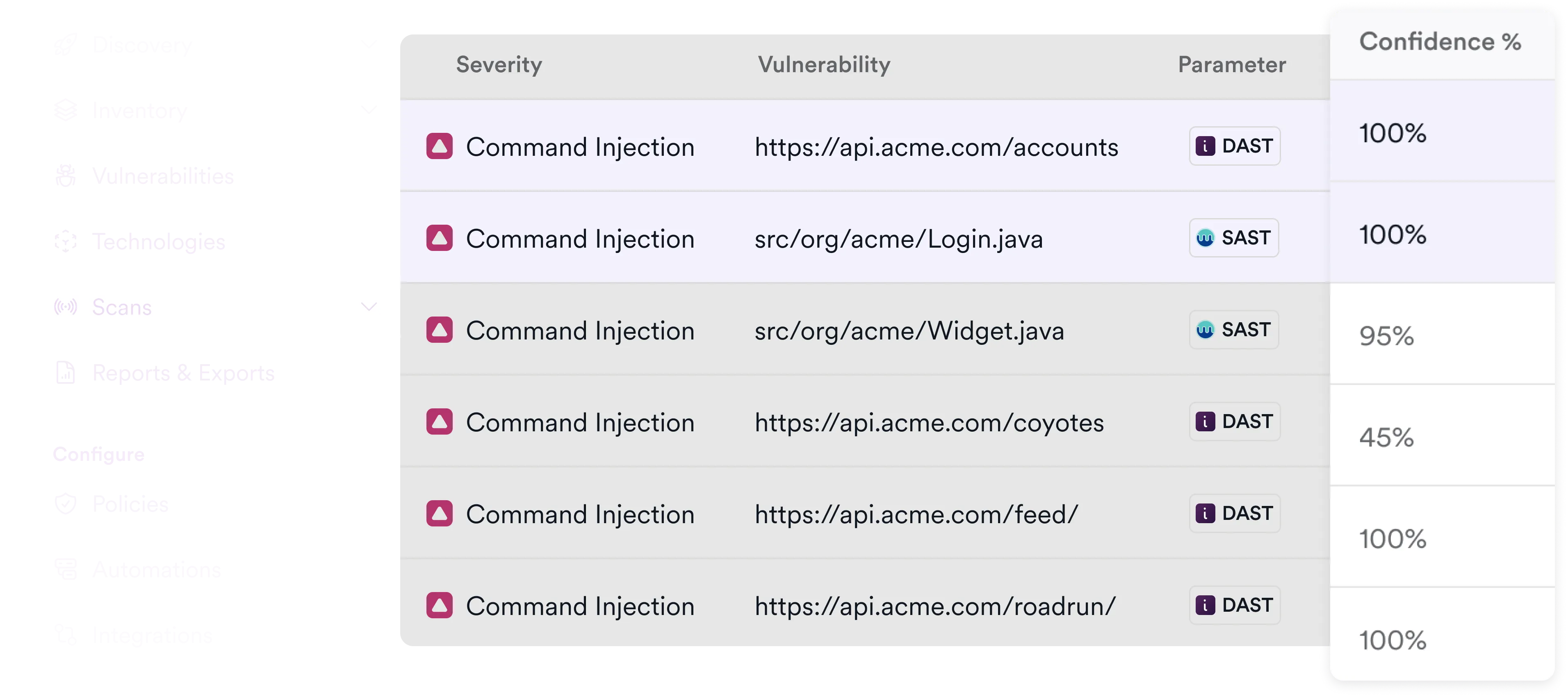
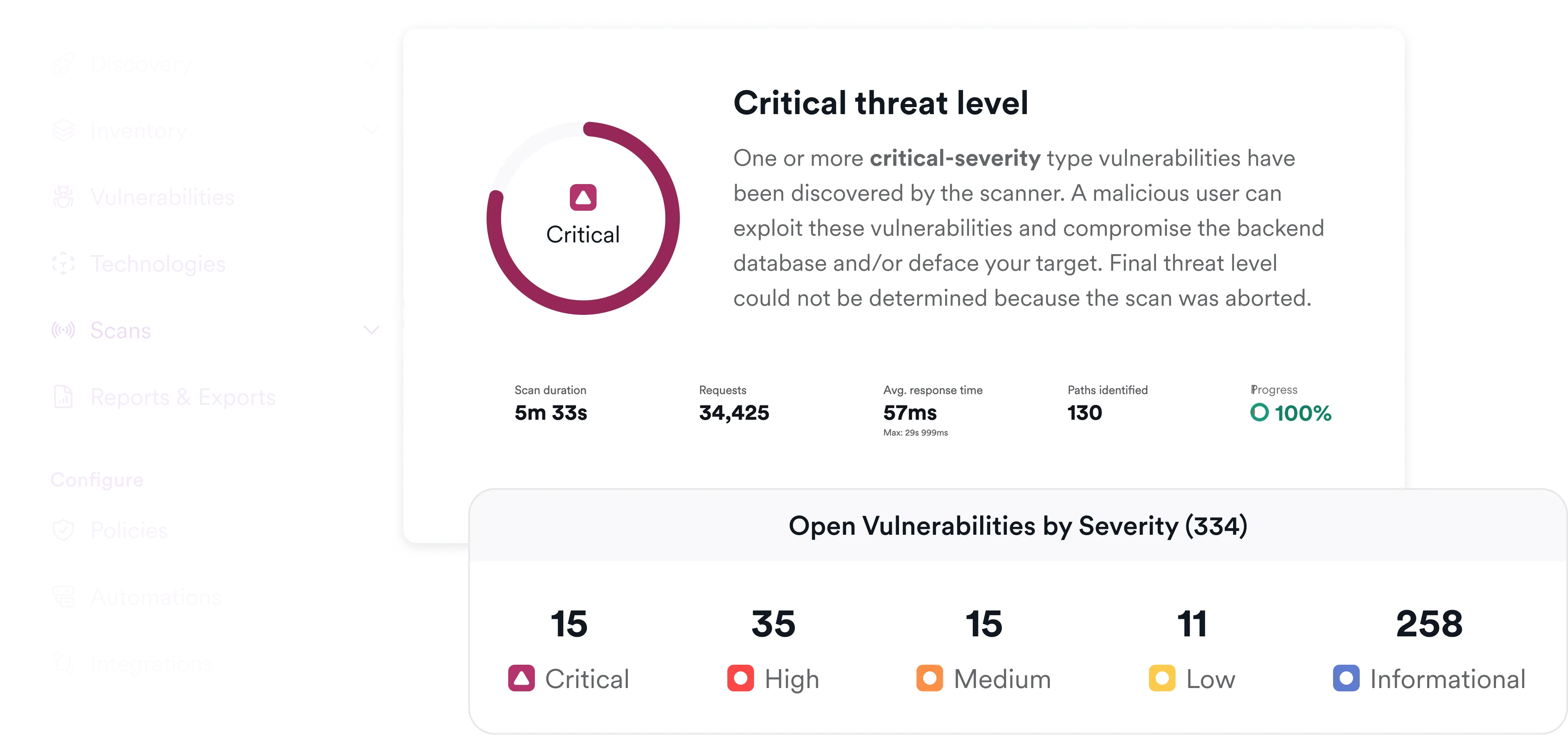
DAST
Continuously discover exploitable paths, workflows, and business logic.
API
Track known and unknown APIs, surfacing authorization and data exposure risks.
Orchestrate and Correlate IaC Scans
Trigger Infrastructure as Code security checks and correlate findings with runtime exposure.
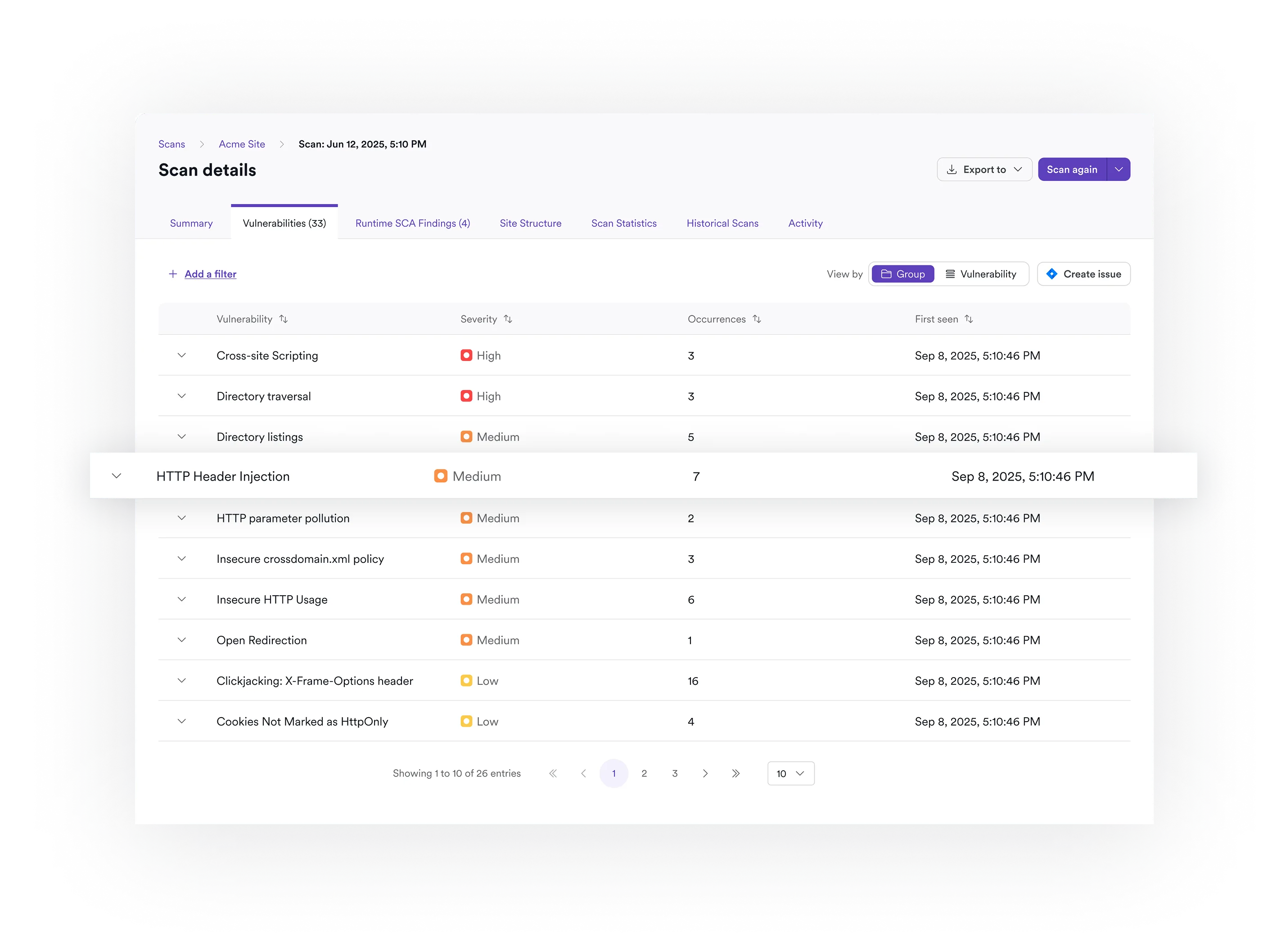
Industry-Best DAST
Silence noise with proof-based scanning that reveals your riskiest runtime vulnerabilities.

API Discovery and Testing
Innovative scanning and testing for a complete picture of your API security.

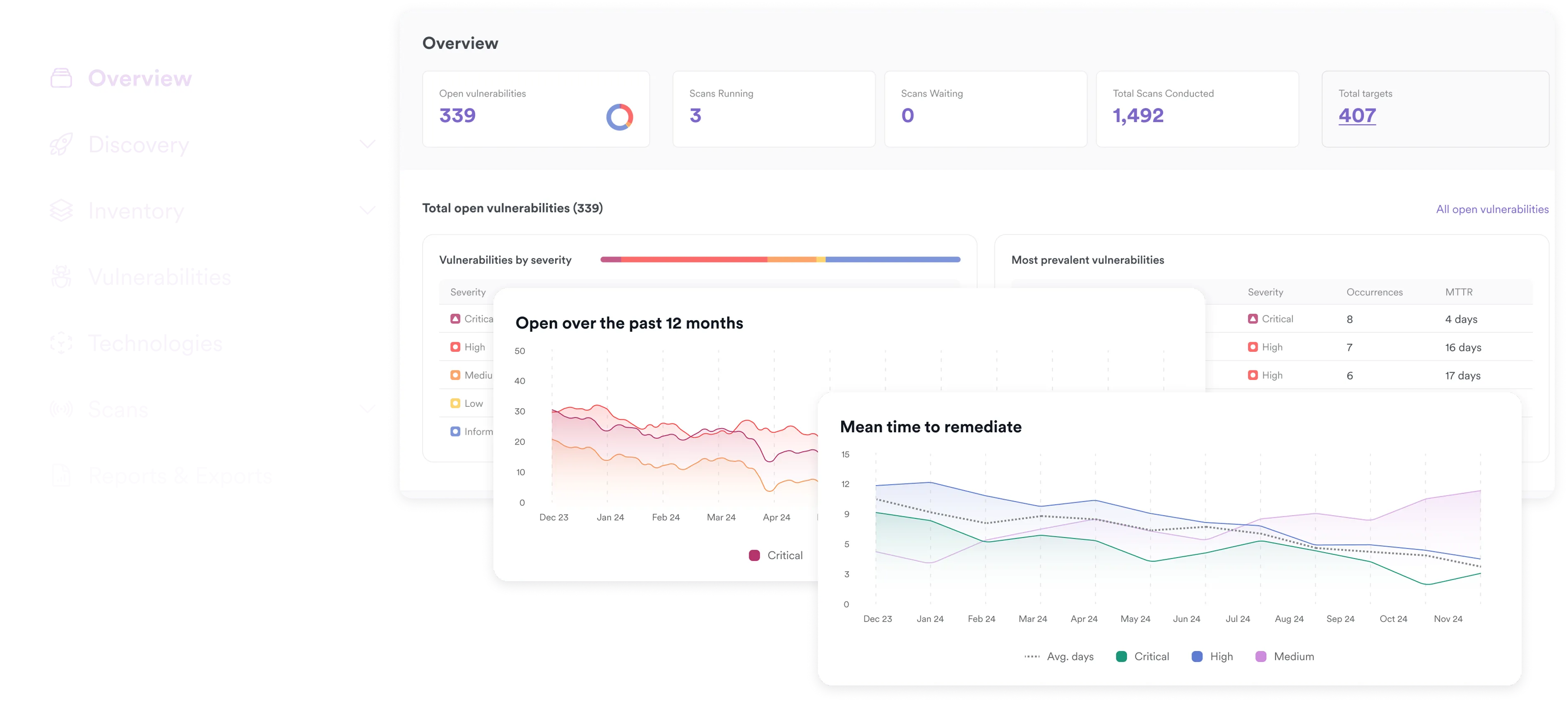
Vulnerability Management
See all your vulnerabilities—deduplicated and correlated—in one view.
Frequently asked ASM questions
Invicti manages attack surface at the application layer—tracking how attack surface is created in IaC, exposed in running applications, and expanded through APIs, then validating what attackers can actually exploit.
Invicti uses multiple API discovery techniques, including sensorless discovery and traffic-based analysis, to identify undocumented and unmanaged APIs that expand attack surface without security review. Invicti supports stateful API scanning, maintaining authentication and session context across multi-step API workflows to uncover authorization and business logic flaws that single-request tools miss.
DAST is the core of Invicti’s attack surface monitoring and management. It discovers and tests reachable application paths, workflows, and business logic in live environments, validating which parts of the attack surface are truly exploitable.
Yes. Invicti supports Software Composition Analysis (SCA) and SBOM generation to help teams understand open-source components and supply-chain risk associated with their applications. SBOMs are not attack surface monitoring on their own, but they support attack surface reduction by identifying vulnerable dependencies that expand exploitable risk within applications.
Secure Attack Surfaces Across the SDLC