Find cross-site request forgery vulnerabilities with accurate, automated DAST
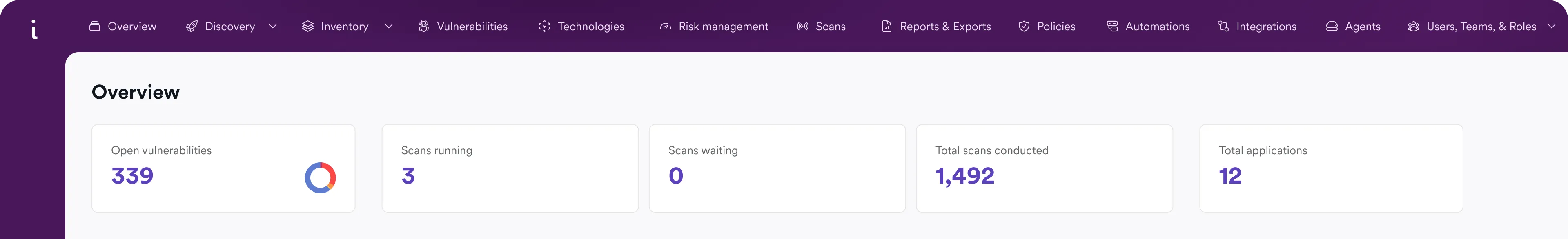
Detect CSRF vulnerabilities in web applications and APIs as part of a DAST-first web application security program. Invicti helps security and development teams identify real, exploitable risks across modern applications – not just isolated security issues.


3600+ Top Organizations Trust Invicti
















Find CSRF vulnerabilities before attackers do
Cross-site request forgery (CSRF), also called XSRF, is a web application security vulnerability that allows attackers to trick authenticated users into submitting unwanted HTTP requests to a target website. Because the victim’s web browser automatically includes session cookies and authentication headers, vulnerable applications may accept malicious requests as legitimate actions.
A successful CSRF attack can lead to unauthorized account changes, privilege escalation, data modification, password resets, or fraudulent transactions. Risks are especially high in authenticated application areas, administrative workflows, and server-side functionality that processes state-changing POST requests.
Common CSRF targets include:
- Account management functions
- Password and email change forms
- Administrative actions
- Financial or transactional workflows
- Browser-accessible API endpoints
- State-changing POST requests without proper validation
- HTML forms lacking anti-CSRF protections
- JSON-based API requests tied to authenticated sessions
Invicti scans running applications to help identify CSRF vulnerabilities alongside other exploitable web security risks.

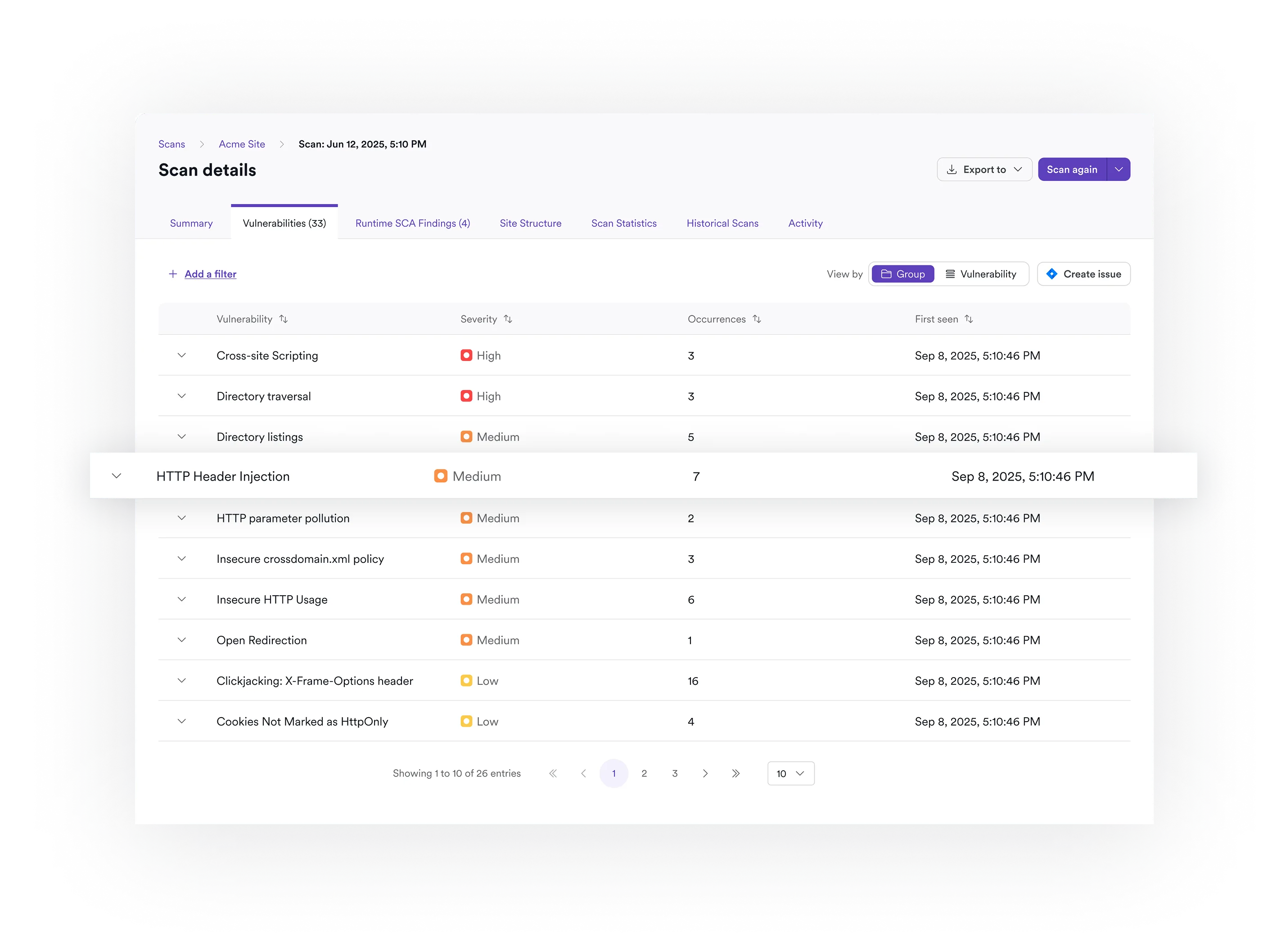
Scan for CSRF as part of full DAST coverage
Modern applications face far more than a single vulnerability type. While CSRF remains an important OWASP security concern, organizations also need visibility into injection flaws, cross-site scripting (XSS), authentication weaknesses, security misconfigurations, exposed components, and API-related risks.
Invicti uses dynamic application security testing (DAST) to analyze running web applications from the outside in – the same perspective attackers use during penetration testing. This approach helps security teams identify vulnerabilities that are actually reachable in production environments.
Instead of relying on a standalone CSRF checker or narrow security tools, organizations can use Invicti as a web vulnerability scanner that continuously tests their broader web application and API attack surface through one unified platform.
Invicti supports testing for modern applications and APIs that exchange data using HTML, JSON, and other common formats across distributed environments.
Reach more of your application with authenticated scanning
Many CSRF vulnerabilities exist behind login pages in authenticated workflows that basic scanners never reach. Effective CSRF testing depends on accurate crawling, session handling, authentication support, and controlled scan configuration.
Invicti is designed to help organizations test modern web applications, including JavaScript-heavy applications, APIs, and complex server-side functionality. Advanced crawling and scanning capabilities help security teams cover more of the application surface while maintaining control over scan scope and configuration.
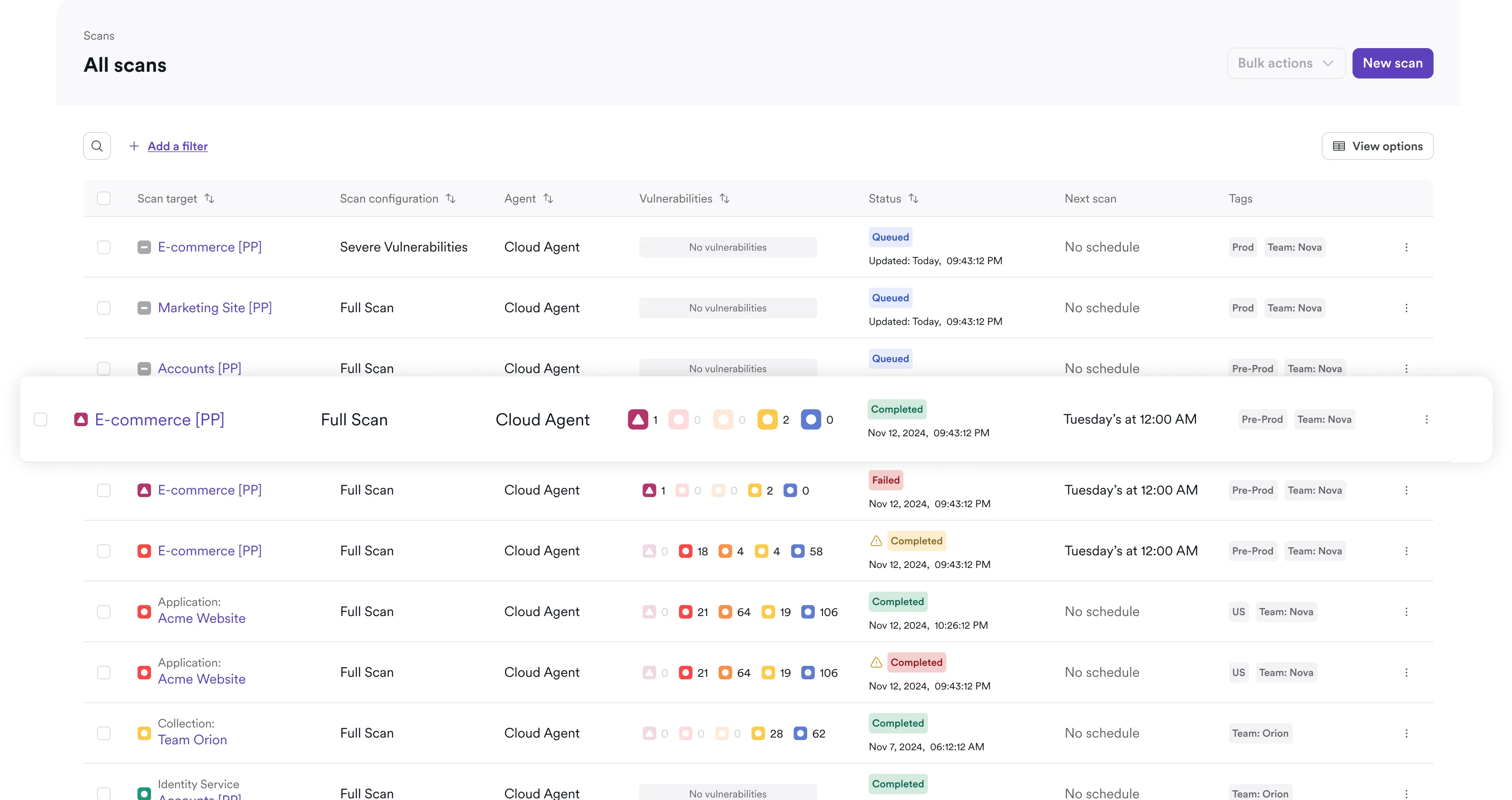
This is especially important for large or distributed environments where different applications, development teams, and release cycles require flexible scanning policies and targeted testing workflows. Capabilities that support effective CSRF testing include:
- Authenticated application scanning
- Support for modern JavaScript frameworks
- Flexible scan scope configuration
- API discovery and security testing
- Scheduled and automated scans
- Centralized vulnerability visibility
- Support for complex HTTP request workflows
- Coverage for modern web page interactions and dynamic content
Whether applications are built with PHP, modern JavaScript frameworks, or API-first architectures, Invicti helps teams automate security testing across their application portfolio.

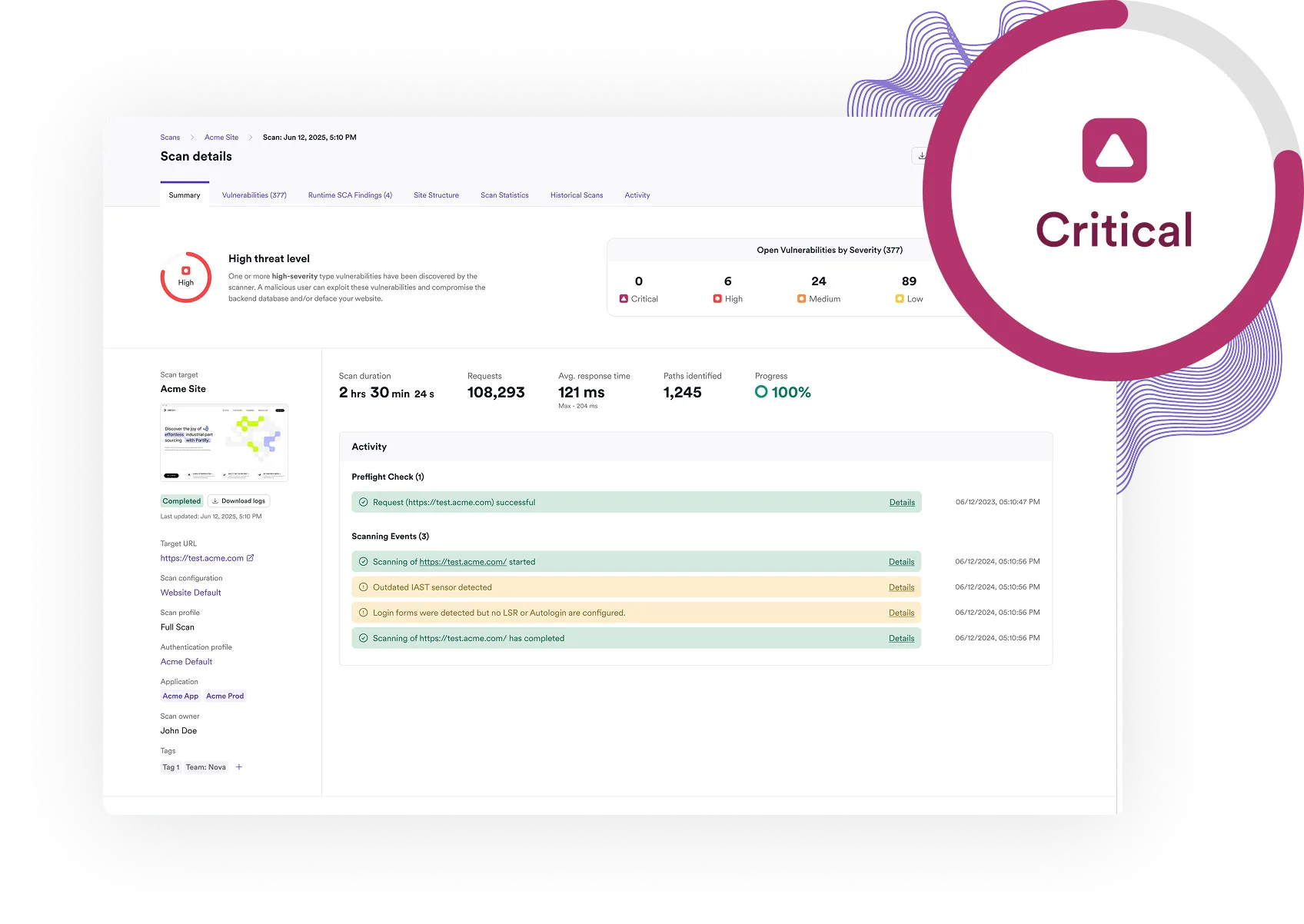
Reduce noise and focus on real risk
Security teams do not need more alerts – they need actionable findings that developers can verify and fix efficiently. Invicti’s DAST-first approach focuses on vulnerabilities that attackers can actually reach in running applications. By testing applications dynamically instead of relying only on static analysis, organizations can prioritize real runtime risk and improve overall cybersecurity and security posture.
For many common vulnerability classes, Invicti can automatically validate exploitability using proof-based scanning technology to help reduce false positives and speed remediation workflows. Developers get detailed vulnerability information and remediation guidance so they can spend less time reproducing issues manually and more time fixing security problems. This helps organizations:
- Reduce alert fatigue
- Improve remediation efficiency
- Prioritize exploitable vulnerabilities
- Streamline collaboration between security and development teams
- Scale AppSec testing across large application environments
- Strengthen enterprise web application security programs
Unlike manual workflows that depend entirely on penetration testing or custom testing templates, automated DAST helps organizations continuously monitor security risk as applications evolve.
Make CSRF testing part of your AppSec workflow
CSRF testing works best when it becomes part of an ongoing application security process instead of a one-time assessment.
Invicti helps organizations integrate security testing into development and operational workflows with automated scanning, centralized reporting, and integrations across the SDLC. Security teams can continuously monitor web applications and APIs while developers receive the context they need to remediate vulnerabilities faster.
As applications evolve and attack surfaces expand, continuous DAST helps organizations maintain visibility into changing security risk across both application frontends and APIs.
Teams using developer platforms, CI/CD pipelines, GitHub repositories, and modern DevSecOps workflows can incorporate automated security testing into existing processes without adding unnecessary complexity.
Frequently asked CSRF scanner questions
A CSRF scanner is a security testing tool that helps identify cross-site request forgery vulnerabilities in web applications. Most modern CSRF detection capabilities are included within broader web vulnerability scanner and DAST platforms.
Cross-site request forgery (CSRF), also called XSRF, is a web application security vulnerability that tricks an authenticated user’s web browser into sending unintended HTTP requests to a web server. If the application does not properly validate the request, attackers may be able to perform actions using the victim’s authenticated session.
CSRF vulnerabilities can be detected through manual penetration testing, code review, and automated DAST scanning. Automated scanners are especially useful to analyze application behavior, HTML forms, authentication workflows, request headers, and server-side request validation mechanisms to identify potential CSRF weaknesses and verify exploitability.
Yes. Dynamic application security testing (DAST) solutions can help identify CSRF vulnerabilities by testing running web applications from the outside in and analyzing how applications process authenticated requests and state-changing actions.
Common CSRF protections include anti-CSRF tokens, secure SameSite cookie settings, origin and referrer validation, secure session management, and avoiding unsafe state-changing GET requests. Many modern frameworks and OWASP-recommended security controls also include built-in CSRF protections.
Yes. SameSite cookies can reduce CSRF risk, but they are not a complete defense in every situation. Organizations should still implement layered protections and security testing for sensitive application functionality.
Not only. Invicti detects CSRF vulnerabilities as part of broader DAST coverage for web applications and APIs, including vulnerabilities such as XSS, SQL injection, authentication weaknesses, misconfigurations, exposed components, and other exploitable security issues.
Manual testing tools are used during penetration testing and security research. Invicti complements these workflows with automated DAST designed to continuously scan web applications and APIs at scale across development and production environments.
Find and fix real AppSec risks with Invicti