SQL injection scanner
Invicti’s SQL injection scanner goes beyond detection and confirms real SQLi vulnerabilities with proof-based scanning by safely extracting data from the database to demonstrate exploitability.
With its DAST-first platform, Invicti helps teams find, validate, and fix SQL injection vulnerabilities in web applications and APIs – before attackers do.

3600+ Top Organizations Trust Invicti
























A DAST-first approach to SQL injection detection
There’s a lot more to SQL injection scanning than just identifying patterns in user input – you should be able to prove which vulnerabilities attackers can actually exploit. Many testing tools, including open source scanners and basic vulnerability scanning solutions, rely on signatures or simulated payloads. This often results in false positives and limited visibility around how SQL queries are executed on the server side.
The Invicti Platform uses dynamic application security testing (DAST) to analyze running applications from the outside in:
- Sends crafted payloads through real HTTP requests
- Tests how applications process user input across parameters, headers, and endpoints
- Evaluates actual SQL statements and database interactions
- Identifies exploitable SQL injection attacks, including blind SQL injection
This approach provides a realistic view of risk based on how attackers perform pentesting and exploit real, reachable vulnerabilities.
Find and prove SQL injection vulnerabilities
Invicti combines deep crawling with advanced SQL injection scanning to uncover security flaws across your application. Invicti’s DAST scanner:
- Maps the attack surface across pages, APIs, and endpoints
- Analyzes inputs that interact with SQL commands and backend logic
- Tests multiple injection techniques, including boolean-based, time-based, and error-based SQL injection
- Detects vulnerabilities in server-side processing and database queries
Unlike tools such as sqlmap that focus on manual pentesting workflows, Invicti automates detection at scale as part of continuous web vulnerability scanning.
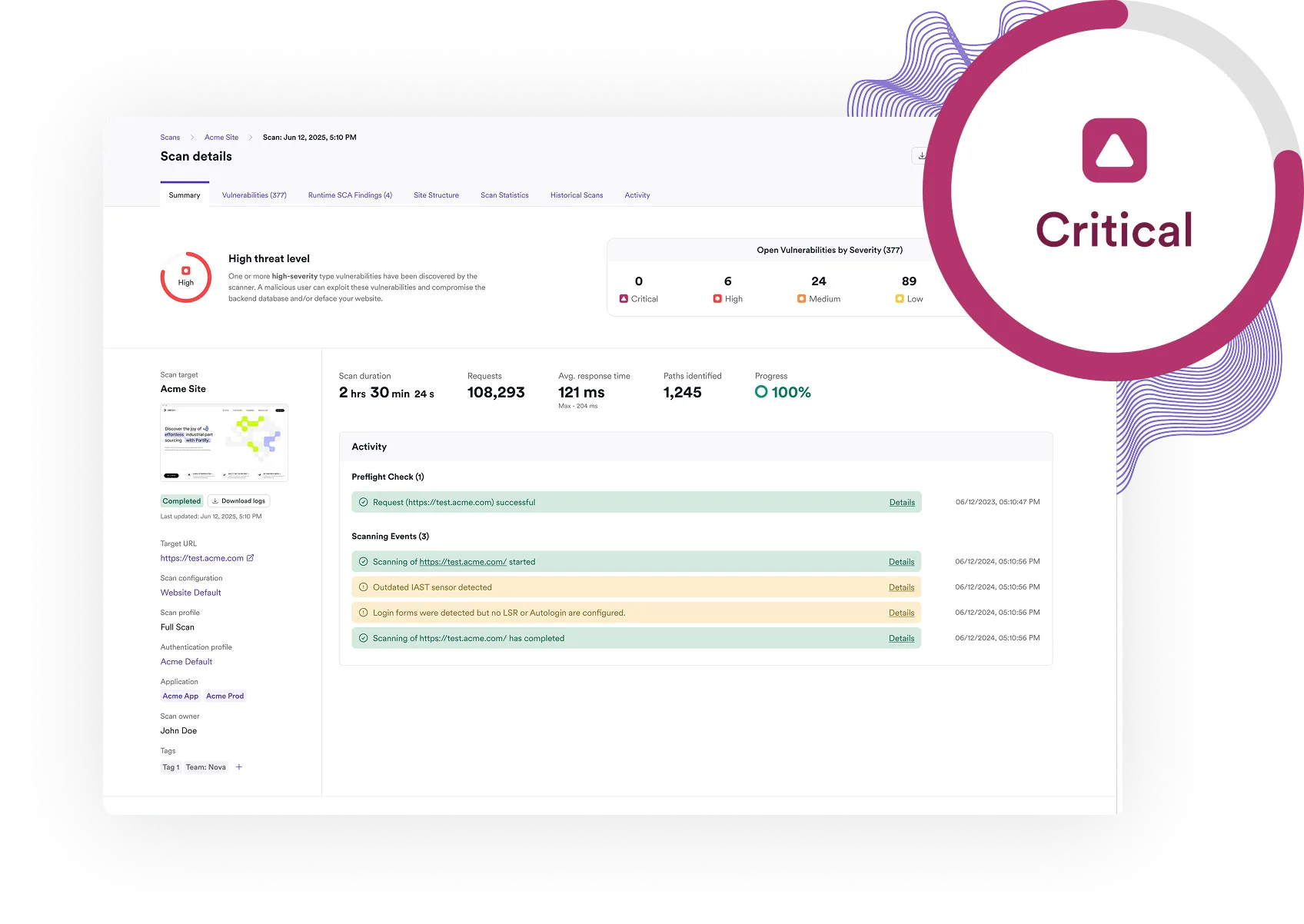
Proof-based scanning with database-level evidence
Invicti’s proof-based scanning technology can safely exploit many SQL injection vulnerabilities to confirm they are real. For SQL injection, this means going beyond detection to:
- Extract data directly from the database in a controlled manner
- Confirm that malicious SQL commands could be executed
- Demonstrate the real impact of the vulnerability
This includes advanced techniques such as:
- Blind SQL injection validation using time-based or boolean responses
- Out-of-band verification where needed
- Safe confirmation of data exposure without harming the application
Each confirmed issue includes clear evidence, showing exactly how data was retrieved via the vulnerability.

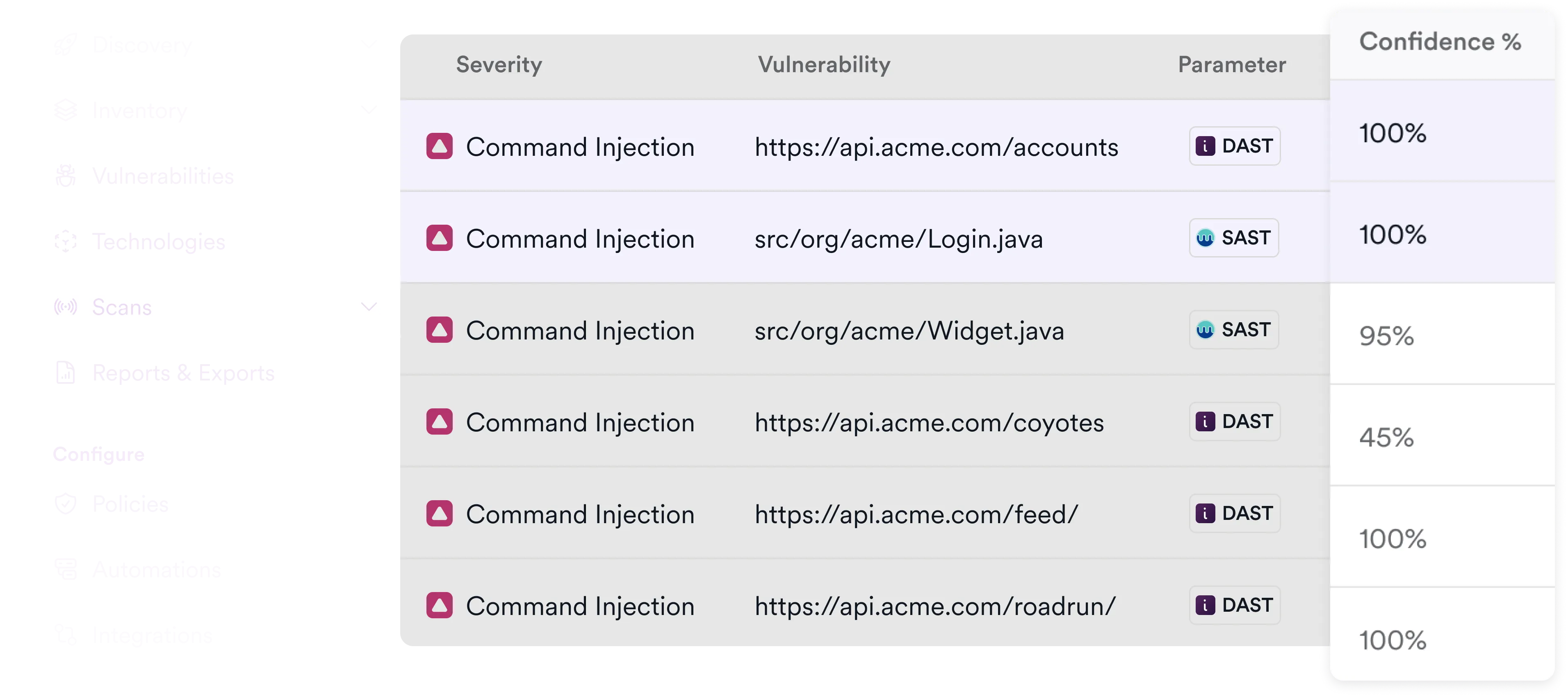
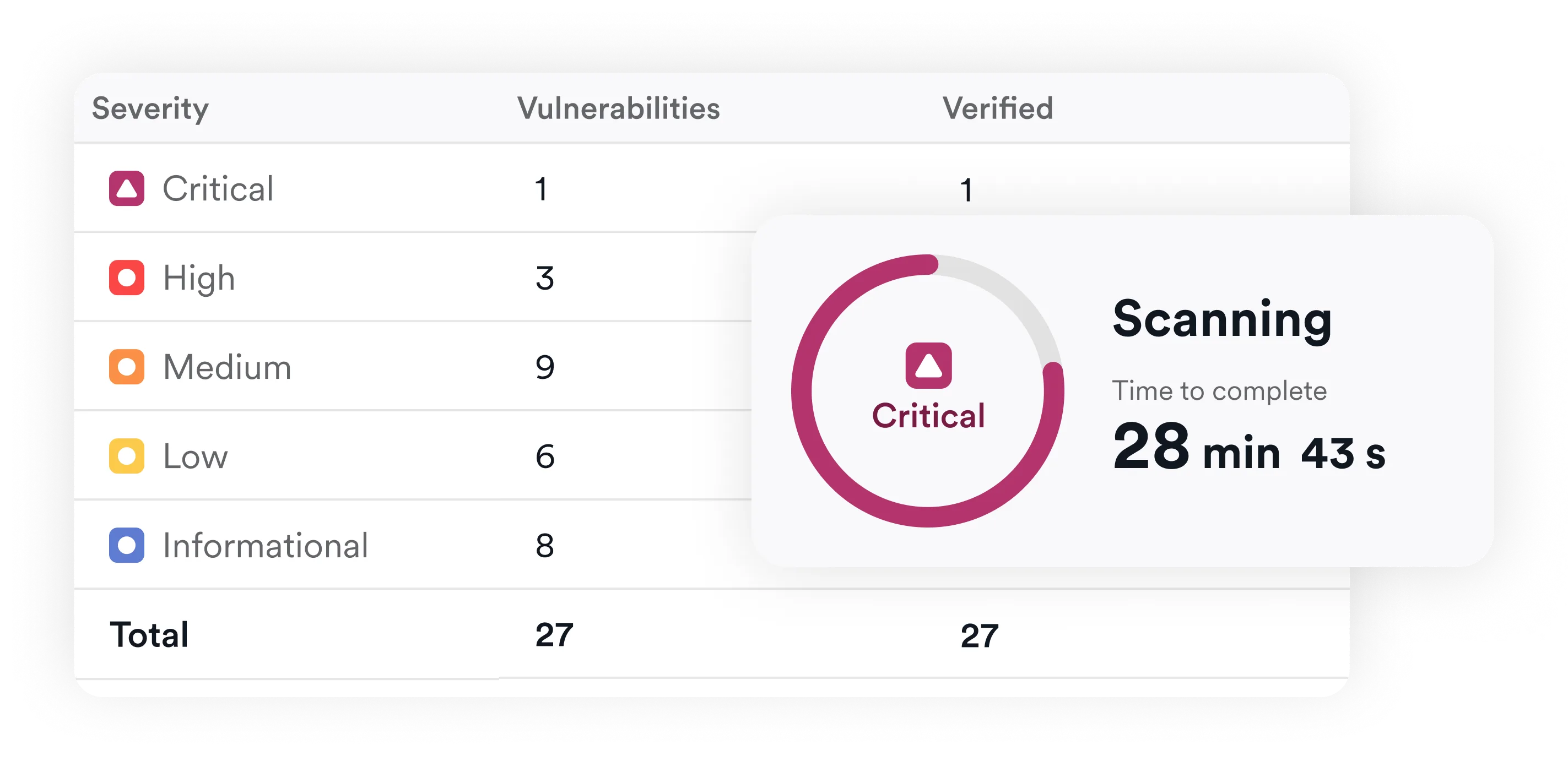
Eliminate false positives and security noise
Traditional vulnerability scanners can generate large volumes of unverified findings, even for long-standing issues like SQLi. This creates friction between security and development teams, who must manually validate whether a reported issue is real.
Invicti removes much of this uncertainty by:
- Validating vulnerabilities automatically
- Confirming exploitability instead of relying on assumptions
- Reducing noise from non-exploitable security vulnerabilities
This allows teams to focus on fixing real issues instead of chasing false alarms.
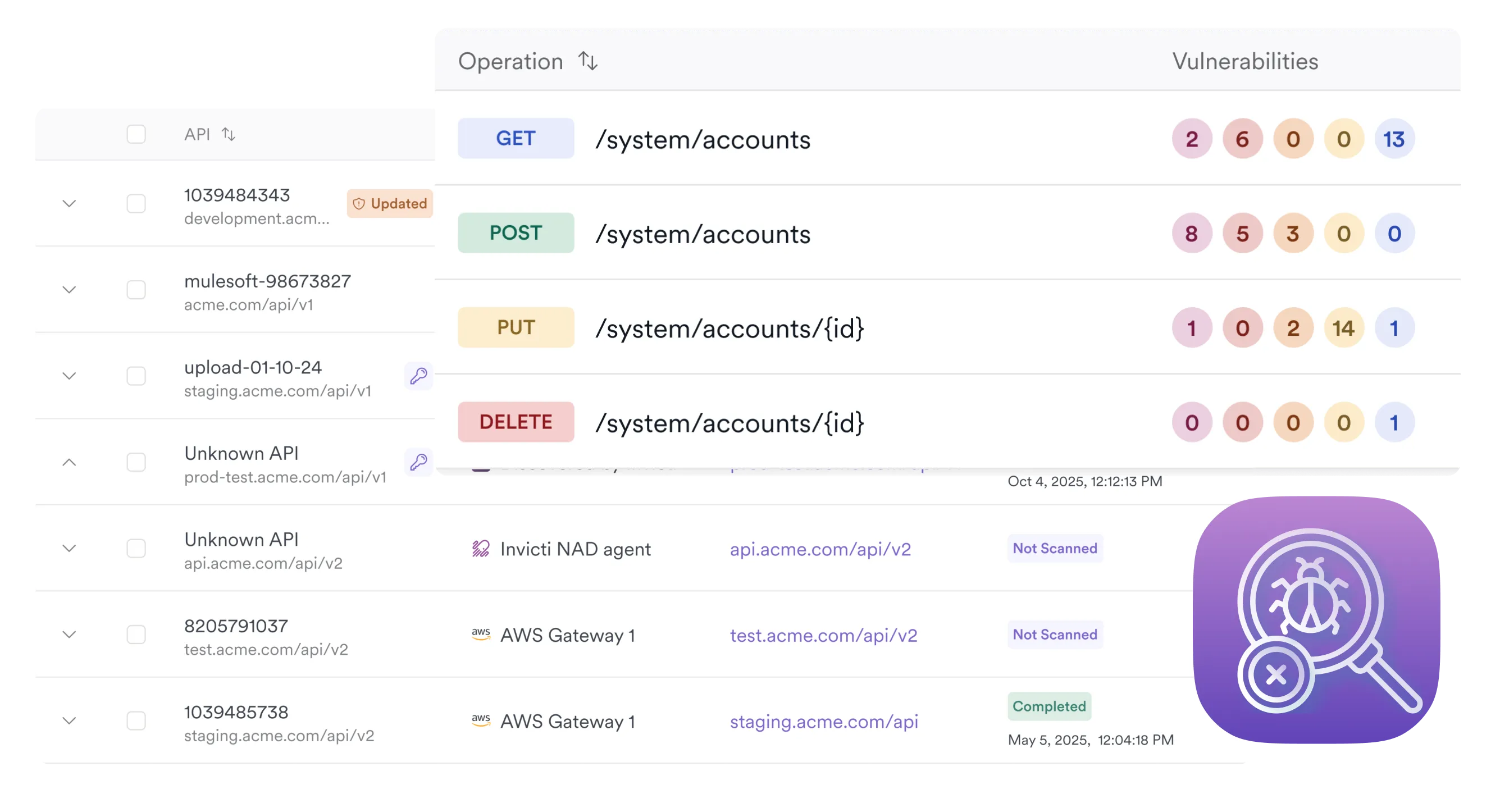
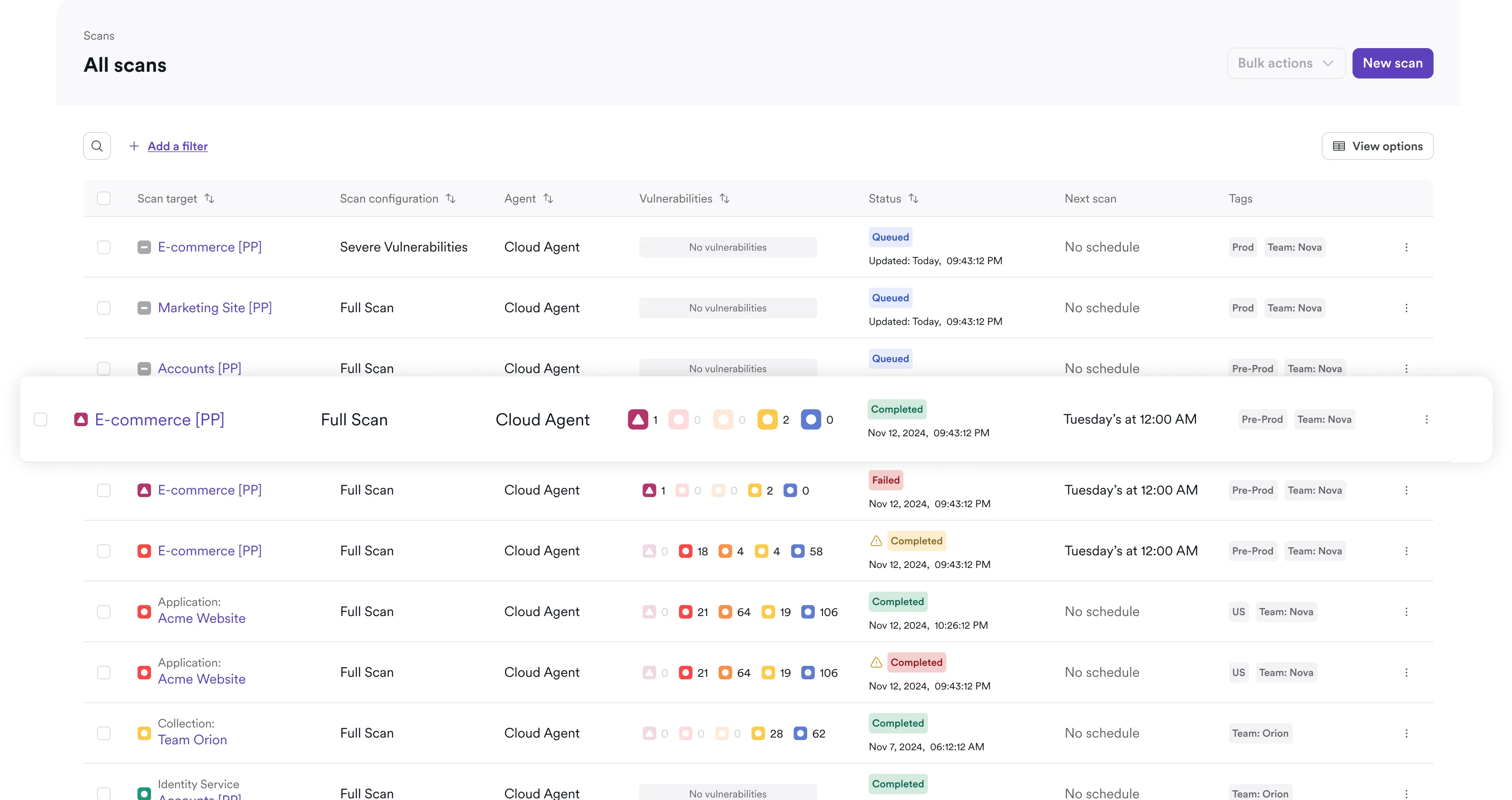
Continuous SQL injection testing across modern applications
Modern applications rely on APIs, microservices, and distributed architectures, so SQL injection testing can’t be limited to just probing form inputs. Invicti supports automated testing across:
- Web applications and web servers
- REST and GraphQL APIs
- Cloud-native and microservices environments
Capabilities include:
- Scheduled and on-demand vulnerability scanning
- CI/CD integration for automated security testing
- Incremental scanning for application updates
- Automatic validation after fixes
This helps to maintain consistent coverage as applications evolve.

Built for DevSecOps and automated remediation
Invicti integrates directly into development workflows to make SQL injection testing and vulnerability scanning in general a routine part of everyday development.
CI/CD and development integrations
- GitHub, GitLab, Azure DevOps, Jenkins, Bitbucket
- Automated scanning during builds and pull requests
- Enforcement of security policies before deployment
Issue tracking and collaboration
- Jira, GitHub Issues, Azure DevOps Boards, ServiceNow, Slack
- Automatic ticket creation with full context
- Detailed reproduction steps including HTTP request data and payloads
- Built-in validation guidance for faster fixes
This streamlines remediation and improves collaboration between security and development teams.
Why SQL injection still matters
SQL injection remains a core risk because of its direct impact on data and systems. Successful SQL injection attacks continue to be used in real-life attack chains and can:
- Expose sensitive data from databases
- Bypass authentication and authorization controls
- Add, manipulate, or delete records
- Execute unintended functionality on the server side
Despite advances in secure coding and the growing use of data stores other than relational databases, SQL injection continues to appear in real-world breaches due to improper input validation and complex application logic.
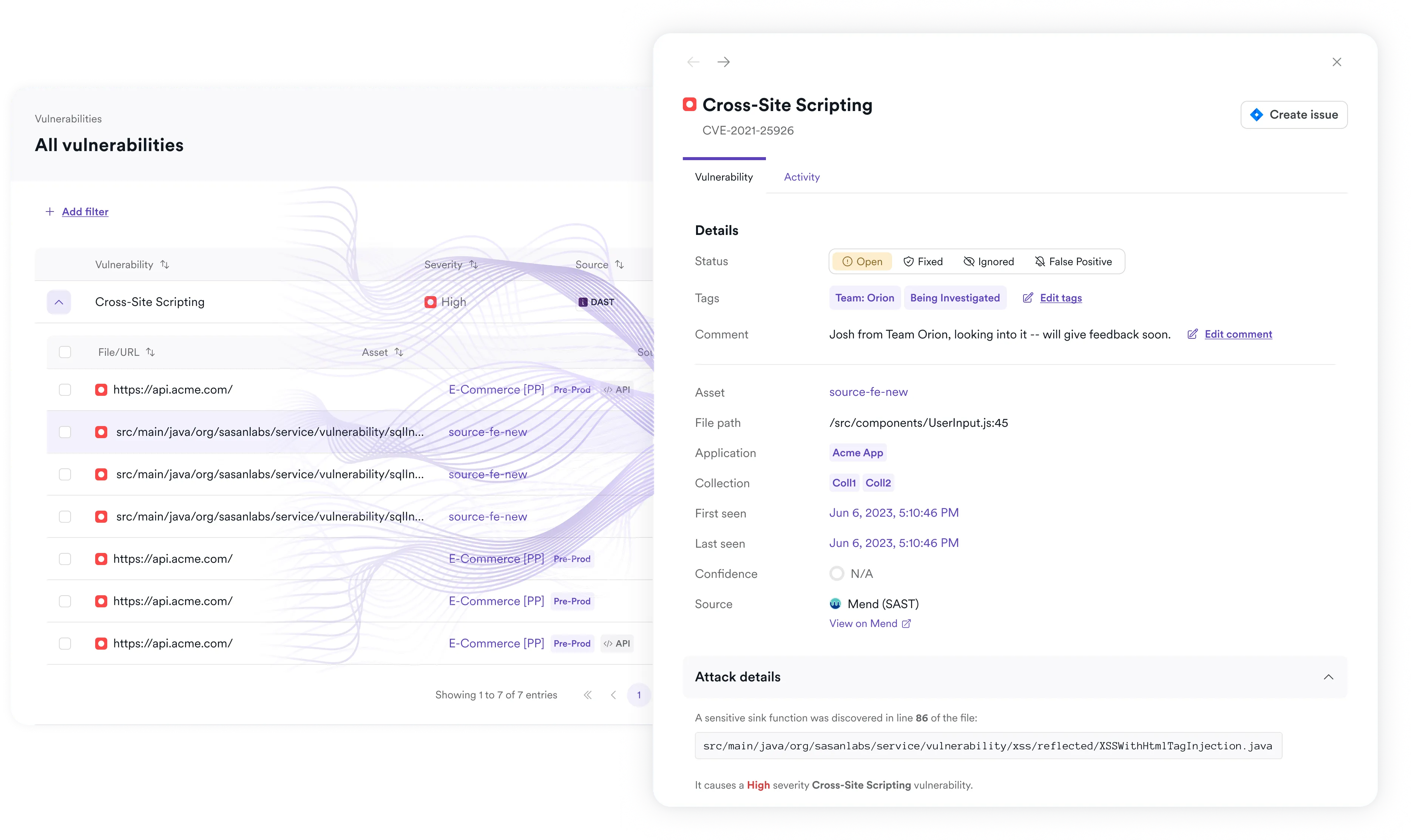
SQLi detection as part of a unified application security platform
Invicti’s SQL injection scanner is part of a broader platform designed to secure modern applications. The platform combines:
- DAST for runtime vulnerability detection
- API security testing and discovery
- Built-in and integrated AST tools like SAST, SCA, secrets scanning, and more
- Application security posture management (ASPM)
- Predictive Risk Scoring and other AI-powered enhancements
This unified approach enables:
- Centralized visibility across assets
- Risk-based prioritization of vulnerabilities
- Consistent coverage across web application security and APIs
DAST on the Invicti Platform also detects hundreds of vulnerabilities besides SQLi, including cross-site scripting (XSS), command injection, remote code execution, misconfigurations, and many more.
A SQL injection scanner is a type of web vulnerability scanner that tests applications for vulnerabilities allowing attackers to manipulate SQL queries through user input. SQLi scanning can be done using a dedicated tool or included as part of a DAST solution.
DAST on the Invicti Platform sends crafted payloads in HTTP requests to test how applications process input and execute SQL statements. Direct and indirect application responses are analyzed to detect unsafe behavior in server-side logic.
Invicti’s DAST uses proof-based scanning to safely exploit many SQLi vulnerabilities and extract sample data from the database to confirm that an injection flaw is real and exploitable.
Yes. Invicti supports automated vulnerability scanning in CI/CD pipelines, which enables continuous testing throughout development.
Yes. In addition to SQL injection, Invicti’s DAST can detect cross-site scripting (XSS), security misconfigurations, and many other security vulnerabilities across modern applications and APIs.

