Pentesting has evolved
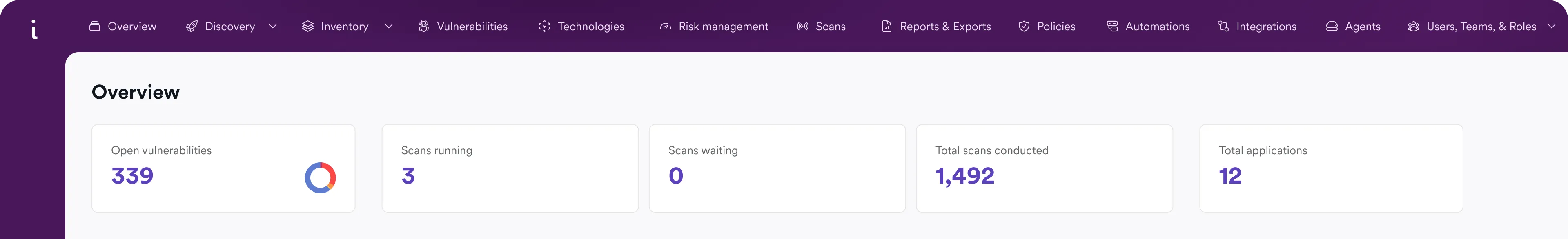
Invicti covers the gaps left by manual penetration testing. Stay secure with automatic pentesting that's validated, continuous, and scalable.

3600+ Top Organizations Trust Invicti
























The problem with legacy pentesting
Legacy pentesting is slow, expensive, and limited to a moment in time. This leaves long gaps for new vulnerabilities to slip through. Results arrive weeks after testing and often contain unverified vulnerabilities that slow teams down. This inconsistent coverage and lack of workflow integration prevents application security from scaling.
Speed
Pentests take weeks to schedule and even longer to deliver results. By the time reports arrive, code has changed and new vulnerabilities have already slipped through.
Coverage
Legacy testing provides only a brief snapshot in time. It can’t keep up with constantly changing applications, APIs, LLMs and environments.
Scale
Manual testing drains time and resources with each new app added to the portfolio. As attack surfaces expand, orgs can't maintain consistent visibility or repeatable results across hundreds of assets.
Always on. Always accurate.
With proof-based scanning, Invicti safely exploits real flaws to deliver proof you can act on immediately, eliminating backlog delays.
Complete asset coverage, known and unknown.
Invicti doesn’t just scan what you know, it uncovers what you don’t and tests what manual pentesters might miss.

More assets, less worry.
Invicti is built for enterprise scale, scanning complex web applications without slowing you down. It handles dynamic apps, APIs, single page applications (SPAs), and authenticated workflows with ease.
Future-proof pentesting with Invicti DAST
The industry’s leading DAST engine continues to improve with AI innovations that are closing the gap between automated scanning and manual penetration testing. Our AI innovations not only enhance DAST accuracy but also help remediate risks posed by AI-powered software and AI-aided development.
Frequently asked pentesting questions
Many routine aspects of pentesting can and should be automated, leaving deeper manual investigation to cybersecurity experts. For web applications and APIs, DAST tools can automatically probe for common security weaknesses like SQL injection vulnerabilities before they are found and exploited by bad actors.
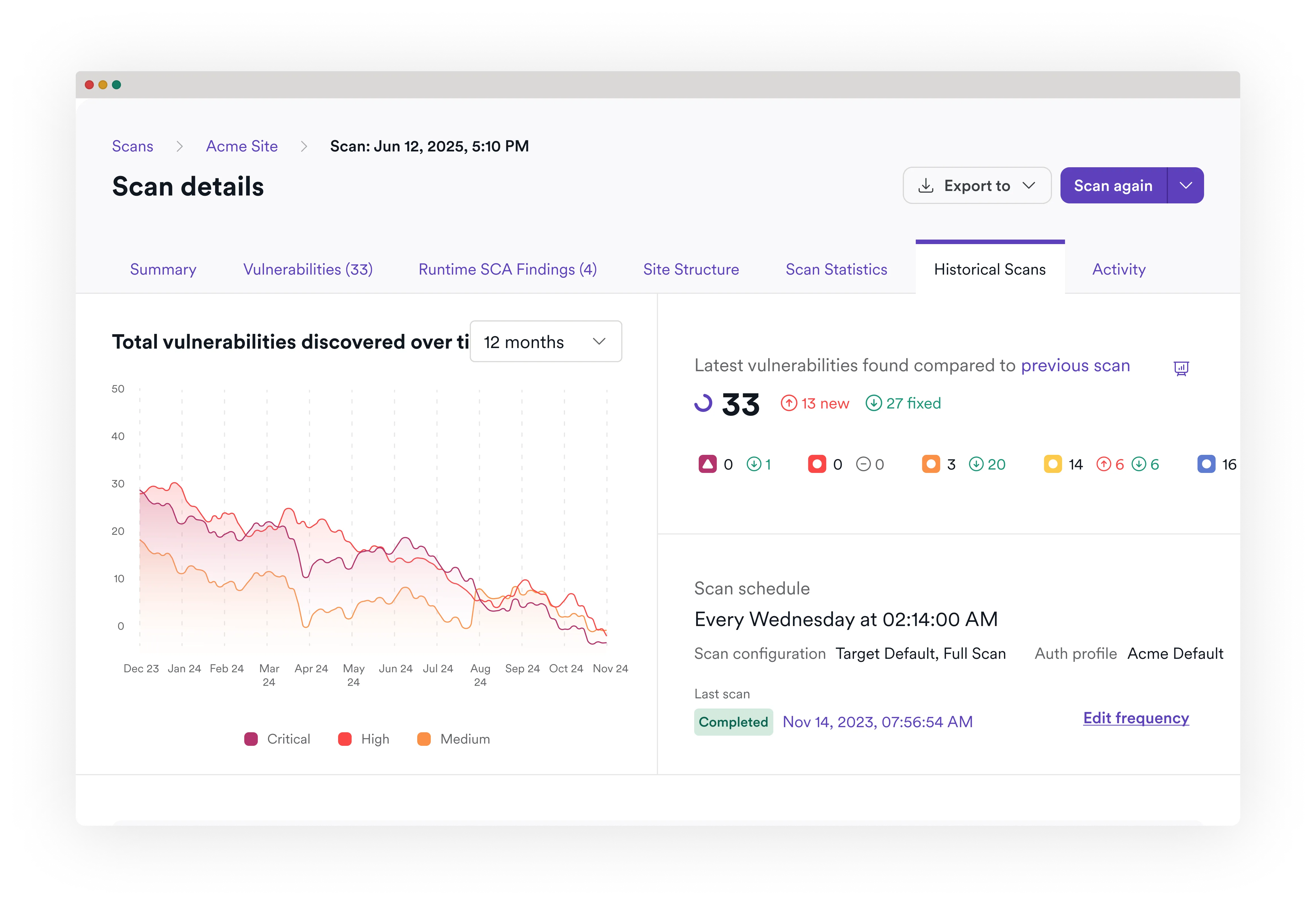
Invicti’s proof-based scanning safely confirms exploitable issues (PoE/PoC), so developers get tickets they can trust. In third-party validations and our long-term user data analysis, confirmed findings achieve 99.98% accuracy.
Yes. Invicti uses advanced checks plus proof/confirmation to surface exploitable issues first, so you don’t end up with “all config, no impact” reports. When combined with additional IAST, reports can even include stack traces or the exact query for faster fixes.
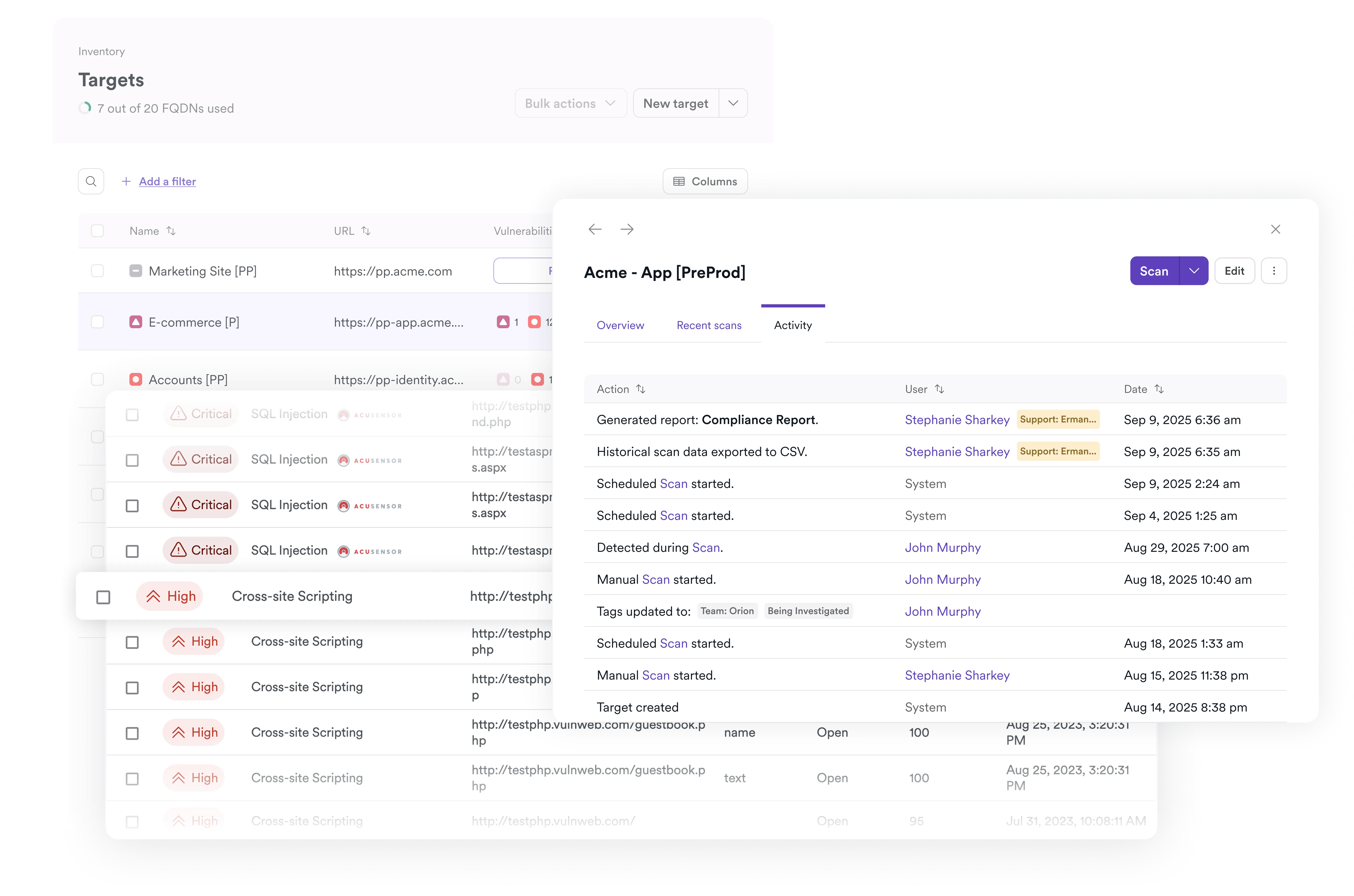
Yes. 110+ out-of-the-box integrations plus a powerful API and open-source CLI let you orchestrate scans in pipelines, push only verified issues to work trackers, enforce gates, and re-test fixes automatically.
ASPM is only as good as its inputs. Invicti feeds runtime-validated, low-noise findings into the posture layer to de-duplicate, correlate, and prioritize what’s actually exploitable so teams fix what reduces risk fastest – all within one platform. Learn more about Invicti ASPM here.
Using your DAST as an automated pentesting tool has the benefit of collating all web vulnerability reports on a single platform for a near-real-time view of your security posture. When DAST is integrated both into security operations and into DevOps, which is the recommended practice, identified security issues can be immediately assigned for remediation.
When Invicti flags a critical vulnerability as verified (SQLi, command injection, etc.), it means it has safely exploited it in a controlled way and includes proof in the report so teams can reproduce and fix without debate. For XSS, we execute a confirmation payload within an embedded browser and attach a working PoC. Read more about how it works here.
Yes. Invicti treats APIs as first-class citizens, ingesting definitions (OpenAPI/Swagger, Postman, WSDL, GraphQL schemas), discovering unknown endpoints, understanding JSON responses, and testing real API risks mapped to the OWASP API Top 10. Learn more about API security here.
Absolutely. You can export the data you need from the full internal API and use built-in dashboards/metrics to track MTTR, SLA adherence, and posture trends across apps, business units, and environments – and then share executive-ready reports.
Unlike many other vendors, Invicti provides flexible licensing that matches the way you build and operate your applications and lets you scan as often as you need. Learn more about Invicti pricing here.
Automate pentesting with Invicti