What is application vulnerability management?
Application vulnerability management is the continuous process of discovering, prioritizing, remediating, and verifying security issues across web applications and APIs.
On the Invicti Platform, vulnerability management goes fat beyond running scans – it helps teams focus on real, exploitable risk, reduce noise, and improve security outcomes across the software development lifecycle.


3600+ Top Organizations Trust Invicti
















Vulnerability management defined
Vulnerability management is the continuous process of identifying, assessing, fixing, and verifying security weaknesses. It includes scanning, but also the decisions and workflows that determine what gets fixed and how quickly.
In application security, this scope includes running web applications, APIs, and their underlying components. Modern environments generate large volumes of findings, many of which are not exploitable. Without validation, teams are left guessing which issues actually matter.
A DAST-first approach – using dynamic application security testing (DAST) – addresses this by testing live applications and identifying vulnerabilities that attackers can actually exploit. This shifts vulnerability management from collecting findings to fixing real risk.
Why vulnerability management matters now
Vulnerability management is under pressure from the scale and speed of modern application development. Organizations now manage large portfolios of web applications, microservices, and APIs that change continuously.
At the same time, APIs are expanding the attack surface, often introducing undocumented endpoints that are difficult to track and secure. Combined with faster release cycles and fragmented toolchains, this creates a growing gap between finding vulnerabilities and fixing them.
Security teams are left with too many findings and not enough context. Without clear prioritization and validation, critical vulnerabilities can remain unresolved while teams spend time on issues that do not meaningfully reduce risk.
The five stages of the vulnerability management lifecycle
A structured lifecycle helps teams move from discovery to measurable improvement. Most effective programs follow five core stages:
1. Discover what you need to secure
Discovery starts with identifying all applications, APIs, endpoints, and components across environments. This includes shadow or undocumented assets that may not be part of formal inventories.
Modern platforms support automated attack surface discovery, API imports, and layered API discovery techniques to uncover endpoints beyond known specifications.
2. Identify vulnerabilities
Once assets are known, organizations test them for security issues using a combination of approaches such as dynamic application security testing (DAST), API security testing, static application security testing (SAST), software composition analysis (SCA), container security, and IaC security checks.
Each method provides a different perspective, but also increases the volume of findings that must be managed.
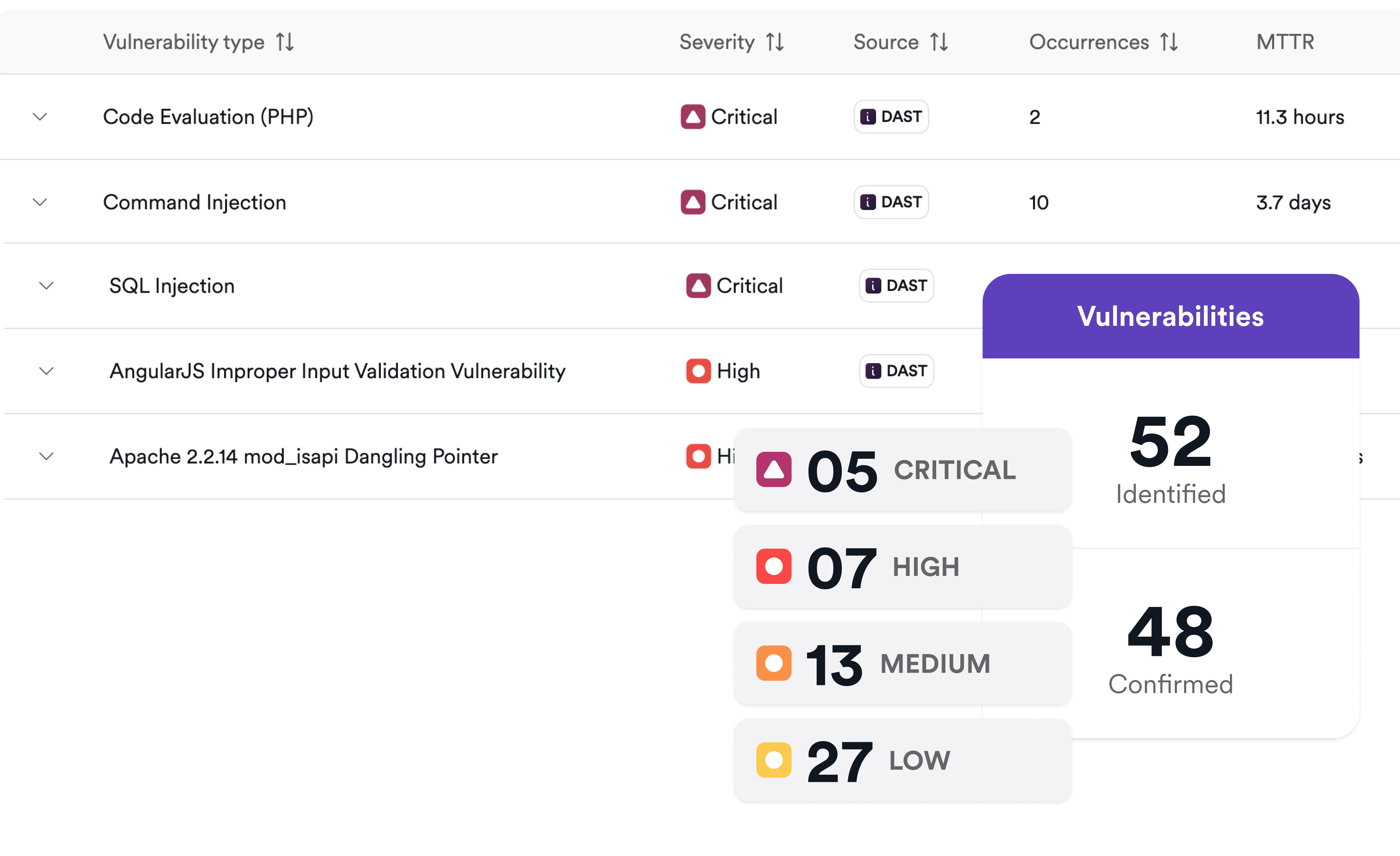
3. Prioritize based on real risk
Effective prioritization focuses on what matters most by considering exploitability, business impact, exposure, and duplication across tools.
Centralized platforms help correlate findings, remove duplicates, and apply business context and threat intelligence. This allows teams to focus on vulnerabilities that are both exploitable and relevant to the organization.
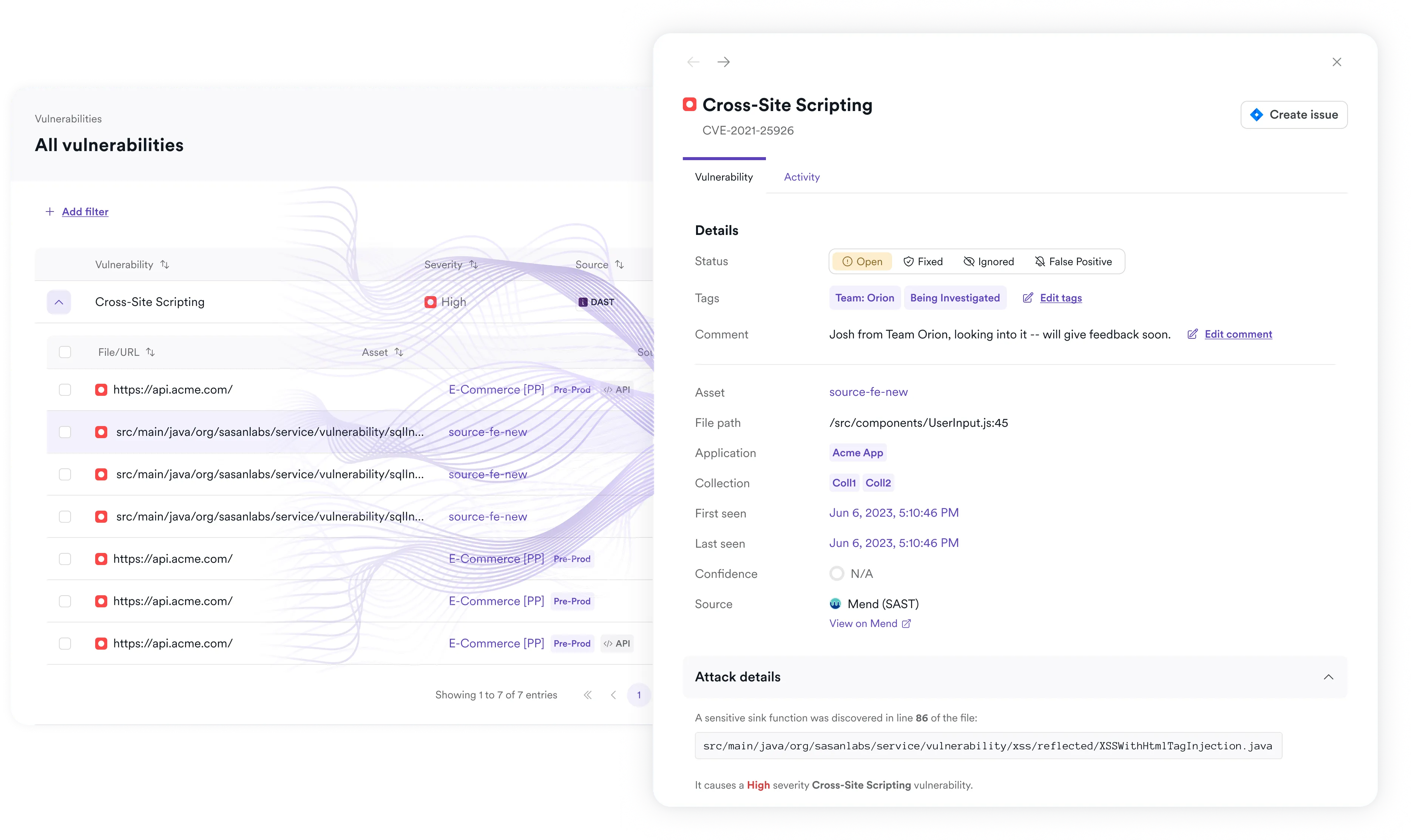
4. Remediate and retest
Findings must translate into action through developer workflows. This includes creating actionable tickets, integrating with issue trackers, and providing clear remediation guidance.
Automated retesting ensures that fixes are validated. Without verification, teams cannot be certain that vulnerabilities are fully resolved.
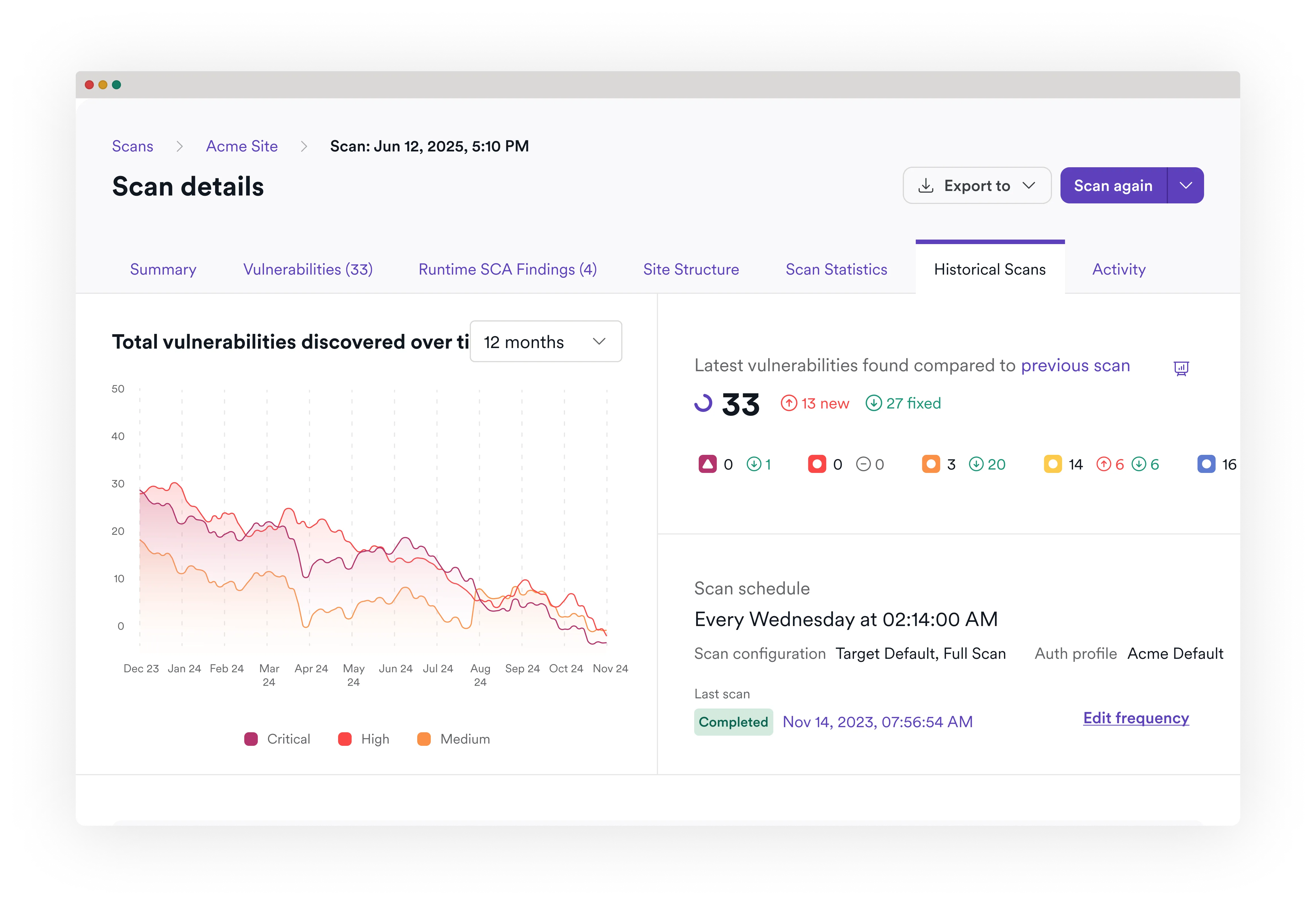
5. Measure and improve
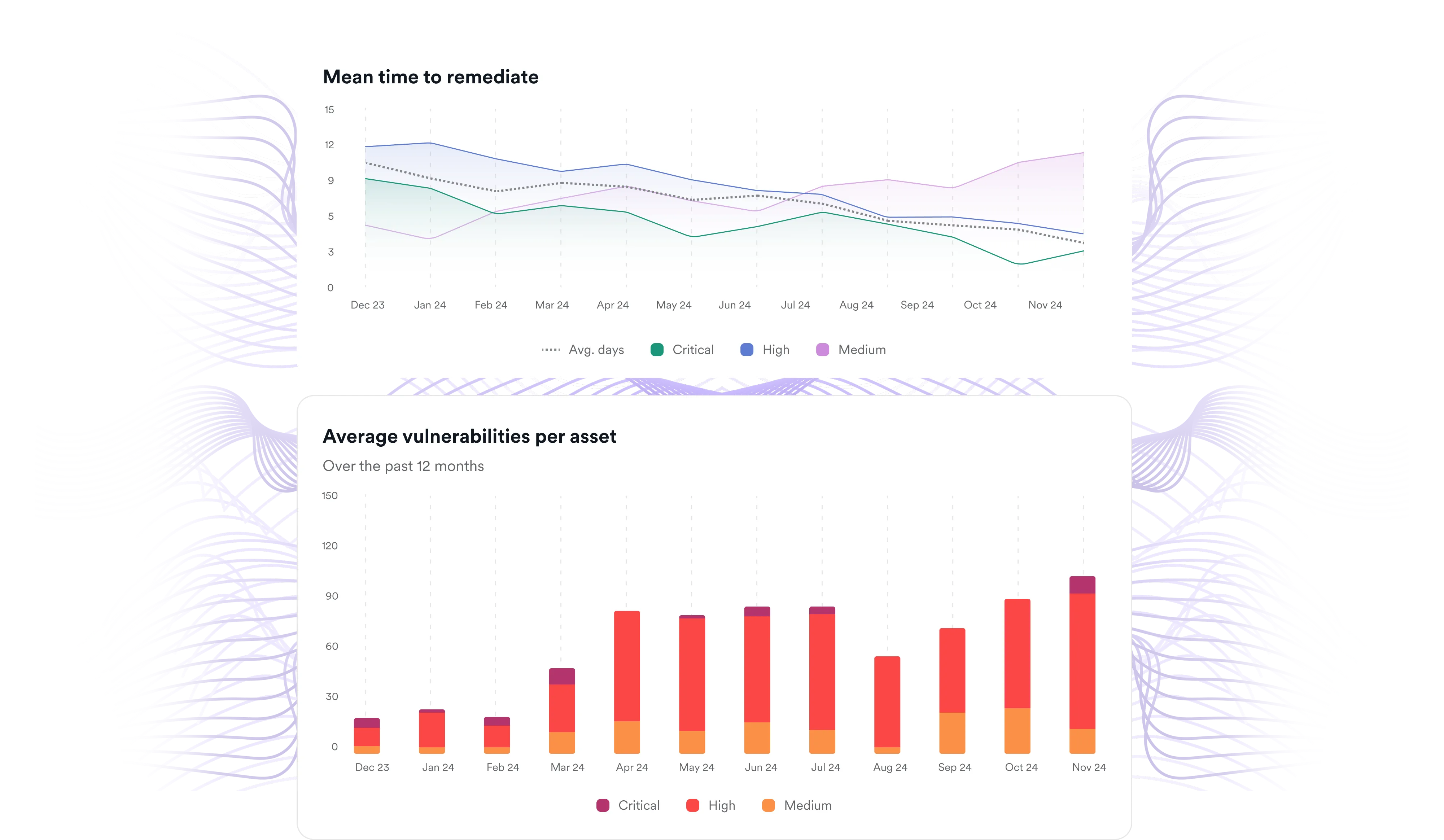
A mature program tracks metrics such as mean time to remediation (MTTR), vulnerability aging, and SLA compliance. These insights help teams identify bottlenecks, improve processes, and demonstrate progress over time, supporting both security outcomes and audit readiness.
.svg)
What good vulnerability management looks like
A mature application vulnerability management program consistently demonstrates a few key characteristics:
- Complete visibility across applications, APIs, and components
- Validated findings that focus on real, exploitable vulnerabilities
- Risk-based prioritization aligned to business impact
- Automated remediation workflows integrated with development
- Continuous retesting and reporting to track improvement
Together, these elements help organizations move from reactive scanning to a structured, measurable approach to reducing risk.
Vulnerability management vs vulnerability scanning
Vulnerability scanning is a single step within a broader process. Vulnerability scanning finds security issues, while vulnerability management ensures the right issues are fixed, validated, and continuously improved.
Vulnerability scanning:
- Identifies potential security issues
- Produces raw findings
- Often generates high volumes of alerts
- Stops at detection
Vulnerability management
- Governs the full lifecycle from discovery to remediation
- Validates, prioritizes, and operationalizes findings
- Focuses on reducing noise and highlighting real risk
- Includes remediation, retesting, and reporting
What makes vulnerability management challenging at scale
Many organizations struggle with vulnerability management because their tools and processes do not work together effectively, which becomes especially problematic at scale. Common challenges include:
- High volumes of unvalidated findings that create noise
- Fragmented toolchains operating in silos
- Incomplete visibility across applications and APIs
- Rapid API growth expanding the attack surface
- Slow remediation due to inefficient handoffs
These challenges are not solved by just adding more tools. They require better coordination, clearer prioritization, and a focus on validated risk.

What modern teams need from their tooling
To manage vulnerabilities effectively at scale, teams need capabilities that support the full lifecycle and reduce operational friction. Key requirements include:
- Runtime validation to confirm exploitability
- Unified visibility across findings from multiple sources
- API discovery and API security testing to expand coverage
- Integration with CI/CD pipelines and issue tracking systems
- Developer-ready remediation guidance
- Continuous retesting and reporting
How Invicti supports application vulnerability management
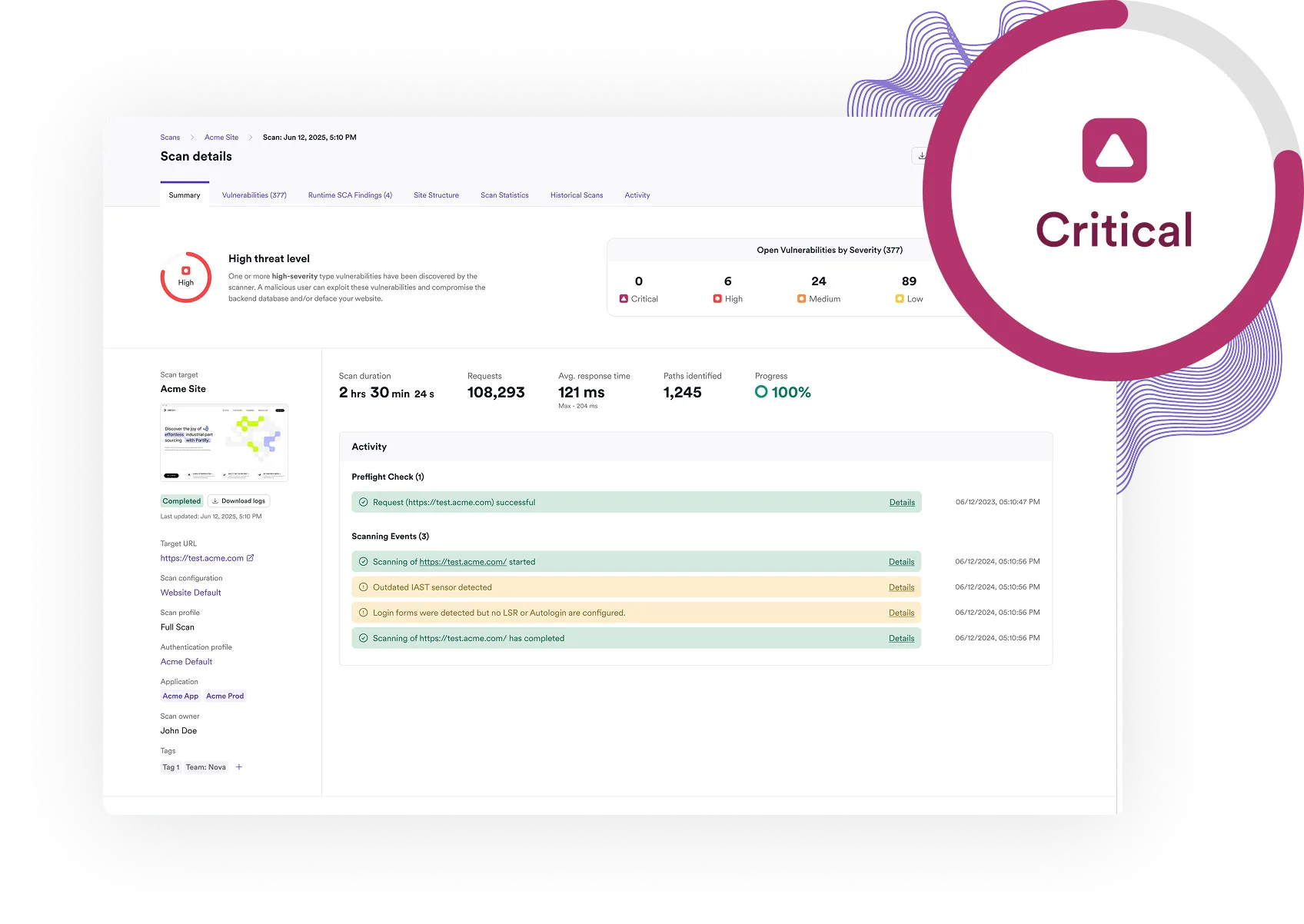
The Invicti Application Security Platform supports the full application vulnerability management lifecycle – from discovery to remediation and reporting. Its DAST-first foundation provides a runtime view of application and API security to helping teams identify vulnerabilities that are accessible and exploitable. This ensures that testing focuses on real-world risk rather than theoretical findings.
Invicti’s proof-based scanning strengthens this approach by confirming exploitability for many common vulnerabilities with an accuracy of 99.98%. This greatly reduces false positives overall and ensures that results are actionable for both security and development teams.
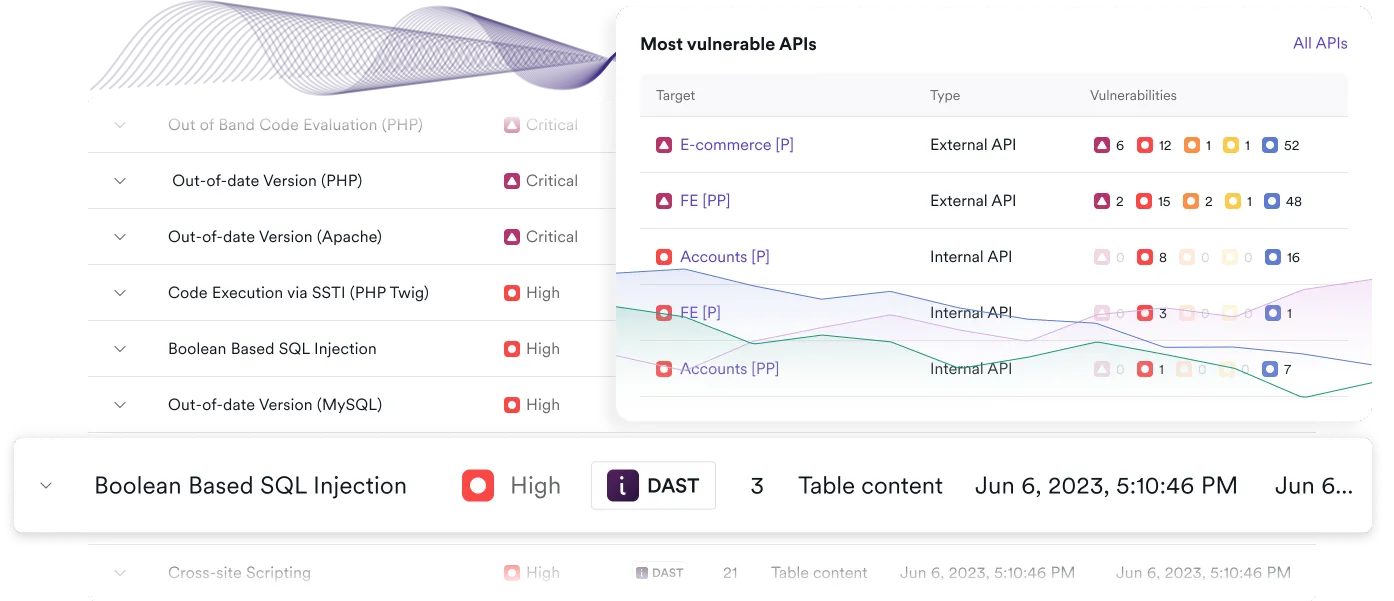
Invicti ASPM acts as the orchestration layer across the Invicti Platform. It centralizes findings from DAST, API security, SAST, SCA, container security, and integrated sources. It then correlates and deduplicates those findings, applies business context, and enables risk-based prioritization.
With built-in workflow automation, reporting, and integrations, Invicti ASPM helps teams operationalize remediation at scale. The result is a unified approach to vulnerability management that emphasizes validated risk, efficient workflows, and continuous improvement.
See how Invicti helps teams validate, prioritize, and remediate application vulnerabilities with DAST-first AppSec and proof-based ASPM. Request a demo to see the Invicti Platform in action in your application and API environments.