The HIPAA vulnerability scanner built for covered entities
Healthcare organizations are entering a new phase of HIPAA enforcement. Proposed updates to the HIPAA Security Rule move beyond flexible guidance toward prescriptive, testable controls – including defined vulnerability scanning cadences, stronger authentication requirements, and stricter expectations for continuous risk analysis.
For CISOs, compliance officers, and AppSec teams, the implication is clear: vulnerability scanning is no longer a periodic checkbox exercise. It must be continuous, auditable, and tied directly to real risk in systems that process electronic protected health information (ePHI).
The stakes here are higher than in any other industry. According to IBM’s Cost of a Data Breach Report, healthcare has been the costliest sector for data breaches for 14 consecutive years, underscoring the financial impact of failing to secure ePHI.
Invicti helps healthcare organizations operationalize HIPAA-aligned vulnerability management with a DAST-first approach built around proof-based scanning that identifies, validates, and prioritizes real, exploitable risks in web applications and APIs – the systems attackers actually target.

3600+ Top Organizations Trust Invicti
























Translate HIPAA security rule requirements into testable controls
HIPAA does not prescribe specific tools – it defines outcomes. Covered entities and business associates must implement safeguards to protect ePHI, particularly across:
- Risk analysis and risk management (§164.308(a)(1))
- Access control (§164.312(a))
- Audit controls (§164.312(b))
- Integrity (§164.312(c))
- Transmission security (§164.312(e))
The focus on risk analysis is not theoretical. Industry analysis by Clearwater Security has found that inadequate risk analysis was a factor in roughly 90% of HIPAA Security Rule enforcement actions, making it the single most common compliance failure.
In practice, covering the requirements originating from the HIPAA Security Rule (45 CFR Part 164) depends heavily on application security testing. Modern healthcare environments rely on web applications, APIs, and interconnected services to process ePHI, making them a primary attack surface.
Invicti enables teams to translate these regulatory requirements into continuous, testable controls by:
- Scanning running applications and APIs for exploitable vulnerabilities
- Validating findings to distinguish real risk from noise
- Mapping results to HIPAA-aligned controls for reporting and audit readiness

How Invicti maps to HIPAA security rule requirements
HIPAA defines what must be protected, not how to implement security. For compliance teams, the challenge is demonstrating how technical controls – like vulnerability scanning – support specific safeguards. Here’s how Invicti capabilities align with key HIPAA Security Rule safeguards and proposed updates relevant to application security and ePHI protection:
This mapping helps security and compliance teams demonstrate that vulnerability scanning is not just performed, but directly supports HIPAA-aligned safeguards with measurable, testable outcomes.
Why traditional vulnerability scanners fall short for HIPAA
Most vulnerability scanners were not built for compliance-driven environments. They generate large volumes of findings without clear validation, leaving security and compliance teams with three persistent problems:
- Uncertainty: Are these vulnerabilities real and exploitable?
- Audit risk: Can findings be clearly mapped to HIPAA safeguards?
- Operational friction: How do teams prioritize and remediate at scale?
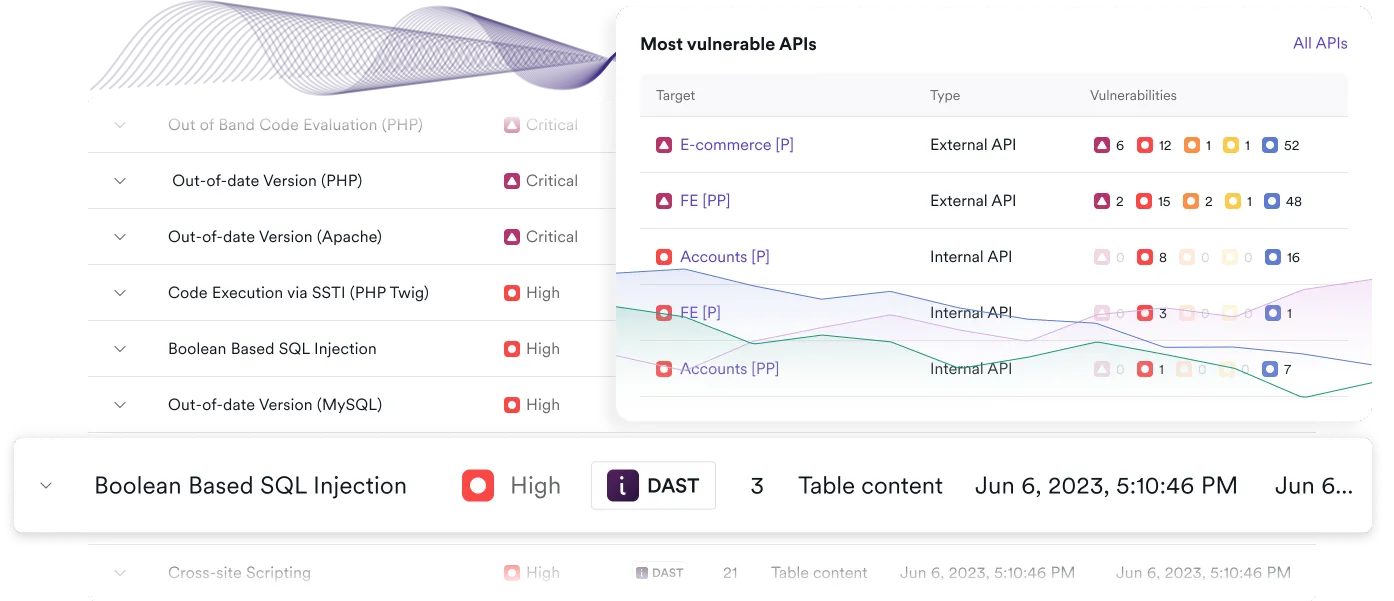
Many traditional scanners also focus primarily on web application frontends while overlooking APIs and dynamically changing assets. In healthcare environments, APIs power patient portals, EHR integrations, mobile applications, and third-party data exchange, often handling sensitive ePHI directly. Without API-aware security testing and continuous discovery, organizations can leave critical exposure points outside the scope of testing.
For healthcare organizations, all this creates a gap between “scanning performed” and “risk understood.” A DAST-first approach addresses this gap by focusing on the vulnerabilities that matter most – those that can actually expose ePHI in production systems.
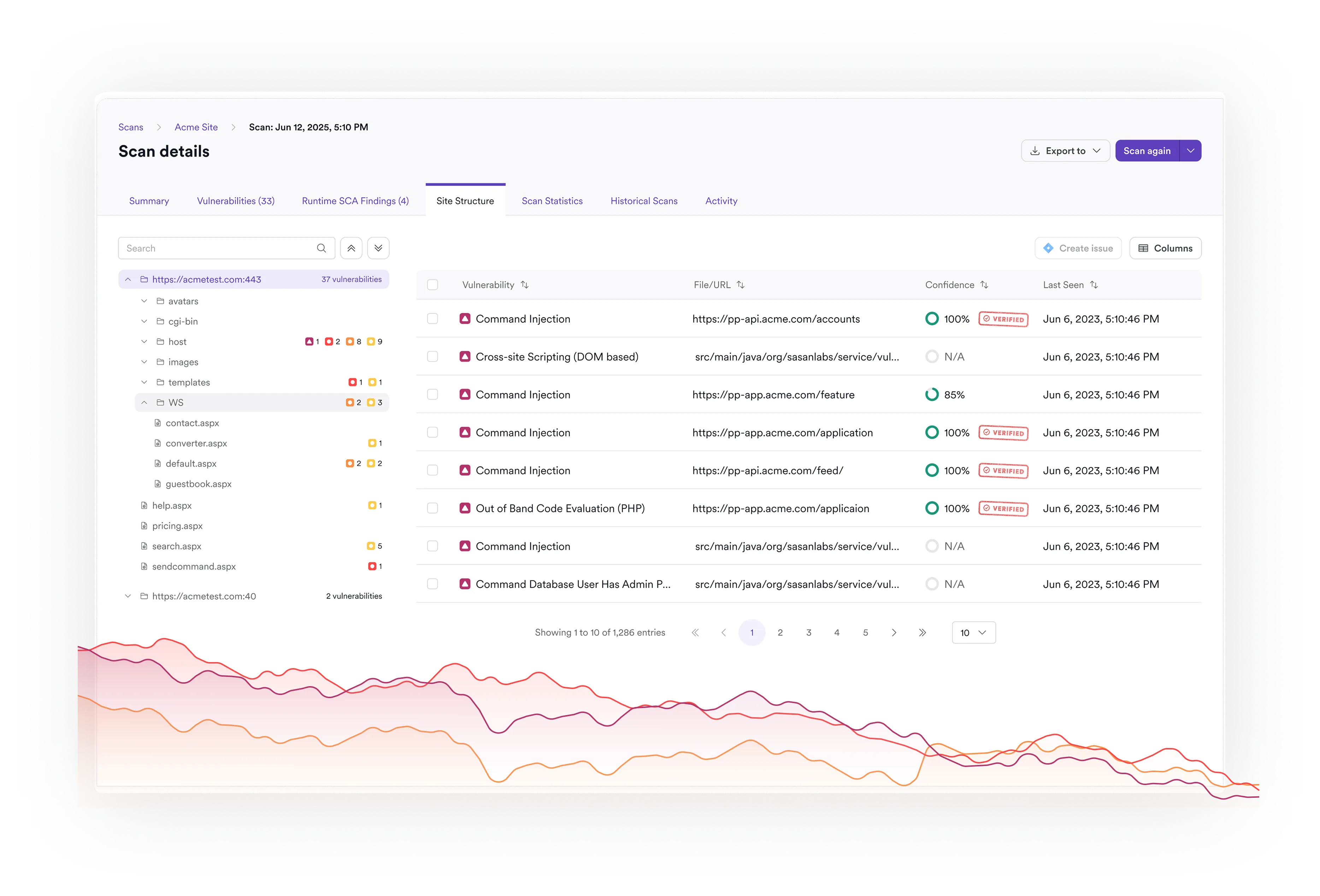
A runtime-validated approach to HIPAA vulnerability scanning
Invicti is built on a DAST-first model that tests applications from the outside in, simulating how attackers interact with real systems. This is critical for HIPAA because it reflects the actual exposure of ePHI in live environments.
With Invicti, teams can:
- Identify vulnerabilities in running applications and APIs that handle ePHI
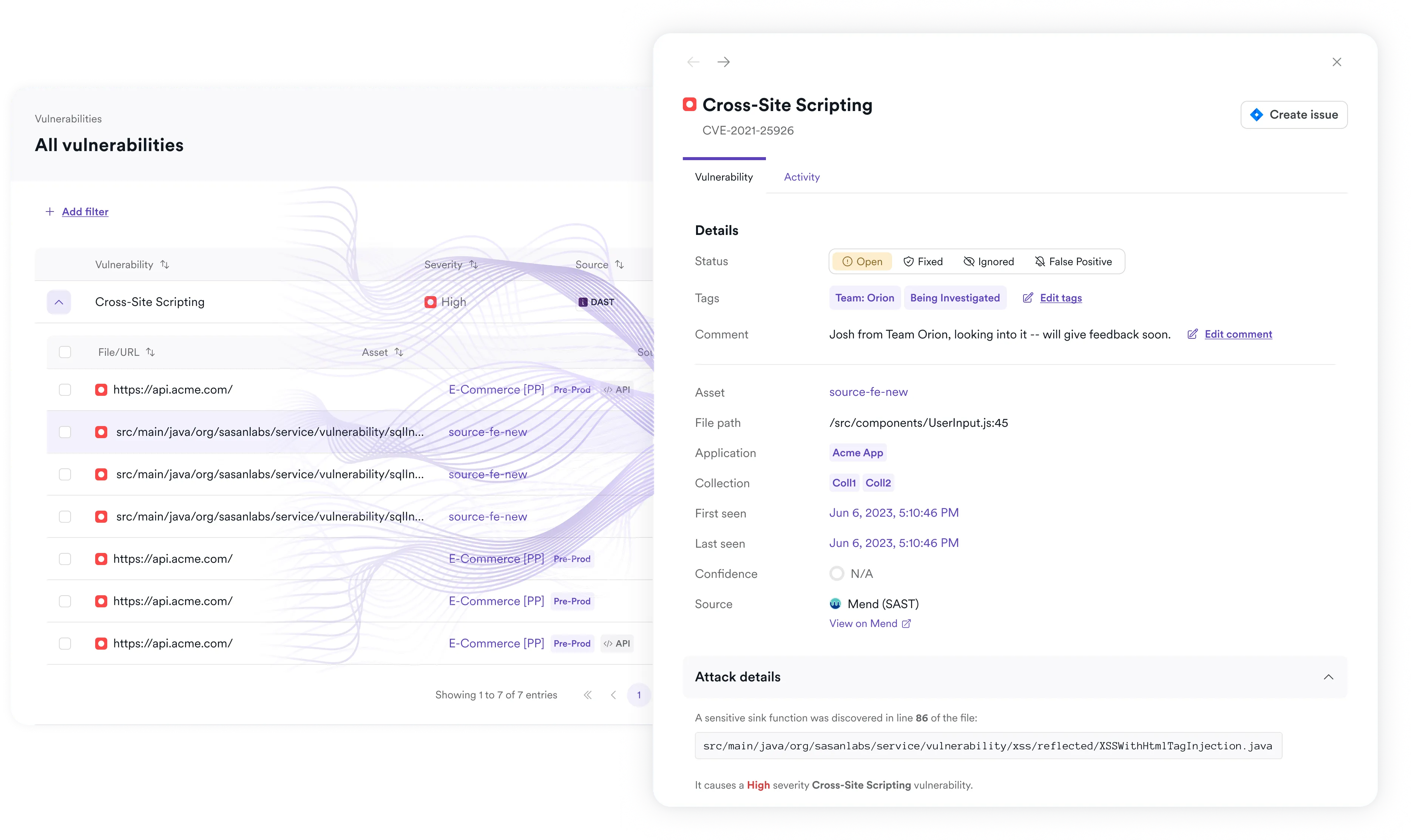
- Confirm exploitability with proof-based validation for many common vulnerabilities
- Prioritize remediation based on real-world risk, not theoretical findings
- Maintain continuous visibility into application security posture
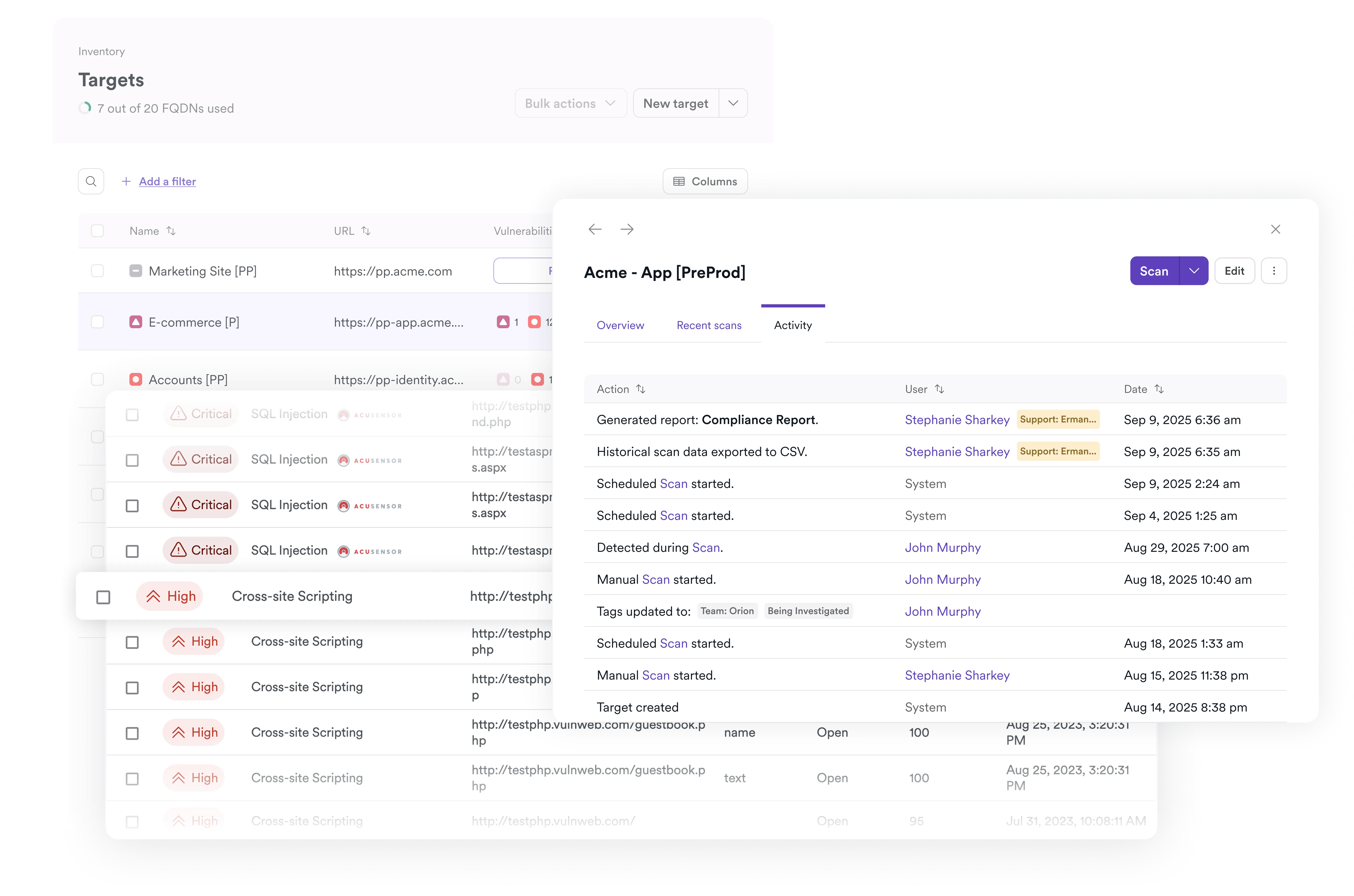
This approach aligns directly with HIPAA’s emphasis on ongoing risk analysis rather than one-time assessments. With Invicti’s automated application and API discovery, teams can also identify unknown or unmanaged assets that could expose ePHI outside approved security processes.
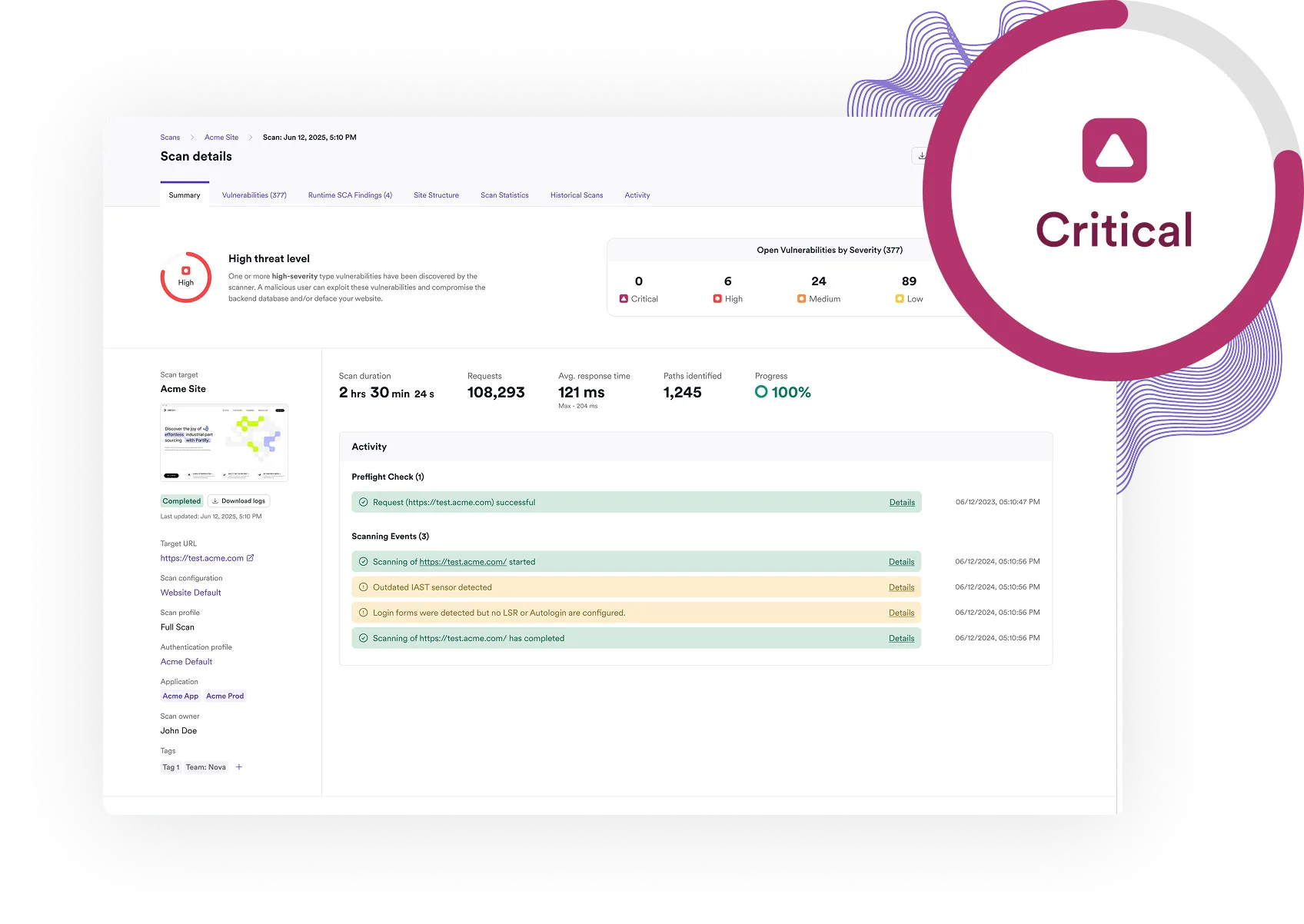
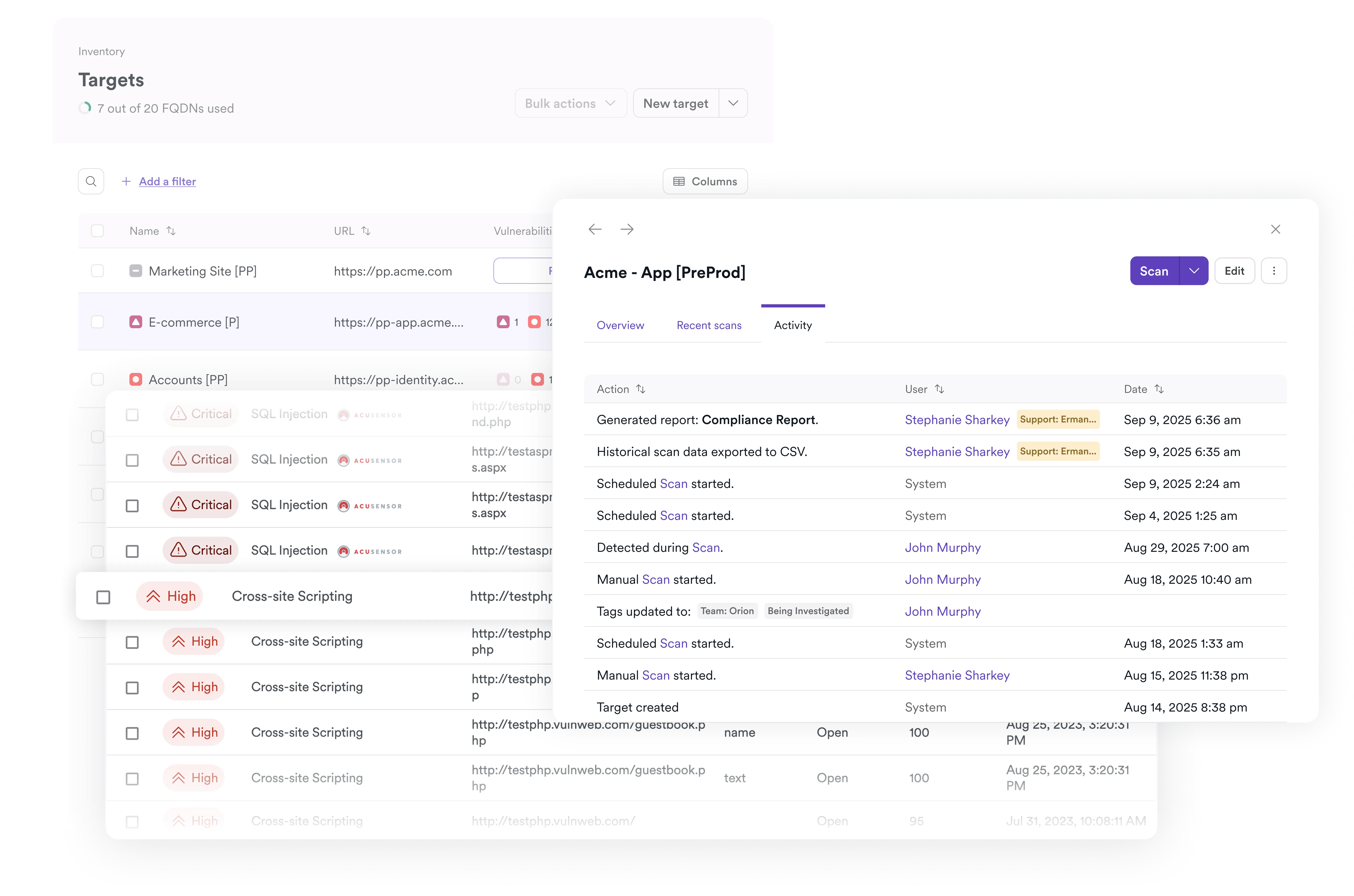
HIPAA-ready reporting for audit and compliance teams
Compliance teams need more than scan results – they need evidence that stands up to auditor scrutiny. Invicti includes a built-in HIPAA compliance report designed to support audit workflows and documentation requirements. The report:
- Maps detected vulnerabilities to relevant HIPAA Security Rule safeguards
- Separates confirmed vulnerabilities from unverified findings
- Provides clear remediation guidance for development teams
- Offers exportable documentation suitable for internal reviews and external audits
This allows security and compliance teams to demonstrate not just that scans are performed, but that risks are identified, validated, and managed in a structured, repeatable way.
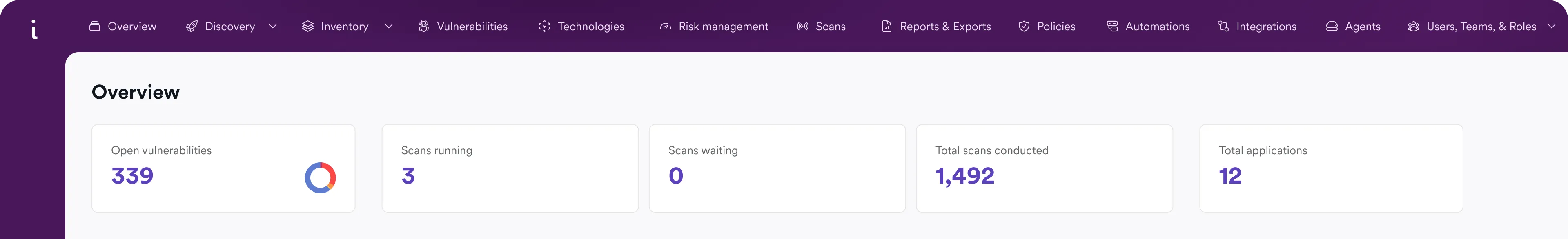
With Invicti’s application security posture management (ASPM) capabilities, teams can consolidate vulnerability data across applications and APIs into a unified view of application risk, simplifying audit preparation and improving remediation tracking for HIPAA-aligned security programs.
Secure the full app and API attack surface for ePHI
Invicti is built on a DAST-first model that tests applications from the outside in, simulating how attackers Modern healthcare systems are API-driven. Patient portals, EHR integrations, mobile apps, and third-party services all rely on APIs to exchange sensitive data. This expands the attack surface beyond traditional web interfaces.
Invicti provides unified security testing across:
- Web applications handling patient data and workflows
- APIs exposing backend services and integrations
- Authentication-protected areas where sensitive data resides
With automated discovery and testing, teams can identify previously unknown assets and ensure that all systems processing ePHI are included in their security program.
interact with real systems. This is critical for HIPAA because it reflects the actual exposure of ePHI in live environments.
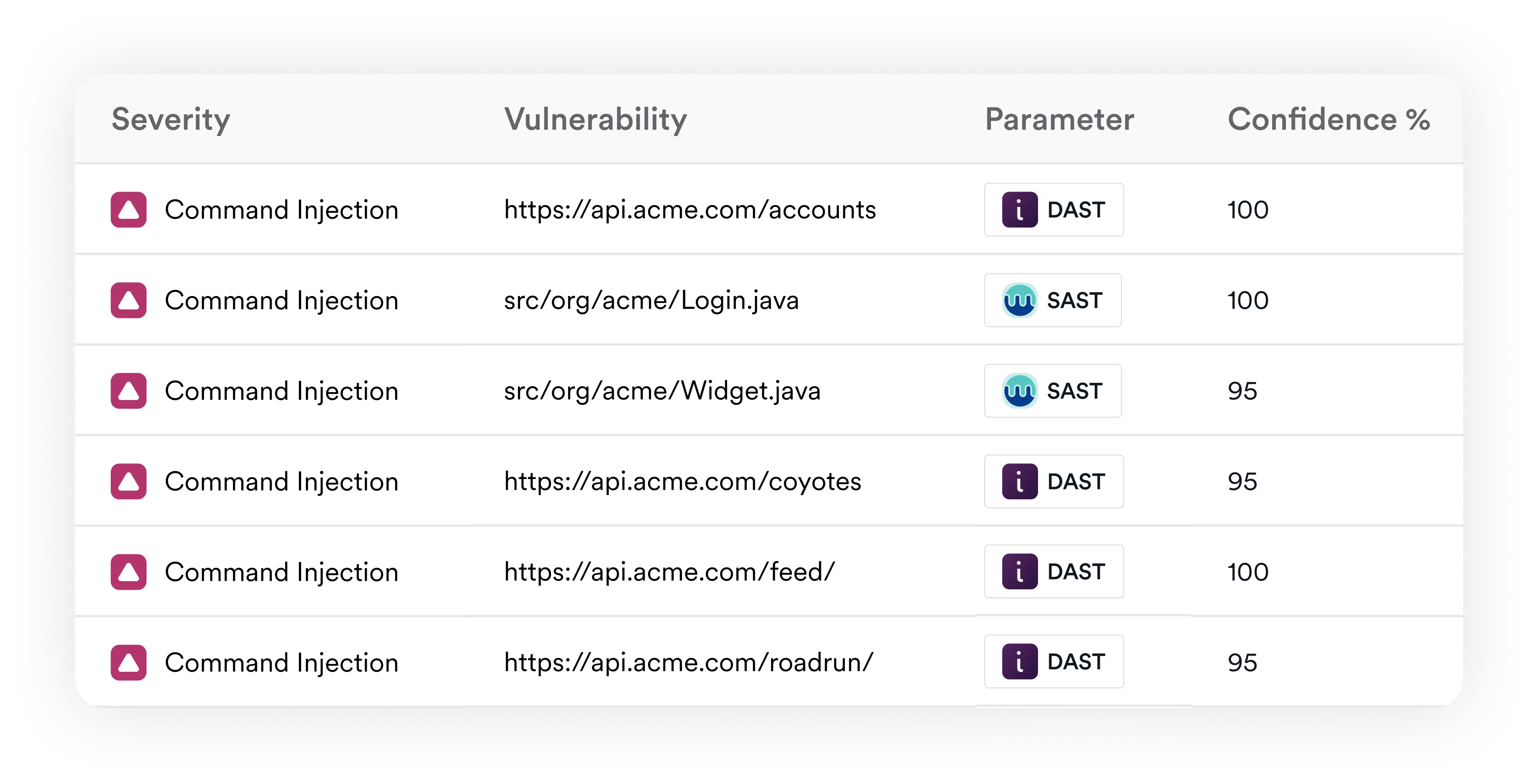
Reduce false positives and accelerate remediation
False positives are more than a nuisance in healthcare – they slow down remediation and create audit risk when teams cannot clearly justify their findings.
Invicti addresses this with proof-based scanning, which automatically validates many vulnerabilities by safely confirming exploitability.
The result:
- Higher confidence in reported vulnerabilities
- Less time spent manually verifying findings
- Faster remediation cycles for development teams
- Clearer evidence for compliance reporting
For AppSec teams under pressure to meet compliance timelines, this reduces friction across the entire vulnerability management process.
Deploy in line with healthcare security requirements
Healthcare organizations often have strict requirements around data handling, network access, and infrastructure control.
Invicti supports flexible deployment options to align with these constraints, including:
- On-premises deployment for sensitive environments
- Cloud-based scanning for scalability and ease of use
- Hybrid configurations for complex healthcare ecosystems
This allows organizations to implement vulnerability scanning without compromising internal security policies or architectural constraints.
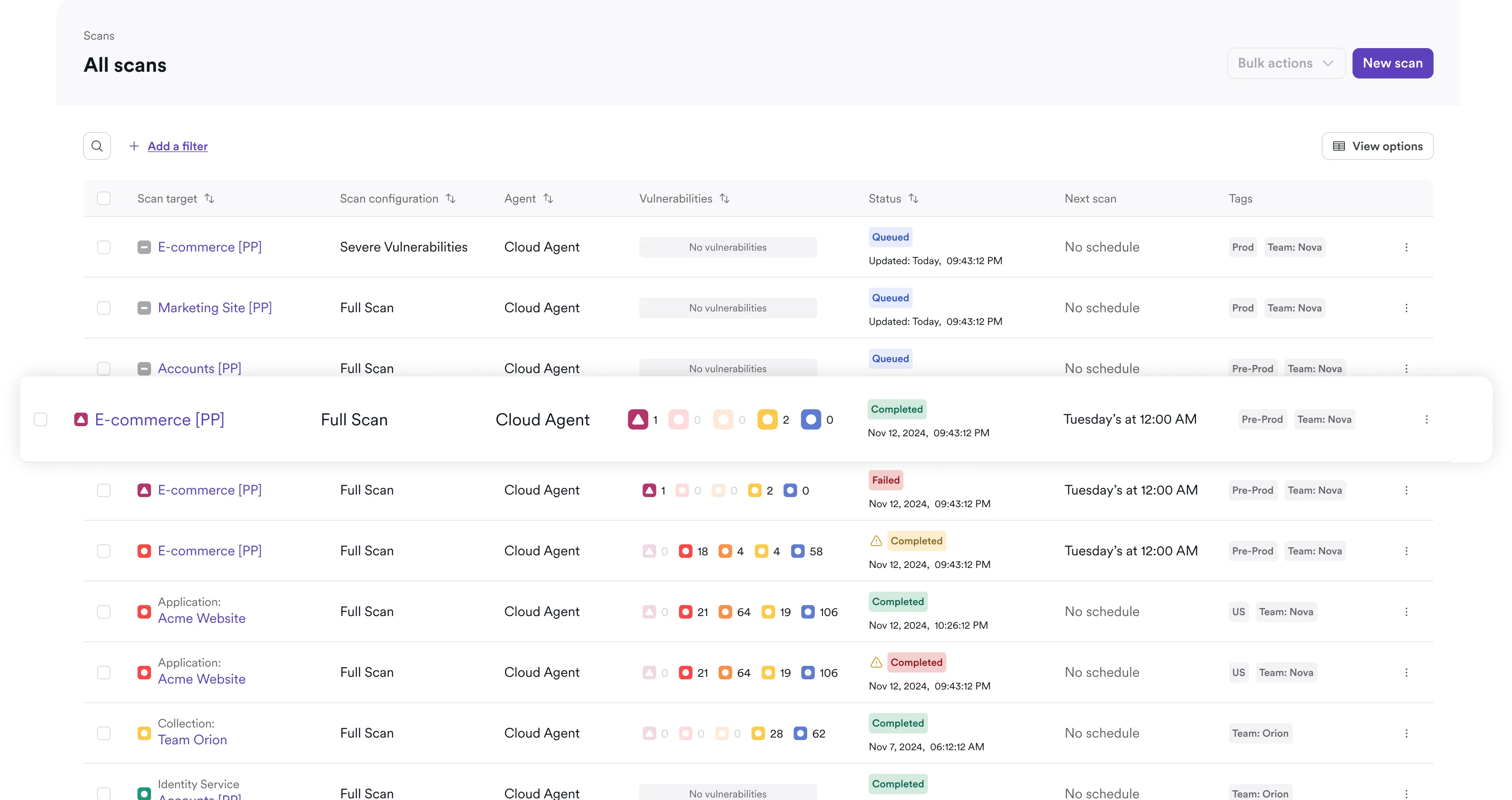
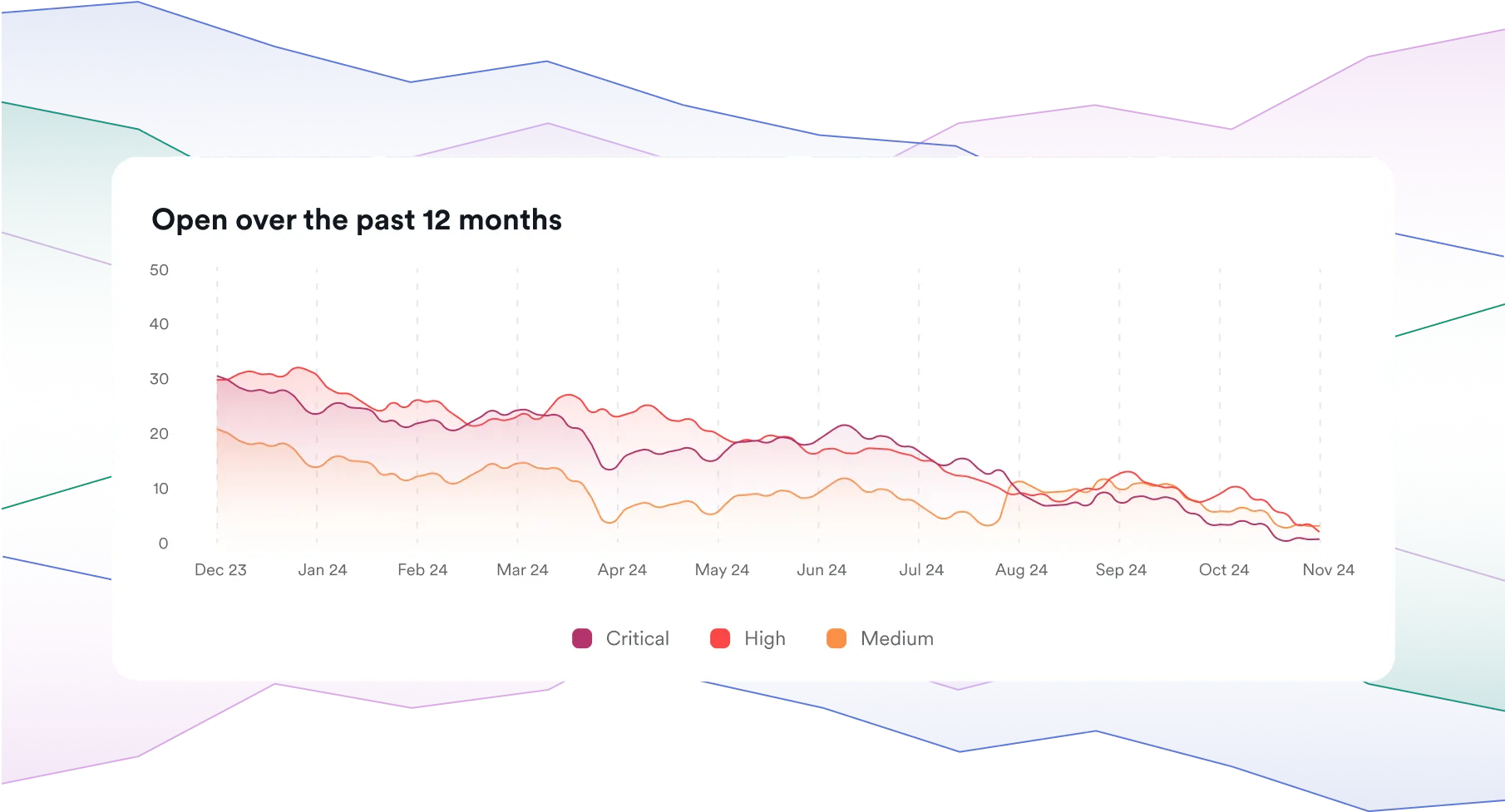
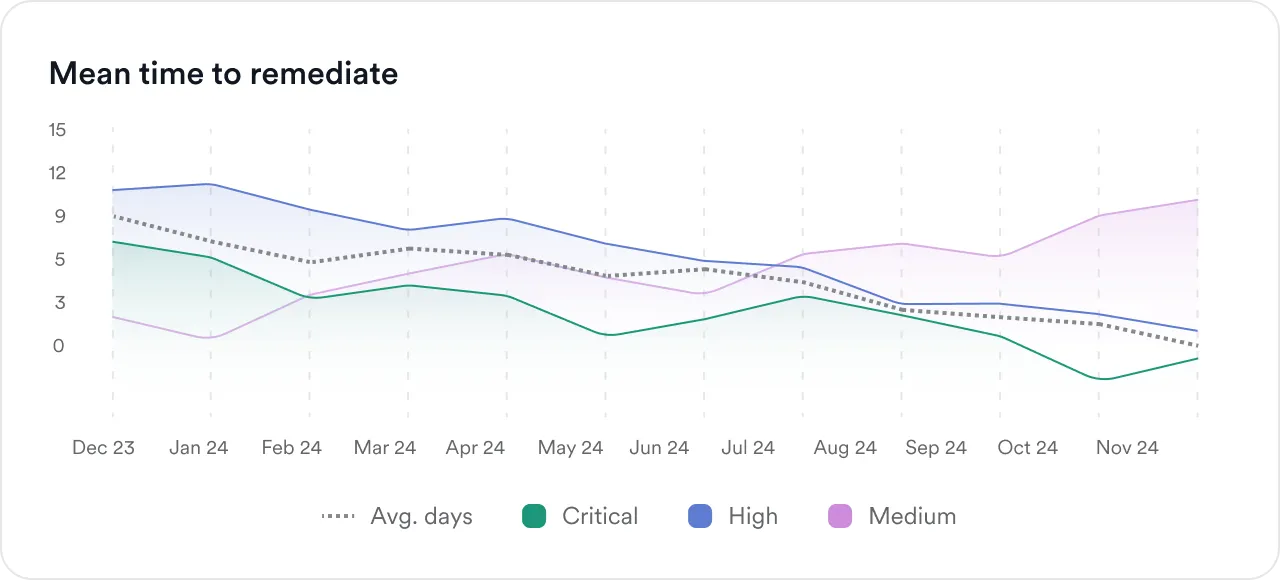
Built for continuous risk analysis, not only periodic scanning
HIPAA compliance is grounded in ongoing risk analysis, not point-in-time assessments. As healthcare applications evolve, new vulnerabilities emerge continuously.
Invicti supports this model with:
- Automated, repeatable scanning across applications and APIs
- Centralized visibility into vulnerability status and trends
- Integration with development workflows for continuous remediation
- Risk-based prioritization to focus on what matters most
This enables teams to move from reactive compliance to proactive risk management. Invicti also enables healthcare organizations to standardize vulnerability testing across large and rapidly changing application and API environments without adding manual review overhead.
Strengthen HIPAA compliance with real application security
Meeting HIPAA requirements for vulnerability management is no longer about proving that scans were run. It is about demonstrating that risks to ePHI are identified, validated, and addressed in a consistent and auditable way.
Invicti provides a comprehensive DAST-first application security platform designed to help healthcare organizations:
- Identify real, exploitable vulnerabilities in applications and APIs
- Align security testing with HIPAA Security Rule safeguards
- Generate audit-ready reports for compliance teams
- Reduce noise and accelerate remediation
For covered entities and business associates, this means greater confidence in both security posture and compliance readiness.
To see how this works in practice, request a demo to explore how Invicti supports HIPAA-aligned vulnerability scanning, reporting, and continuous risk analysis across your application environment.
Validate real risk across the applications and APIs that handle ePHI