PHP vulnerability scanner
DAST-first security testing for PHP applications and APIs on the Invicti Platform – find and validate real vulnerabilities in running applications, cut through false positives, and give teams the clarity they need to prioritize and fix security issues faster.

3600+ Top Organizations Trust Invicti
























PHP vulnerability scanner: Scan with confidence
PHP remains a widely used programming language for business-critical websites, customer portals, e-commerce platforms, and content management systems. That also makes PHP applications a common target for attackers looking for exploitable security vulnerabilities in login flows, input handling, session management, APIs, and widely-used third-party components.
Invicti helps organizations secure PHP applications by testing how they behave in the real world. As a DAST-first application security platform, Invicti scans running web apps and APIs to identify application vulnerabilities that attackers can actually reach and exploit. Because testing happens against the live application in its runtime environment, Invicti works across PHP environments without requiring access to source code or a repository.
Whether you’re running WordPress, Laravel, Symfony, CodeIgniter, Drupal, Joomla, custom PHP applications, or any mix of legacy and modern frameworks, Invicti can help uncover security issues such as:
- SQL injection
- Cross-site scripting (XSS)
- Remote code execution (RCE)
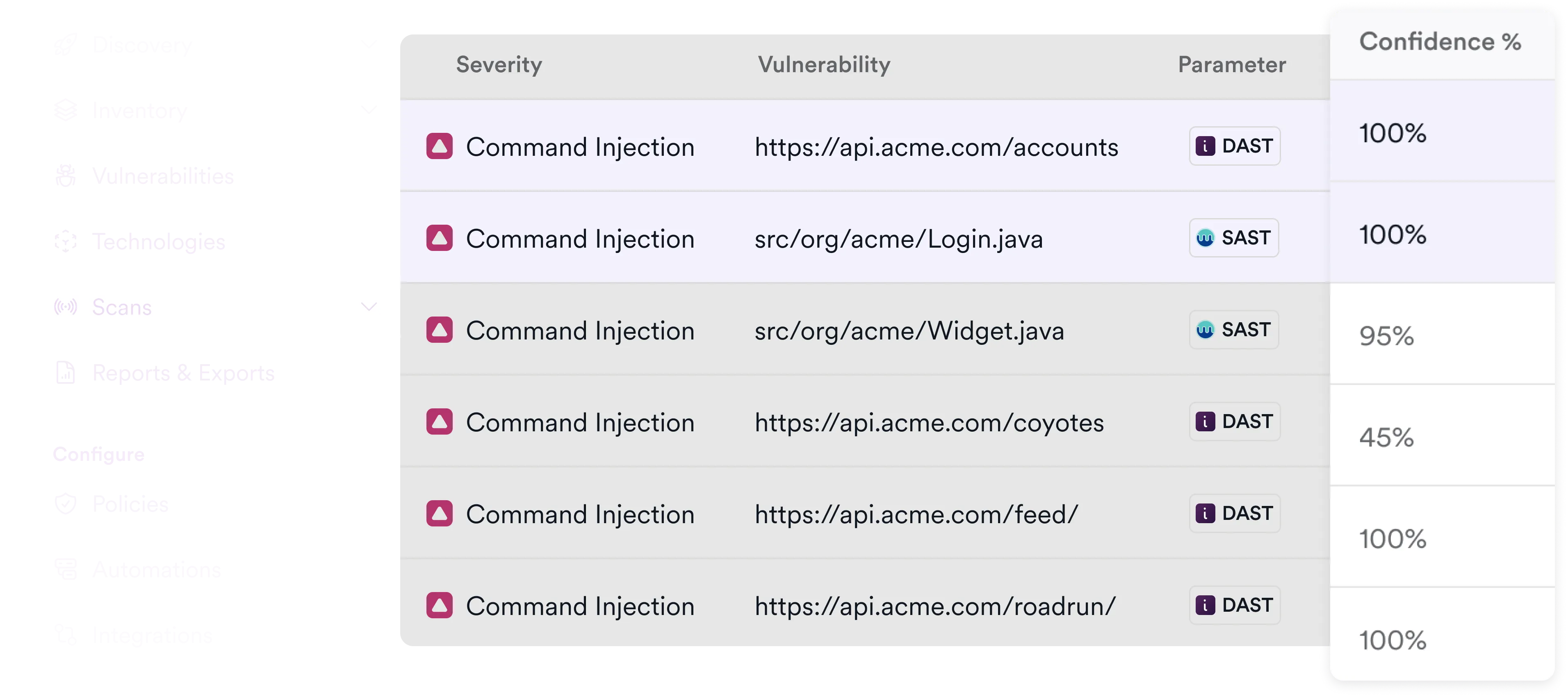
- Command injection
- Authentication and authorization weaknesses
- Local and remote file inclusion
- Cross-site request forgery (CSRF)
- Security misconfigurations and exposed attack surface
- Outdated and vulnerable open-source components, plugins, and dependencies with known vulnerabilities
Unlike basic PHP scanning tools that may create more noise than value while also missing many issues, Invicti uses a mature scan engine for dynamic application security testing (DAST) with proof-based scanning to find and automatically confirm many high-impact vulnerabilities. That helps teams reduce false positives, improve vulnerability detection, and move faster on remediation.
Automated PHP vulnerability scanner
Modern PHP environments change constantly, with new code, dependencies, and APIs introduced throughout the development lifecycle. Manual penetration testing alone cannot keep up with this pace or provide consistent coverage across all applications and endpoints.
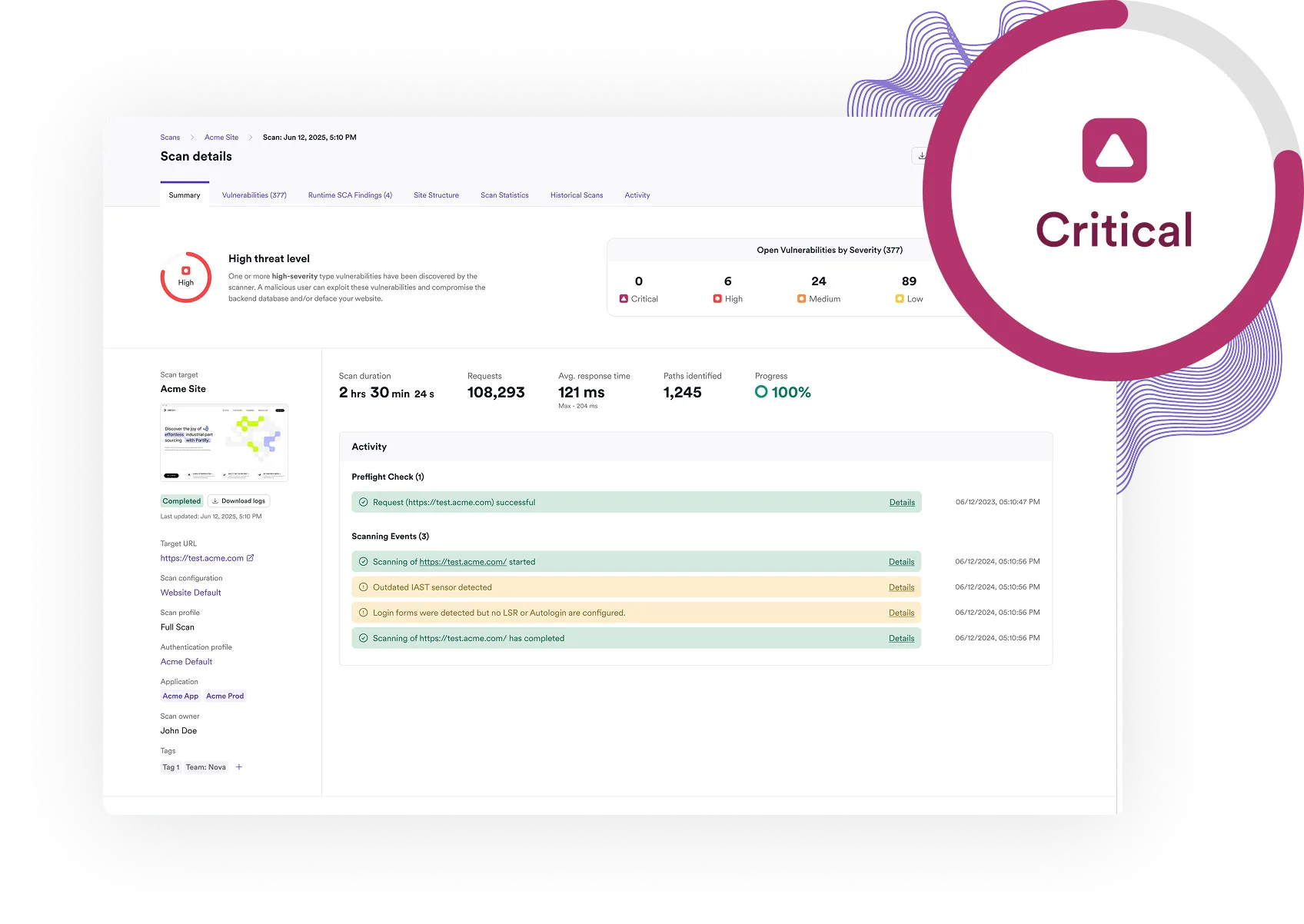
Invicti provides an automated PHP vulnerability scanner that continuously tests running applications and APIs for security issues. By using dynamic application security testing, it evaluates real application behavior and identifies security flaws that are reachable in production-like conditions – helping teams focus on issues that represent actual risk rather than theoretical findings.
Automation also allows organizations to scale PHP security testing across large portfolios without adding overhead. Scans can be scheduled or triggered through CI/CD pipelines, ensuring that new releases, updates, and configuration changes are automatically assessed. Combined with proof-based scanning, this approach helps validate many vulnerabilities during the scan itself, reducing the need for manual verification and enabling faster, more confident remediation.
For teams managing multiple PHP language applications, frameworks, and APIs, automated scanning provides consistent visibility into security posture while supporting development speed and operational efficiency.
Go beyond basic PHP scanning with a full AppSec platform
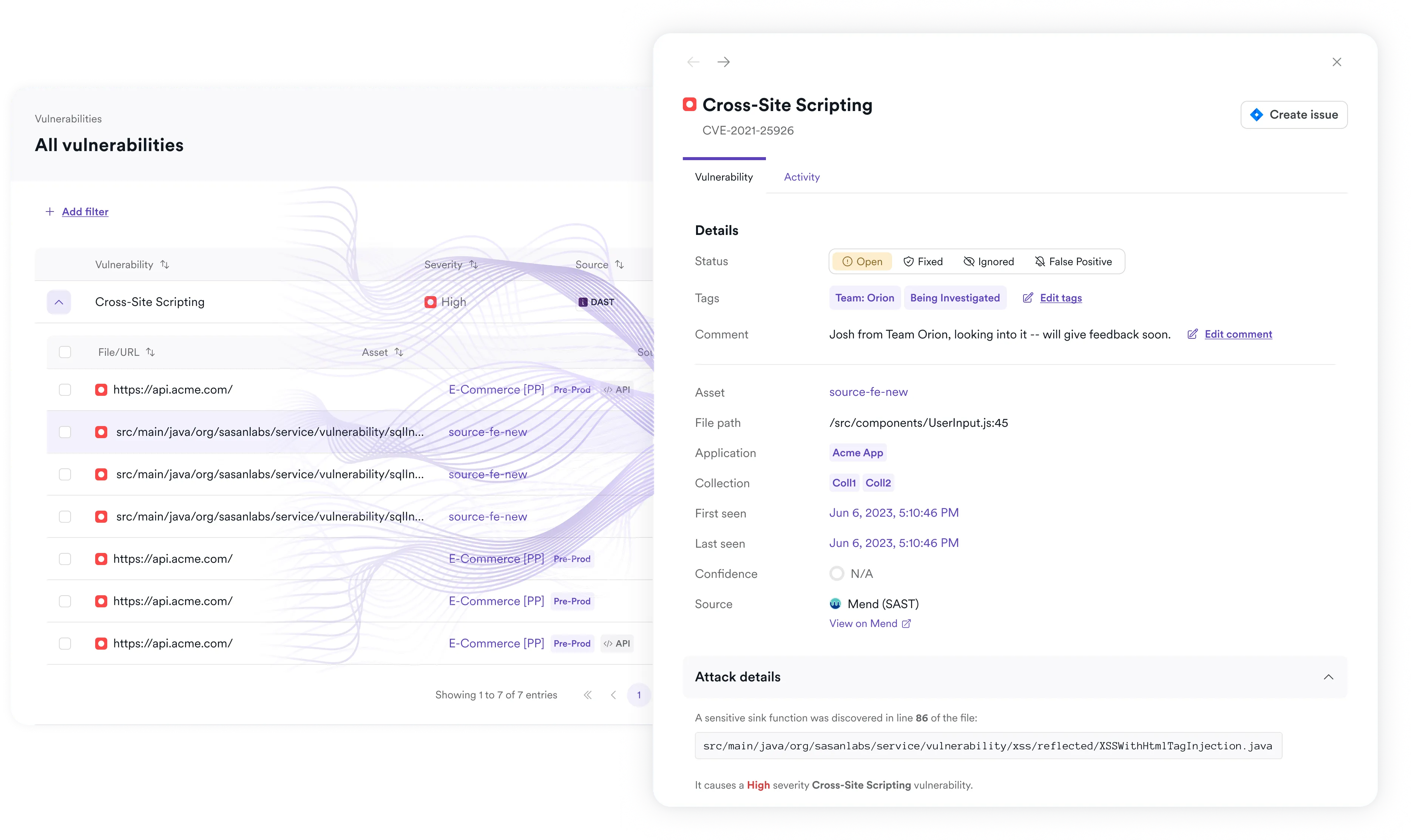
Finding PHP vulnerabilities is only part of the job. Security teams also need to understand which issues are real, where they exist across the environment, and how to prioritize fixes without slowing development.
Invicti is built for that broader challenge. Its DAST-first approach focuses on real, exploitable risk in running applications to help teams cut through noise and spend less time chasing findings that do not represent meaningful exposure. Detailed evidence and clear remediation guidance make results easier for developers and security teams to validate and act on.
Where teams also want code-level insights, the Invicti Platform includes static application security testing to complement runtime testing. This gives organizations an additional layer of security analysis for PHP code in the repository and helps identify issues in PHP files and scripts earlier in development while keeping runtime validation as the main prioritization lever.
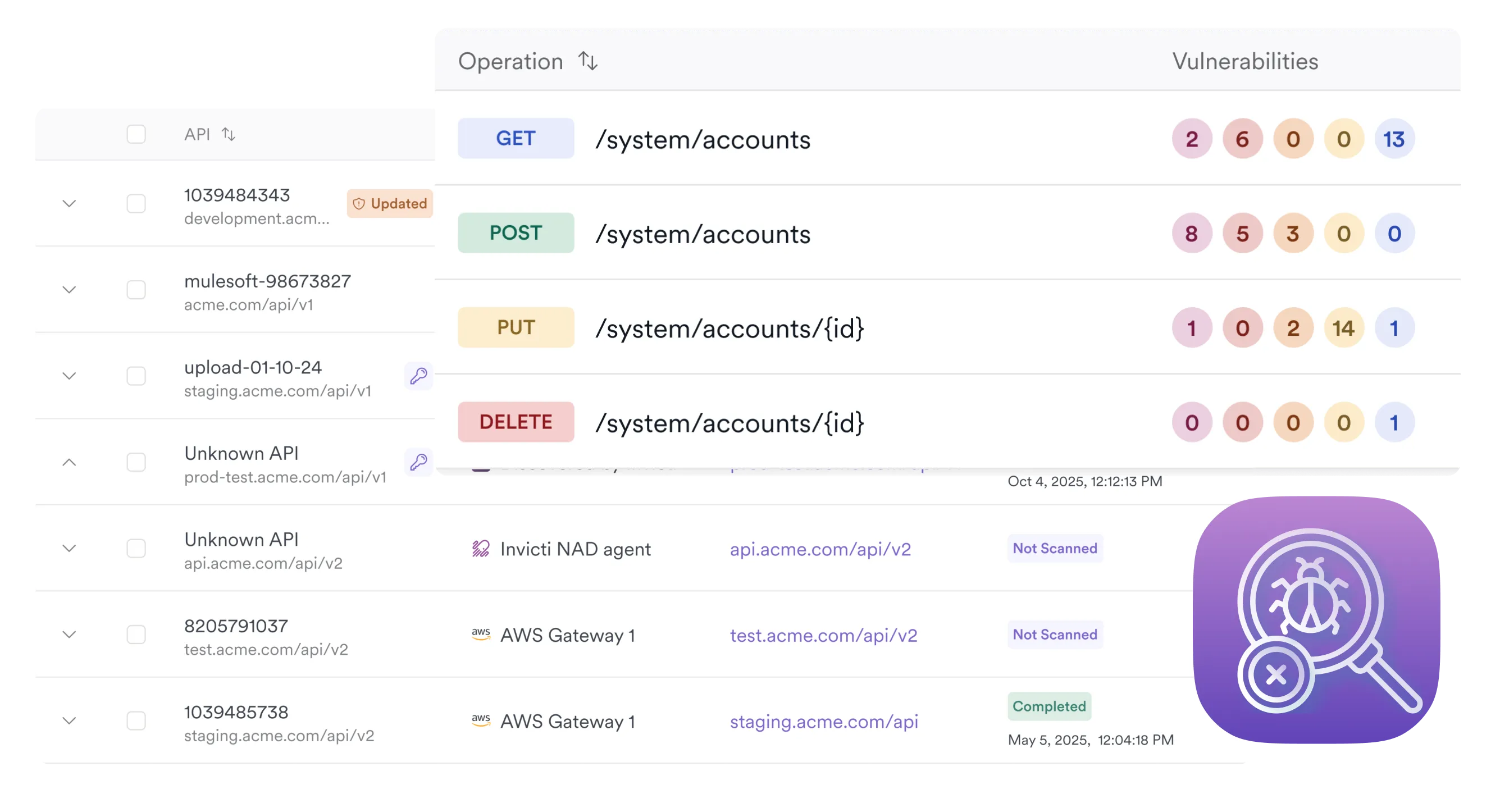
For organizations working with large or growing application portfolios, Invicti also provides a unified way to see and manage security findings across web applications, APIs, and code. This helps teams centralize vulnerability management, improve prioritization, streamline workflows, and bring more consistency to application security operations.
Seamless integration with development workflows
Security testing should support delivery speed, not get in the way of it. Invicti integrates with CI/CD pipelines, issue trackers, and development workflows so teams can bring PHP security testing into day-to-day engineering processes.
With Invicti, teams can:
- Automate vulnerability scanning throughout the release cycle
- Identify exploitable vulnerabilities earlier in the software development lifecycle
- Add SAST to development workflows for broader coverage
- Send validated findings into developer workflows for faster remediation
- Reduce friction between development and security teams
- Support enterprise requirements with features such as single sign-on (SSO) and role-based access control (RBAC)
This allows organizations to scale PHP security testing without adding unnecessary manual effort or slowing down releases. It also helps teams connect runtime testing with static application security testing in environments that use GitHub, GitLab, Docker, and other modern delivery workflows.

Why choose Invicti as your PHP vulnerability scanner?
Invicti helps organizations secure PHP applications with:
- DAST-first security testing for running PHP applications and APIs
- Proof-based scanning to validate many exploitable vulnerabilities automatically
- SAST on the Invicti Platform to add code-level insights alongside runtime testing
- Technology-agnostic coverage across PHP as well as non-PHP frameworks, CMS platforms, and modern web applications
- Unified visibility across application and API security testing workflows
- Integrations that support DevSecOps processes and remediation at scale
- Centralized prioritization, governance, and compliance reporting for growing AppSec programs
With Invicti, teams can identify, validate, and remediate vulnerabilities more efficiently while improving visibility across their PHP application environment.
Invicti helps teams go beyond surface-level scanning by focusing on security vulnerabilities in running PHP applications that attackers can actually reach. With proof-based scanning, Invicti can automatically validate many high-impact issues, reducing false positives and making findings more actionable for both security teams and developers. Teams that need deeper code-level visibility can also use SAST on the Invicti Platform to complement runtime-based vulnerability scanning.
Yes. Invicti can scan PHP-based CMS platforms such as WordPress, Drupal, and Joomla, as well as custom-built PHP applications and popular frameworks like Laravel and Symfony. This helps organizations assess risk across both standard deployments and highly customized PHP environments, including issues introduced through plugins and other third-party components.
Invicti provides a full set of application security testing tools and uses its DAST to assess running PHP applications from the outside in just as an attacker would. It can crawl and test application functionality, evaluate authenticated areas, and identify vulnerabilities such as SQL injection, XSS, authentication flaws, and other exploitable security issues from the OWASP Top 10 and beyond. For many findings, proof-based scanning provides additional validation to help teams focus on real risk.
No. Invicti’s core PHP security testing does not require access to source code because it uses dynamic testing against the running application. That makes it well suited to environments where teams need to assess security across custom applications, packaged platforms, or third-party-managed PHP deployments. For teams that also need static code analysis, Invicti Platform can perform static application security testing against code in a connected repository.
Yes, Invicti integrates seamlessly with CI/CD pipelines, issue trackers, and development workflows, enabling automated security testing and rapid remediation within DevSecOps environments.
Yes. Many PHP applications rely on APIs, JavaScript-heavy front ends, and server-side functionality running on a web server, and those assets are part of the real application attack surface. Invicti helps organizations test APIs and web applications together so they can find vulnerabilities across the full user-facing environment instead of treating each layer separately.

