How to choose the right AppSec solution for MSPs
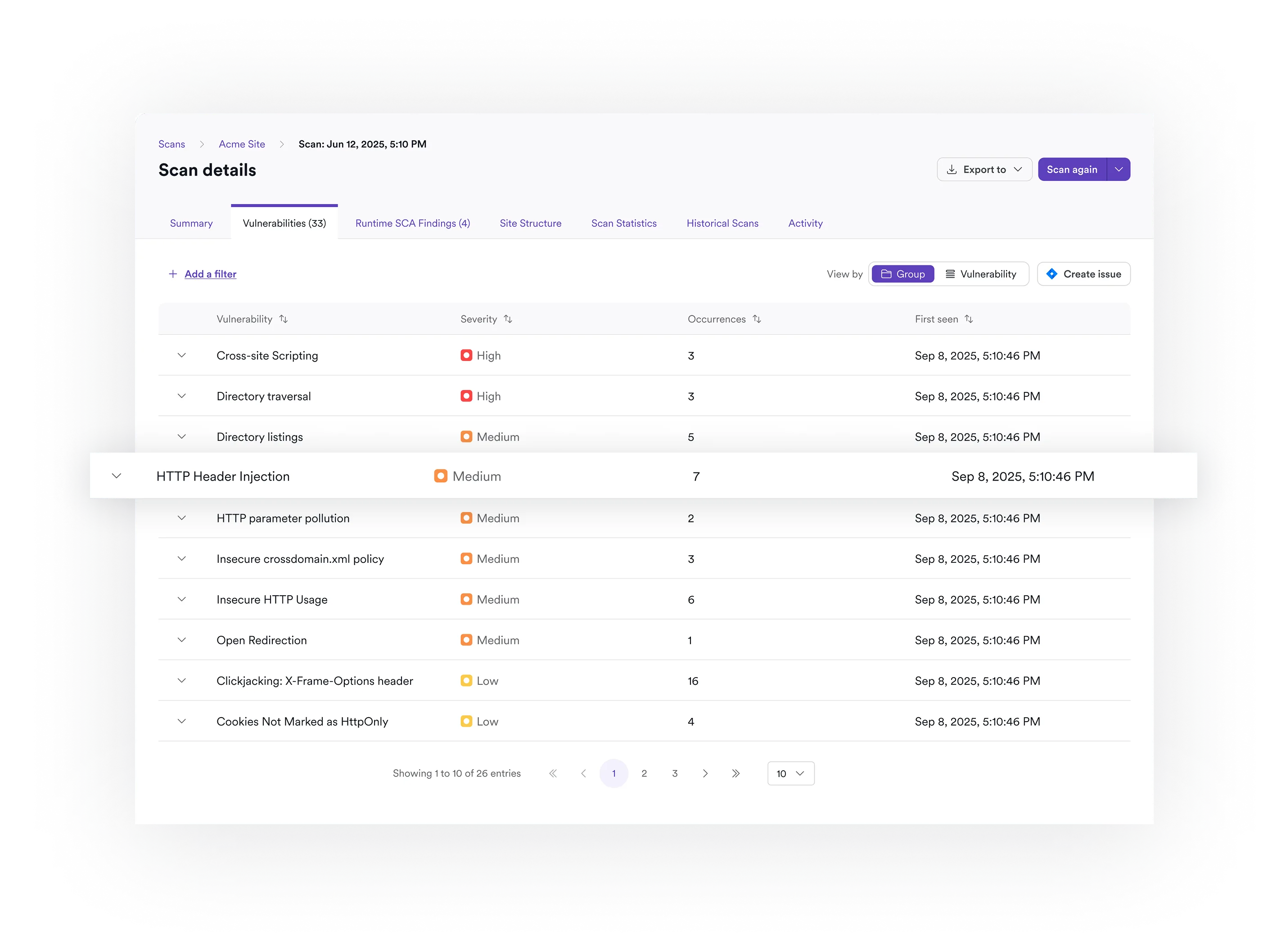
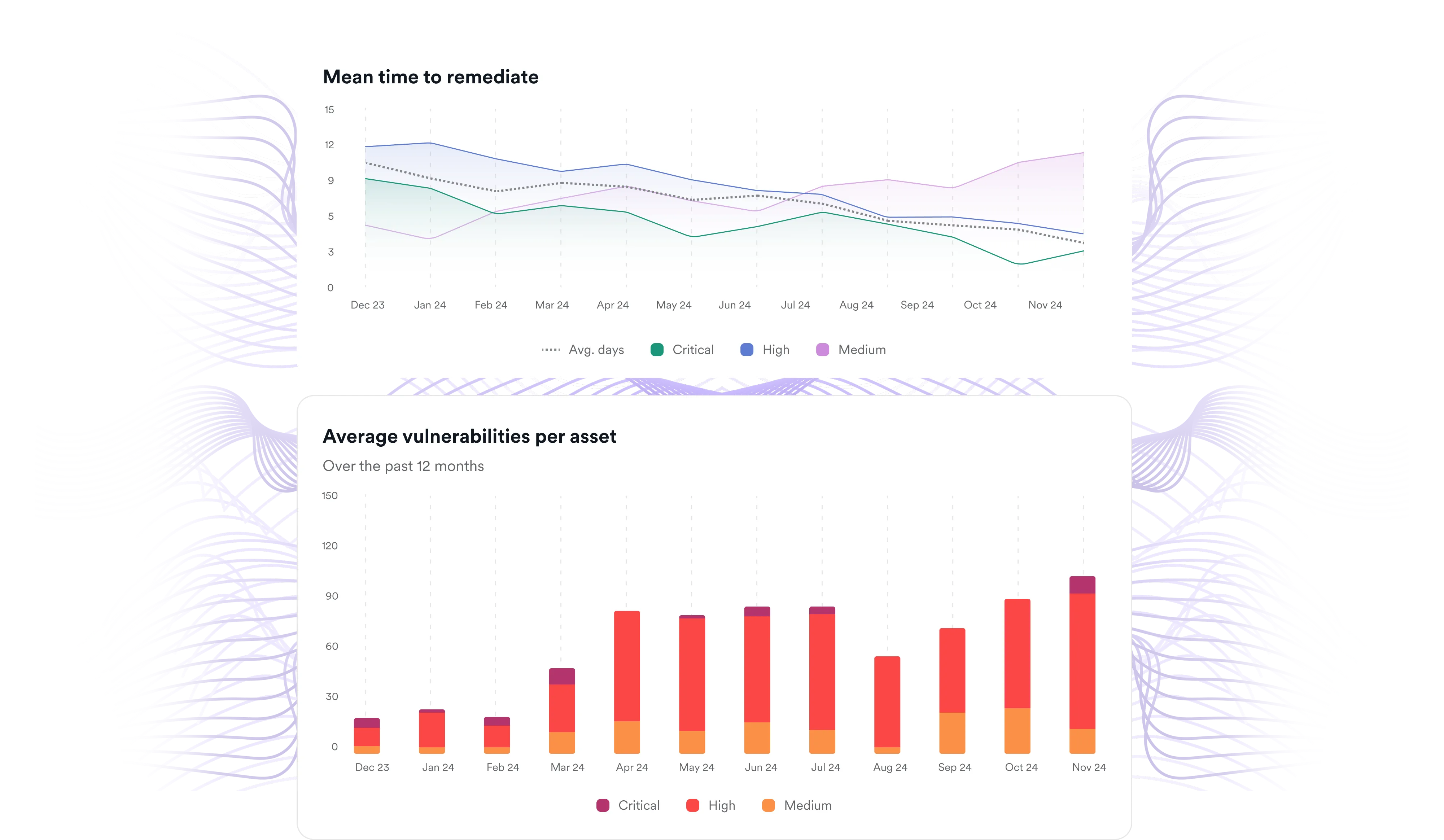
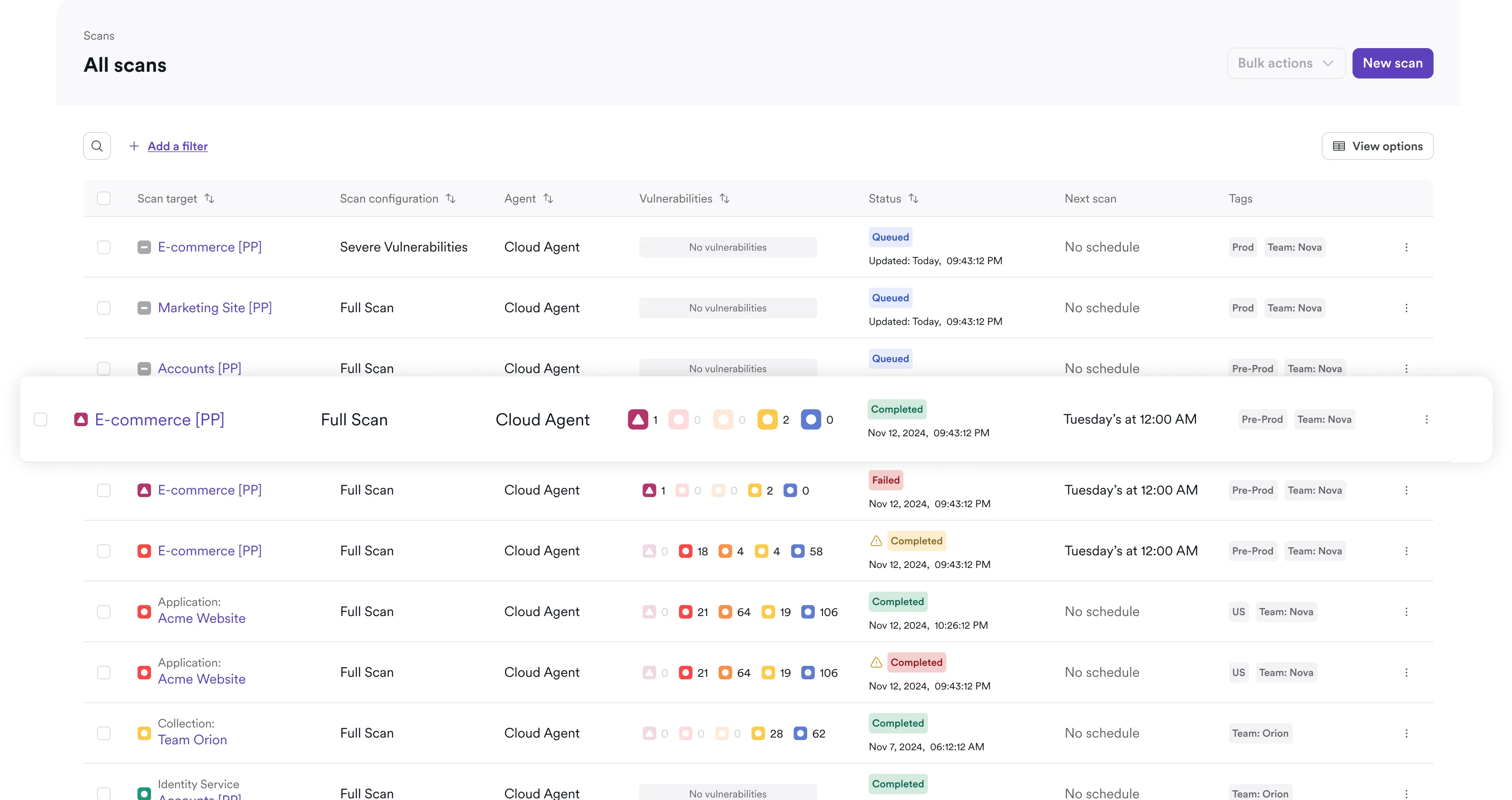
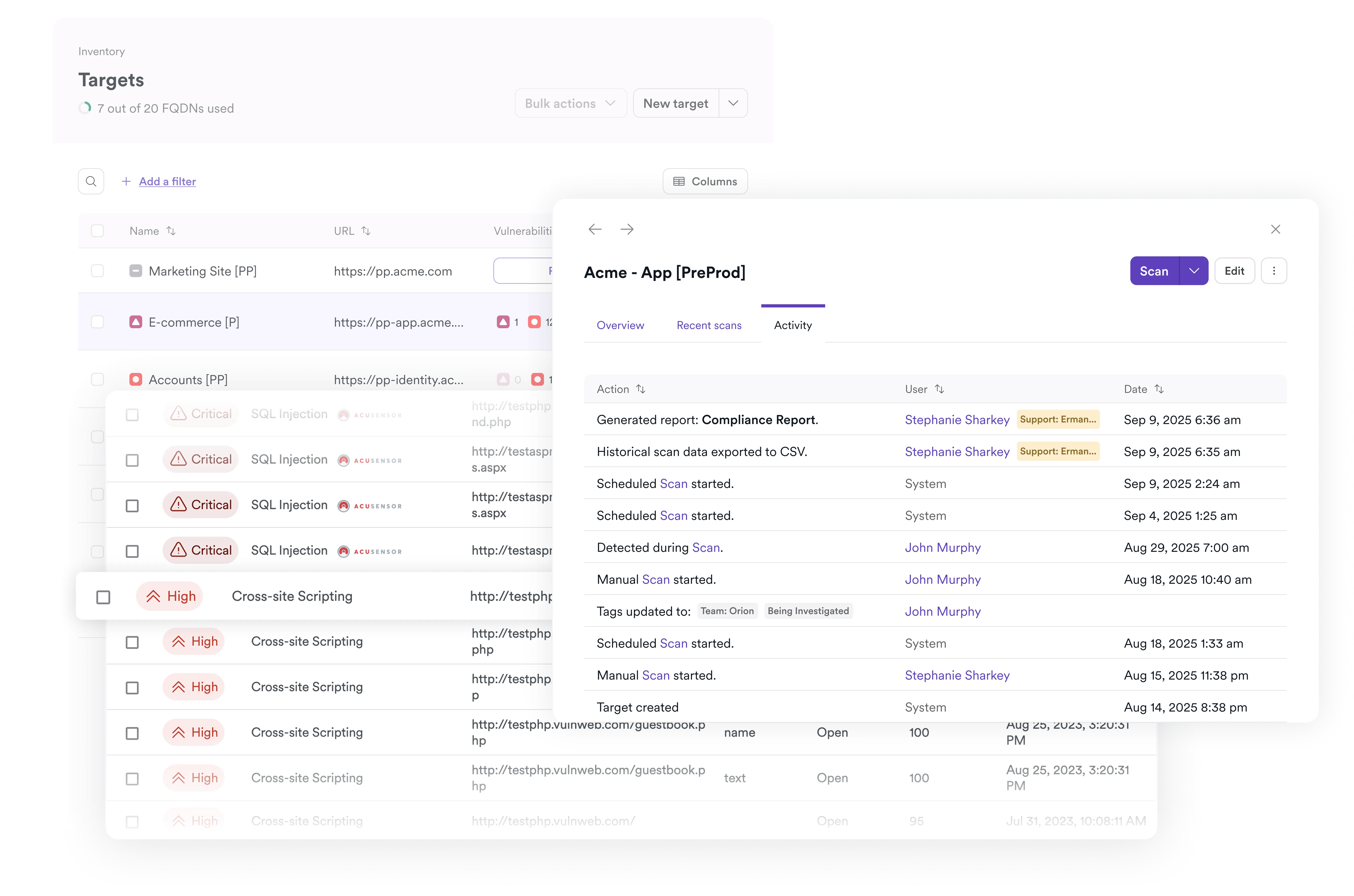
To scale effectively, providers need a platform that delivers accurate results, supports multi-tenant environments, and automates security workflows. The right solution enables MSPs to deliver vulnerability assessment and application security services efficiently while protecting their margins.
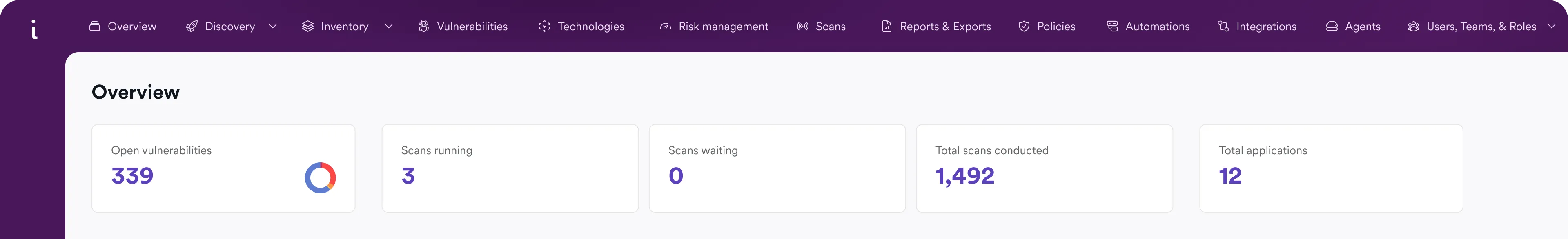
The Invicti Application Security Platform addresses this need. Built around industry-leading DAST and expanded with additional AST tools, API security, ASPM, and automation capabilities, Invicti enables providers to deliver scalable AppSec services across their entire client ecosystem.