Invicti DAST-to-SAST correlation: Fix verified runtime risks at pipeline speed
Modern DevOps teams constantly face the pressure of balancing delivery speed with security. Traditional DAST finds real, exploitable risks but lacks clear code location, leading to manual tracing that can take hours or weeks. Invicti’s new DAST-to-SAST correlation solves this by linking proof-based runtime findings with SAST results to pinpoint the exact line of source code and identify the developer who checked it in. By cutting through the noise and eliminating false positives, this unified approach accelerates remediation cycles from weeks to just hours, better aligning AppSec and DevOps for faster, more confident releases.

DevOps’ uneasy relationship with DAST
DAST findings demand DevOps leaders’ immediate attention, as runtime results highlight exploitable risks in live production environments. However, unlike SAST, traditional DAST findings lack clear guidance on the location of the problematic code or on the developer who checked it in.
Once alerted, development teams scramble, wading through code repositories to find the root cause, a labor-intensive and time-crushing endeavor. Root cause analysis takes hours, days, or weeks, particularly when investigating complex, distributed systems. And what modern application isn’t a web of loosely coupled API microservices?
Faced with confirmed security risks at the end of a delivery pipeline, DevOps leaders have to make a difficult decision quickly to meet committed deadlines:
- Break the build, or
- Accept the risk – find a compensating control or fix later
It’s not an easy decision. Missing delivery commitments means reporting bad news to executives, while releasing vulnerable applications increases risk. This is especially critical given the 60-day industry average to fix production security issues. Still, accepting risk rather than halting innovation is the most common outcome, as business priorities often eclipse security in many organizations.
As organizations advance their DevSecOps maturity, the traditional boundaries between static and dynamic testing must dissolve. What's needed is a unified approach that shifts runtime-validated vulnerability detection left – where remediation is faster, cheaper, and far less disruptive – harnessing the broad coverage of static analysis, grounded in the proof-based precision of DAST, at the velocity modern delivery pipelines demand.
What is DAST-to-SAST correlation?
Invicti’s new DAST-to-SAST correlation addresses the ongoing challenges that Security and DevOps leaders face by binding proof-based DAST findings with more noisy SAST results. This correlation method not only provides evidence of exploitability and reachability but also pinpoints the offending code’s location and the originating developer, all within a single alert. Combined with AI-guided fixes integrated in automated Jira ticket creation, this capability can reduce repair cycles from days to just hours.

As a result, security and DevOps teams can cut through the noise, make release decisions faster, and remediate real risks with clear, actionable insights. Ultimately, this reduces effort, builds developer trust, and improves both security and delivery outcomes.
Benefits
- True positive confidence increases (noise reduction)
- Fix ownership becomes clear
- Risk prioritization strengthens
- Duplicate findings are deduplicated
- KPI and compliance quality improves
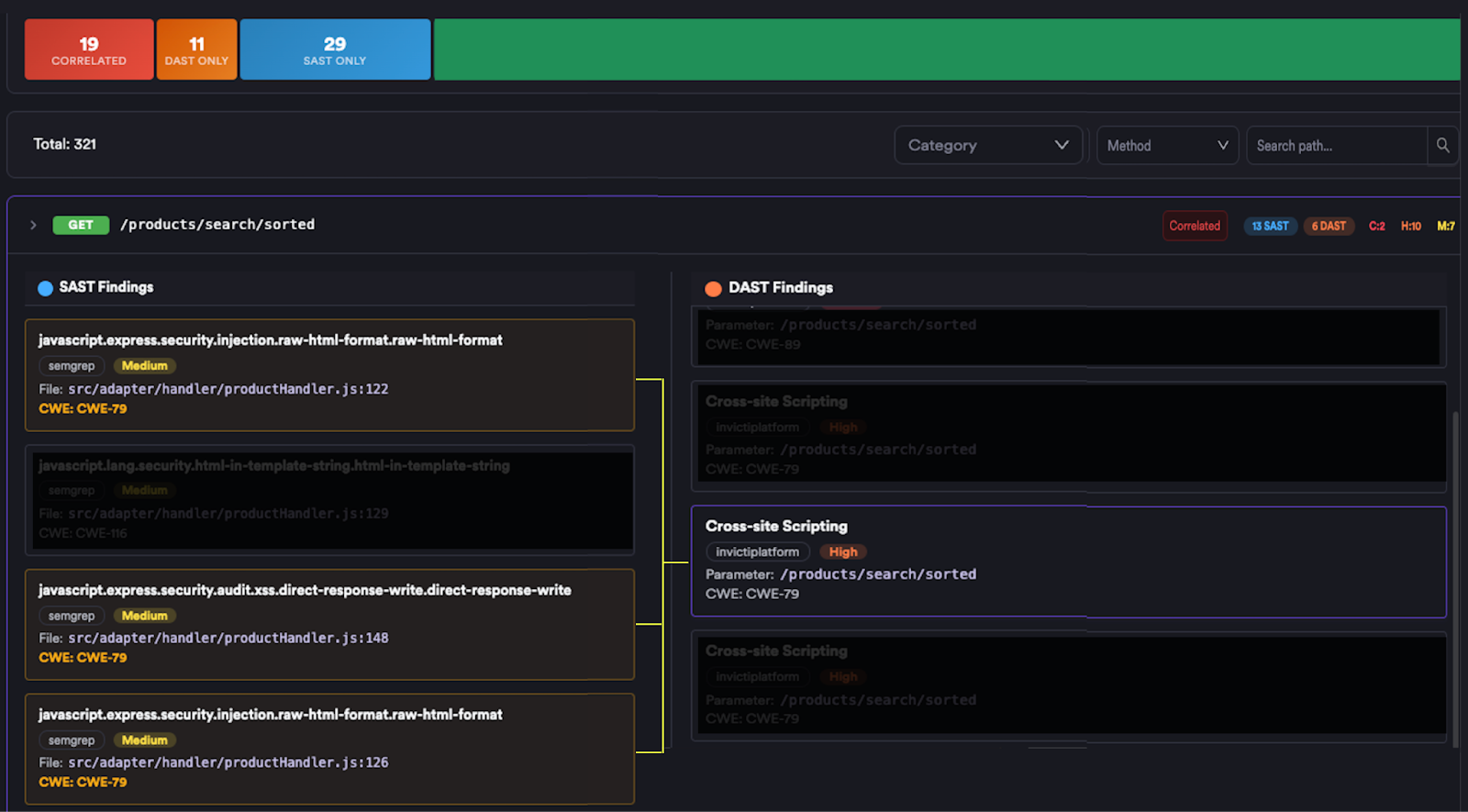
How it works
To correlate DAST and SAST results, Invicti’s comprehensive application security platform parses connected code repositories to extract every API endpoint in the project, then builds a dependency call graph – a map of how each endpoint chains through the codebase, up to 10 levels deep. SAST and DAST findings are mapped onto the graph to produce precise many-to-many correlations. The correlations reveal not just that an endpoint is vulnerable, but which SAST findings map to DAST results and the exact code paths involved.
Shift-left API security testing
As discussed, APIs naturally enable DAST scans earlier in the development cycle, at the microservice, module, or subsystem level. That makes DAST-to-SAST correlation especially powerful for triaging voluminous, noisy static findings and accelerating remediation early in the delivery pipeline.

To streamline security testing workflows, Invicti offers a container-based CLI that integrates seamlessly into developer environments and CI/CD pipelines. It supports scanning across any stage in the SDLC, whether isolated services locally, pre-production, or live production systems. While enabling teams to run security scans even in fully isolated environments with no internet exposure, without requiring on-prem installations.
Does it work for every DAST finding?
For DAST-to-SAST correlation to succeed, Invicti’s vulnerability inventory must contain both a DAST finding and at least one correlatable SAST finding. As a result, this approach is limited to vulnerabilities that both tools can detect.
The Venn diagram below illustrates which vulnerability types static and dynamic scanners can each detect, where they overlap, and which findings are candidates for correlation.
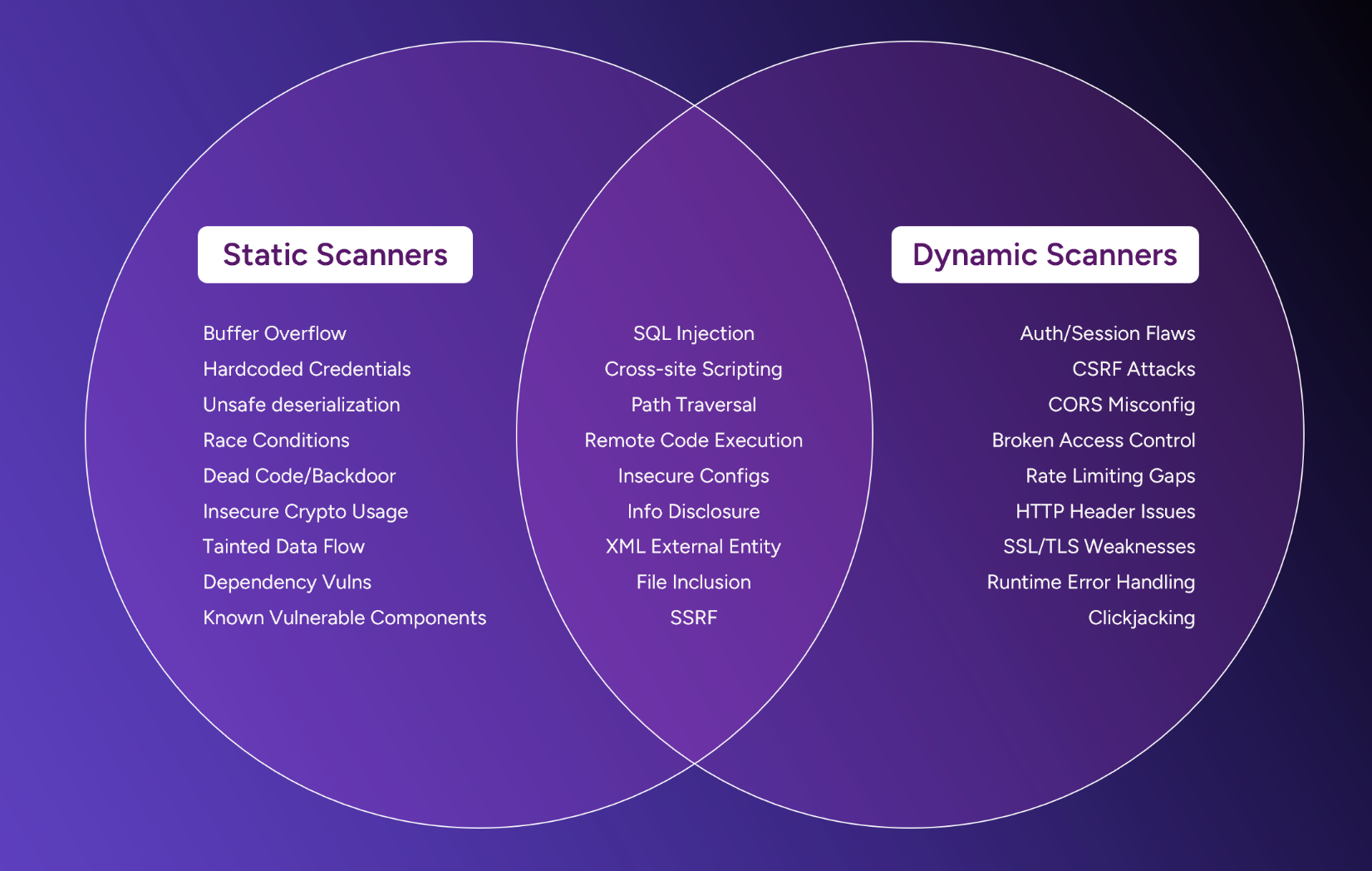
The first insight from this diagram is that SAST and SCA tools, along with DAST, are essential for comprehensive vulnerability coverage:
- Skipping DAST at any phase of the SDLC lifecycle leaves you exposed to hidden risks.
- The intersecting vulnerabilities, those detectable by both static and dynamic scanning, are where DAST-to-SAST correlation can most effectively drive prioritization and speed up remediation.
Conclusion
Modern DevOps teams constantly balance speed and security, as traditional DAST approaches introduce verified risks late in the CI/CD cycle. This often leads to slow remediation and prolonged exposure to risk.
Invicti’s DAST-to-SAST correlation resolves this challenge by linking proof-based runtime findings with precise source code context. By combining exploitability validation with developer-level visibility, teams can quickly identify, prioritize, and fix real vulnerabilities without unnecessary investigation.
This approach dramatically reduces noise, accelerates remediation from weeks to hours, and better aligns security with DevOps workflows. Ultimately, organizations can deliver secure applications faster and make more confident, risk-informed decisions.
Experience the future of AppSec with our webinar “DAST and SAST, Finally Working Together For Fast Fixes.” Learn from Invicti experts how to transform runtime findings into clear, code-level actions, and request a demo when you’re ready to find and fix code issues faster.
Frequently asked questions
Experience the future of AppSec




