The Pitfalls of SAST vs DAST Thinking
The web application security industry loves its acronyms, with
SAST, DAST, IAST, and many other terms making up a real alphabet soup. This encourages “either-or” decision-making: we pick one *AST, implement it, and then we’re secure. Unfortunately, in the
real world, things are not that simple and organizations often struggle to get value from their investment in web application security, especially when it comes to SAST.
The idea of starting with
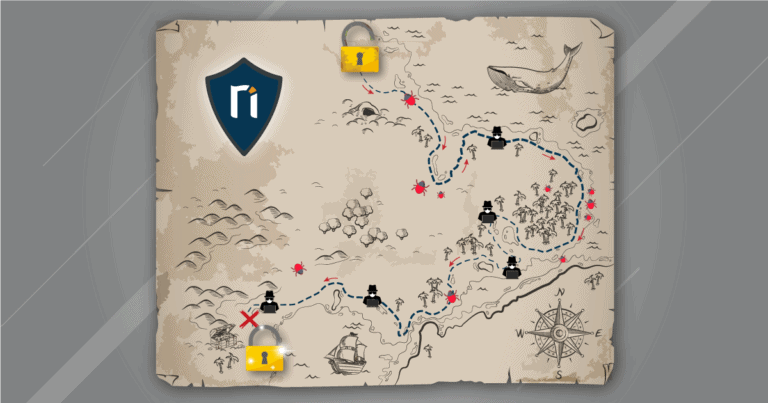
static application security testing (SAST) is reasonable enough: if you write secure code, you should end up with a secure application. In military terms, you are building up a secure, maybe even impregnable defensive position. But this is just one position on the huge and mobile battlefield of web application security. What about all the others? Do you know where all your resources and valuable assets are? Can you anticipate where the next attack will come?
Without a high-level strategic view of the entire environment, organizations run the risk of blindly deploying great tactical security measures in some places while leaving gaping holes in their defenses elsewhere. While they are building up their cybersecurity bunkers, another location could be under attack or already breached without anyone noticing. This is where
dynamic application security testing (DAST) comes in – your aerial reconnaissance for web security.
Know the Enemy and Know Yourself
In public web environments, attackers can strike anywhere and at any time, so time is not a luxury that modern organizations have. Every day spent without a solid understanding of the current security posture and priorities is another day at risk of a breach. Investments in web security should quickly and visibly reduce this risk – and yet nobody is surprised to hear about a SAST deployment that will take several months to complete.
Building an in-depth defense from the first line of code is a noble goal, but the first step must be getting full visibility of the entire environment to see where the most dangerous weaknesses are. Modern web application environments can be extremely complex patchworks of new and legacy code spread across multiple locations. The only realistic way to get a high-level view of your assets and security is to use a high-quality dynamic application security testing solution with
advanced asset discovery, crawling, and
vulnerability scanning capabilities. Armed with the knowledge of all your assets and identified vulnerabilities, you can then plan your actions based on solid facts, not guesswork.
In the web security world, knowing your enemy is next to impossible – but with a sufficiently advanced DAST solution, you can keep track of the enemy’s methods. Taking Invicti as an example, dedicated security researchers work every day to discover and implement new attack vectors and techniques, allowing the product to simulate the efforts of real-life attackers and find vulnerabilities before they can be exploited. This adds another dimension to your security intelligence by providing reliable data about your web application security priorities.
DAST Provides a Map for Your Security Journey
Simply put, a
modern DAST solution is the only way to get a complete picture of your web security posture and take action from day one. When you know what assets and vulnerabilities you have, you can make informed decisions on your web security journey. This could include identifying priority areas for vulnerability remediation, SAST deployment, web application firewall (WAF) deployment, and other security initiatives.
Crucially, any organization can deploy DAST right now and gain this clarity in a matter of days. With an advanced solution like Invicti, getting started is very easy. As you go deeper, you can integrate dynamic testing into your development pipelines regardless of language, framework, or architecture – another major boost for efficiency and security. You can then have a real-time picture of your web application security status across all environments without having to spend weeks on configuring individual testing deployments.
A high-level view of your entire web environment and vulnerability status is like your battle map. Without it, you are acting in the dark and risk wasting precious time and resources on initiatives that could bring no immediate security benefits. Don’t let the enemy catch you by surprise – let Invicti be your eyes on the battlefield.