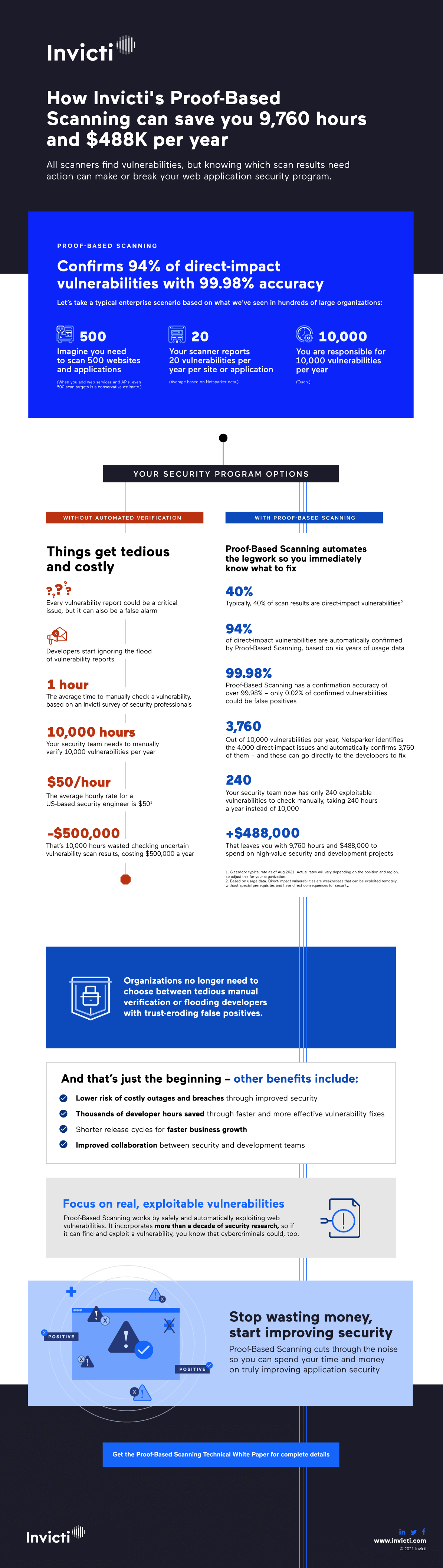
Accurate vulnerability scanning saves money – and we can prove it
99.98% – that’s the data-based accuracy of automatic vulnerability confirmation in Invicti. With such reliable results provided for the vast majority of serious issues, you can truly automate your application security program. Learn how we arrived at this number and see our infographic to discover how accurate results can translate into major savings.
Your Information will be kept private.
Begin your DAST-first AppSec journey today.
Request a demo
Real-life usage data proves the accuracy of Proof-Based Scanning
Based on our own internal testing and consistently positive customer feedback, we’ve always known that Proof-Based Scanning has a very high accuracy – but exactly how high? To answer this, the Invicti data team crunched the numbers from 6 years of anonymized usage data for the Invicti Enterprise on-demand web vulnerability scanner, covering over 540,000 unique vulnerabilities in customer applications. The two main goals were to find out how often Invicti provides automatic confirmation in real-life application environments and how accurate these confirmations really are.
The key to gauging confirmation accuracy was the False Positive flag that Invicti users can set in scan results to indicate that they believe the scanner made a mistake. Our security researchers sat down and manually checked all the reports flagged by users as false positives, eventually discovering that nearly all these results were actually real vulnerabilities. After fine-tuning to account for customer feedback, the Invicti scan engine now has a confirmation accuracy of over 99.98% – which means fewer than 2 false positives per 10,000 confirmed vulnerabilities.
But what actually gets confirmed? Automatically confirming every single vulnerability found by the scanner is not technically possible and, in any case, confirmation wouldn’t make a huge practical difference for low-severity issues. Instead, Proof-Based Scanning focuses on confirming vulnerabilities that have a direct impact on your security posture and could have serious consequences if exploited remotely by malicious actors. For these direct-impact vulnerabilities, Invicti provides accurate automatic confirmation in 94% of cases, allowing you to immediately address the issues that really matter and need urgent action.
Confidence in your scanner makes all the difference
The significance of this research goes far beyond impressive marketing numbers (though we are delighted to have them). First and foremost, the idea behind Proof-Based Scanning is to automatically and safely exploit application vulnerabilities to prove they are real and not false positives. Knowing that confirmations are 99.98% accurate enables your teams to fully trust confirmed scan results and make the right security decisions. Just as importantly for prioritizing work, confirmation is also an indicator of risk – after all, if an automated scanner can exploit a weakness, then so can real-life attackers.
Reliable vulnerability confirmation by the scanner with no human intervention enables true automation and integration at scale without risking false positives. Developers can now get actionable security tickets directly into their existing issue tracker and start fixing vulnerabilities without waiting for manual verification, triage, and assignment. In large application environments, this level of automation is the only practical way for security to keep up with the pace and scale of development. On an enterprise level, security automation can also make the difference between spending thousands of hours (and dollars) on low-value busywork and measurably improving security with each issue you resolve.
Economies of accurate automation
Compared to a traditional process that relies heavily on manual coordination by security engineers, integrating confirmed vulnerability reports into an automated remediation workflow is a whole different game. Instead of an endless backlog of vulnerability reports awaiting verification, you get actionable tickets that your developers can start fixing immediately. Each automatic report comes with all the necessary technical information and remediation guidance to minimize communication overhead and eliminate time-wasting due to false positives.
We’ve prepared an infographic to show the savings that accurate vulnerability testing automation can unlock in a realistic enterprise scenario. Every single automatic confirmation saves you time and money – and at an enterprise scale, even very conservative estimates quickly add up to big numbers. See the infographic below to learn how this works and book a no-obligation demo of Invicti to have it work for you.