Are Hackers a Step Ahead? An Analysis using Web Application Vulnerabilities
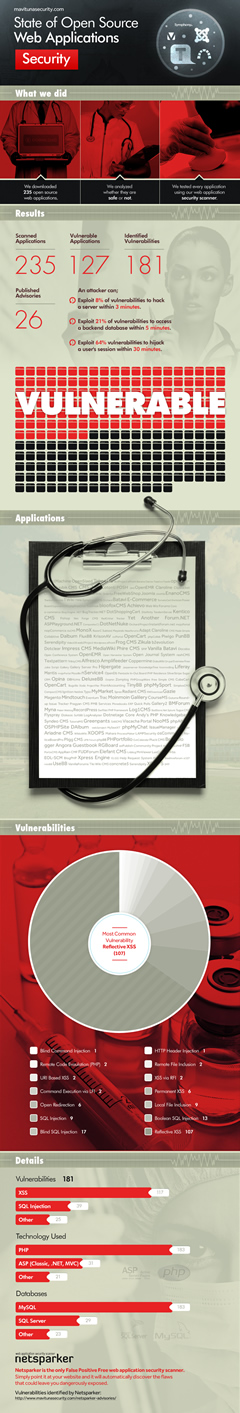
In this analysis the Netsparker team used Netsparker Web Application Security Scanner to scan a number of popular open source web applications and identify vulnerabilities in them. The results are very shocking and explain why malicious hackers are always a step ahead of website owners. A vulnerability statistics infographic was also generated from the results.
Your Information will be kept private.
Begin your DAST-first AppSec journey today.
Request a demoIf you have been involved in the IT industry you’ve definitely heard the myth that hackers are always a step ahead. It seems it is the truth because hack attacks are on the increase. Follow some of the popular IT news websites and you will read about hacked websites and stolen credit card numbers almost on a daily basis. Even if you are a home user, your friendly computer shop technician warned you to stay away from malware, viruses and hackers.
Businesses shifted most of their operations online and now they are depending on websites and web applications more than ever. Hackers know very well that most businesses do not invest in secure development and web application security and they take advantage of such fact and hack them.
I personally do not agree with the myth that hackers are always a step ahead. I think that the IT industry is way behind from where it should be. I am using the results of hundreds of web application security scans performed with Netsparker web application security scanner as an example to show that the IT industry can do much better in terms of security.
Security Scanning of Open Source Web Applications
As part of the quality assurance tests and to improve the web vulnerability detection rate of false positive free web application security scanner Netsparker, our engineers launch thousands of web application security scans throughout the year against test websites. Some of these websites are built using popular open source web applications, such as Joomla, Twiki, Blog Engine .NET and TomatoCart.
What Type of Web Applications were Scanned with Netsparker?
From the below numbers, we can get a better overview of how many open source web applications were tested, with which web application framework they were built and what database backend they use.
- 235 open source web applications scanned
- 183 are built with PHP
- 31 are built with ASP (Classic, .NET and MVC)
- 21 are built from a variety of other web application frameworks
- 183 use MySQL as database backend
- 29 use Microsoft SQL Server as database backend
- 23 use other database backends, such as PostgreSQL etc
Web Application Vulnerabilities in Open Source Web Applications
The results of the web application security scans of 235 open source web applications are quite shocking; 181 unique web vulnerability types were detected in 127 vulnerable open source web applications. Below are some statistics about the discovered web vulnerabilities:
- 107 Reflected cross-site scripting vulnerabilities
- 17 Blind SQL injection vulnerabilities
- 13 Boolean SQL injection vulnerabilities
- 9 SQL injection vulnerabilities
- 6 Persistent cross-site scripting vulnerabilities
- 2 URI-based cross-site scripting
- Other discovered web vulnerabilities were a variety of command injection, command execution, HTTP header injection etc.
Different variants of SQL injection and cross-site scripting vulnerabilities are still the most predominant web vulnerabilities. They sum up to 85% of the reported web vulnerabilities. When you consider that these 2 web vulnerability variants are considered as low-hanging fruits vulnerabilities, and both of them were listed in the OWASP top 10 for the last decade, you would not expect to see them doing better than Lady Gaga does in the music charts!
The Aftermath: We are not Doing Enough to be One Step Ahead
Netsparker web application security scanner discovered both high and critical web vulnerabilities in around 54% of the tested open source web applications. Out of the 181 reported web application vulnerabilities, only 35 were fixed until today (23/04/2013). The other 146 zero-day vulnerabilities in 127 open-source web applications discovered by Netsparker are still not fixed. Therefore any website or blog running on such web application can be hacked since it has known security issues.
Web Application Security is a Must!
The whole point of this article is not to point fingers at someone and nor is to instigate some sort of an endless “open source vs closed source” debate. I am sure that if Netsparker engineers had the opportunity to scan closed source web applications with Netsparker web application security scanner they would still surprise us with the number of vulnerabilities Netsparker would detect.
The whole point is that everyone in the IT industry, from testers and developers to webmasters and executives, still got a lot to learn about web application security if we want to be a step ahead of hackers. Non-profit organizations such as OWASP, the PCI Security Council and security vendors such as Netsparker have been advocating web application security for years and hacking attacks are still on the rise. Unfortunately, many web application development companies and communities from both sides of the globe, businesses and website owners are still not listening to what web application security experts are saying.





