A Detailed Look into the New Features and Improvements of Netsparker Version 3.0
Netsparker Version 3 – By far way better than its predecessors, Netsparker Web Application Security Scanner version 3 makes web application security an easy task and allows web application security experts automate more than ever before. Generate PCI Compliance reports with Netsparker 3.0 to verify your web applications are PCI complaint. Read this blog post for more details of what is new and improved in Netsparker version 3.0.
Your Information will be kept private.
Begin your DAST-first AppSec journey today.
Request a demoFinally Netsparker version 3.0 is soon to be released so stay tuned with us! We have listened to all of your feedback and did our best to add some new cool features. We improved the mechanics of the scanner, added new security checks and fixed a number of bugs. In this blog post we will go through what is new in Netsparker version 3.0. This version is a major update of both Netsparker Standard and Professional editions.
Scan Policy Editor
The Scan Policy Editor can be used to fine tune a scan by defining which web application security tests should be launched against a target web application, thus reducing scan duration time. Newly configured Scan Policies can be saved and used in future web application security scans. For more information on the new Scan Policy Editor and how to create custom Scan Policies refer to the Netsparker Scan Policy Editor post.
PCI Compliance Report
With Netsparker version 3 you can generate PCI compliance reports to check and confirm that your websites and web applications are PCI compliant. The PCI compliance report is mandatory for every website and web application that accepts any form of online payments. Failing to have PCI compliant online payment web systems may result in fines or having them closed down.
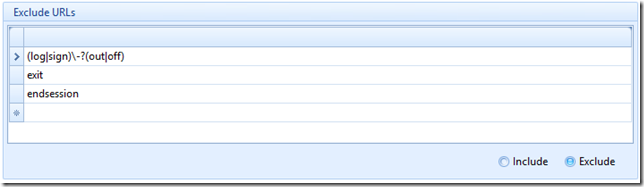
Support for Multiple Exclude and Include Patterns
In previous version of Netsparker one could only specify a single value, which could be a regular expression to match a URL that should be excluded, or included in a web application security scan. In the new version of Netsparker it is possible to add as many matching patterns as you like, as can be seen from the screenshot below.
Knowledge Base Node
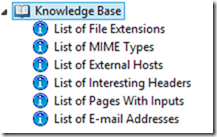 The new Knowledge Base node introduced in this new version of Netsparker will show up in the Sitemap left hand side window as a separate node and will be automatically populated during the web application security scan. The knowledge base node will contain generic information about the target website such as list of different file extensions discovered on target website, list of links that point to an external host, list of external scripts used on the website etc. Even though such information might not be directly related to security issues on the target website, it is still useful to know about such things and keep yourself informed of what is in the target web application.
The new Knowledge Base node introduced in this new version of Netsparker will show up in the Sitemap left hand side window as a separate node and will be automatically populated during the web application security scan. The knowledge base node will contain generic information about the target website such as list of different file extensions discovered on target website, list of links that point to an external host, list of external scripts used on the website etc. Even though such information might not be directly related to security issues on the target website, it is still useful to know about such things and keep yourself informed of what is in the target web application.
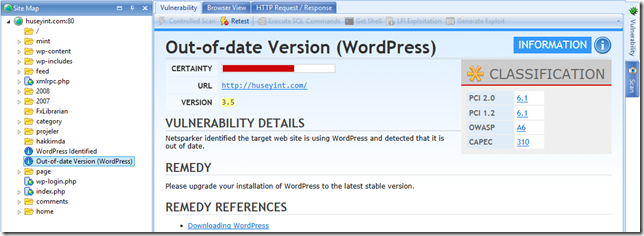
Off the Shelf Web Application Fingerprinting
Off the shelf web applications such as WordPress, Joomla and Drupal are becoming really popular and are being integrated in business web applications. Although these type of well known web applications are very popular, unless they are kept up to date they are prone of getting hacked. The new version of Netsparker includes a new fingerprinting module that automatically detects such kind of well known web applications and alerts you if the version running on the target website is not the latest version and if there are known security vulnerabilities that could be exploited.
Server Side Includes Injection Security Checks
Server side includes allows developers to dynamically include content of another page. It has support for multiple directives, for example it can also be used to execute code. Hence they are prone to some dangerous attacks that can lead to remote code execution or arbitrary file reading. Netsparker version 3 has specific web security tests designed to check if the server side includes on the target website can be injected with malicious code.
Easier to Launch new Web Application Security Scans
Even though Netsparker was already well known for being really easy to use, we went the extra mile and simplified even more the new Start a New Scan interface in Netsparker version. We moved all of the options which are typically left as default to the generic application's settings, such as the number of concurrent connections during a security scan and the enabling or disabling of crawler parsers, which only need to be disabled in very specific circumstances. Launching a new web application security scan has never been easier!
Oracle CHR Encoding and Decoding
The encoder in Netsparker can now also be used to encode any type of input to Oracle SQL Server Char so understanding and fixing of vulnerabilities on web applications which use Oracle server as a database backend servers is now easier than ever before.
Other Improvements and Bug Fixes
Apart from the above noticeable changes that will definitely allow you to be more productive and detect more vulnerabilities in your business web applications, Netsparker version 3 contains a lot more changes and bug fixes which are listed in the Netsparker change log.