BREACH Attack Security Check
Invicti web application security scanners use a wide and ever growing range of security checks to test for vulnerabilities in a scan. The Invicti Standard 5.5 November 2019 Update introduced a new BREACH Attack security check that is enabled by default.
Your Information will be kept private.
Begin your DAST-first AppSec journey today.
Request a demo
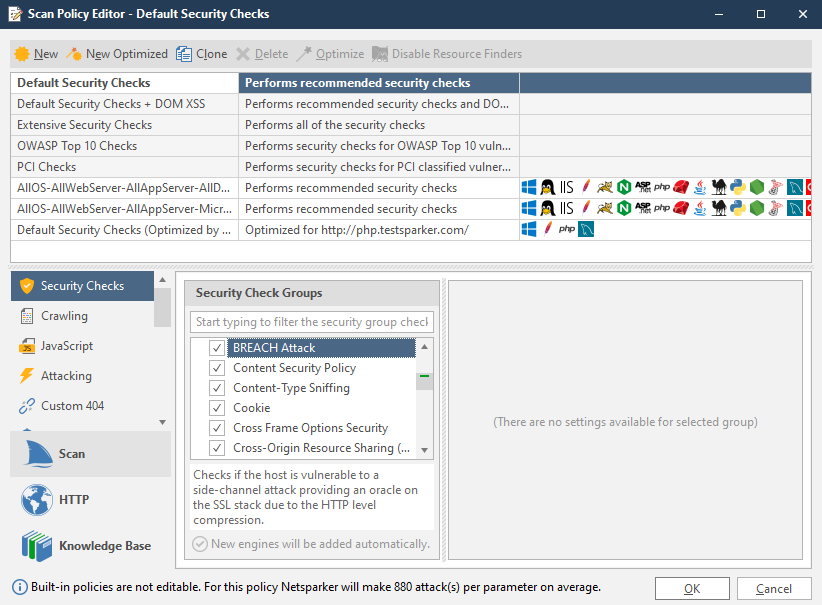
Netsparker uses a wide range of security checks during a scan to test for issues and vulnerabilities. Some are default while others can be modified or deleted. Since the number of hacks and vulnerabilities grows continuously, Netsparker web application security scanner must regularly add to its total list of security checks.
In the recent Netsparker Standard 5.5 November 2019 Update, we have added BREACH Attack to our list of security checks. BREACH Attack (Browser Reconnaissance & Exfiltration via Adaptive Compression of Hypertext) is a Medium Severity Level vulnerability and occurs in SSL/TLS protected connections. Attackers can use it to view a victim’s encrypted traffic and steal information from a website.
In Netsparker Standard, the BREACH Attack security check is enabled by default. It can be disabled and requires no additional settings.