Upcoming changes to Invicti’s teams and permissions feature
We are excited to inform you that a long-awaited redesign of the teams and permissions feature is coming soon to Invicti Enterprise. With this major improvement, you can streamline the process of creating and managing role-based teams.

Limitations of the previous approach
In the past, Netsparker Enterprise provided the ability to add team members with built-in roles only. While you could add as many members as you wanted, the permissions you could assign to them were quite limited and not granular. It was not possible to create multiple teams that precisely suited your needs nor to assign fine-grained roles and permissions to teams or team members.There were also some limitations related to managing member permissions. The older approach did not give administrators a lot of flexibility in assigning roles. For example, you could assign the Start Scans and View Scan Reports permissions to a member of two different website groups. However, it would not be possible to remove that member’s View Scan Reports permission for only one website group – doing so would unassign the Start Scans permission as well. For further information about the current system, see User Permissions Matrix in Netsparker Enterprise.
Introducing role-based access control with granular permissions
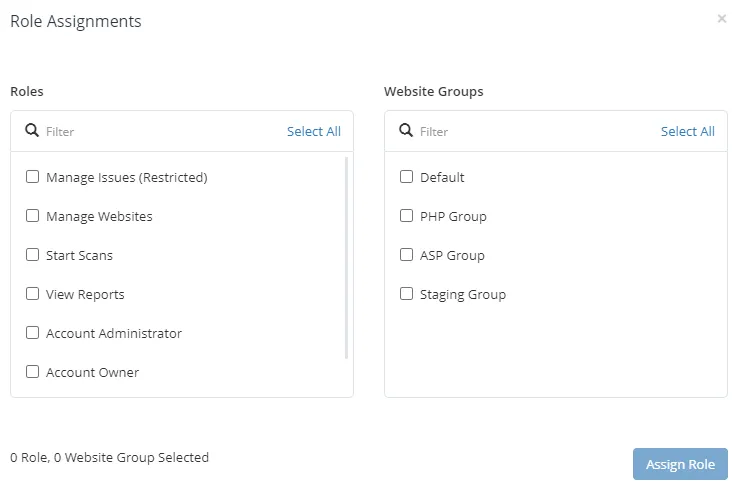
With the new release arriving on June 7th, such limitations will be a thing of the past. Netsparker Enterprise introduces role-based access control to let you pick from a wide variety of granular permissions to create custom roles. There are more than 80 permissions for you to choose from. You can select any combination of these permissions and assign it to a team or member.
To ensure backward compatibility, all existing roles in your Netsparker deployment will be transferred into the new version as built-in roles.
You now have complete freedom to group members and create teams that include only the selected members. Members added to a team inherit the team’s roles, in addition to any individual member roles they may have. You can edit and delete roles and teams at any time.
More flexibility, more options for you
The new feature also lets you create as many teams as you need, so you can align Netsparker team structure to your actual teams and needs. For example, you can set up one team for adding and scanning websites while a separate team manages the issues and vulnerabilities identified in these websites. This makes it much easier to manage teams and members.With the new approach to teams and permissions, you also get much more flexibility and precision in assigning permissions to teams and team members. You can now be as specific as you need when setting up permissions. Going back to the first example, you can now quite easily set up a team with privileges to start scans on website groups A and B but view scan reports only for website group A, not group B.To make it easier to accommodate real-life roles, members can now be part of more than one team (as they often are in reality). A member added to multiple groups will assume the combined roles of all these groups, in addition to any individual privileges.
SCIM 2.0 support
Do you manage your members and teams using identity providers such as Azure AD? The new Netsparker Enterprise release also adds support for the System for Cross-domain Identity Management (SCIM) 2.0 standard to help manage users and user groups in identity providers, including Azure AD and Okta. That way, you can securely automate the exchange of user identity data between your cloud application and any service provider. This streamlines the process of provisioning and de-provisioning of your users into Netsparker.
Experience the future of AppSec




